Edward Snowden is back at it with more claims about government security operations.
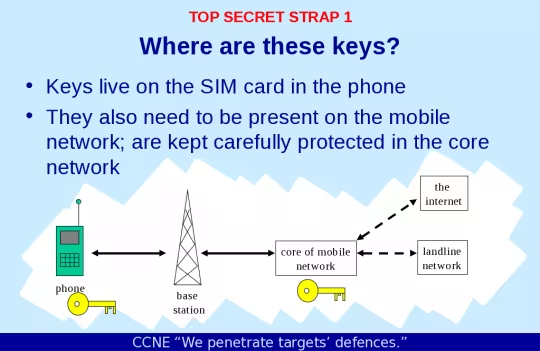
According to documents he provided to The Intercept, American and British spies hacked into Gemalto, the largest SIM card manufacturer in the world, to steal encryption keys for its cards. These keys basically allow mobile communications – both voice and data – to be decrypted without alerting the users, networks or governments of any activity.
It’s analagous to having the keys to a door, instead of trying to break it down.
The hack was performed by a team from the NSA and its British counterpart, the Government Communications Headquarters (GCHQ). Information about the breach was detailed in a 2010 GCHQ document. A joint unit dubbed the Mobile Handset Exploitation Team (MHET), kept secret until now, was formed in April 2010.
Gemalto creates about 2 billion SIM cards a year for AT&T, T-Mobile, Verizon, Sprint and about 450 manufacturers worldwide. Gemalto also produces banking cards, electronic passports, identification cards and other digital security solutions.
According to the report, the stolen encryption keys allow intelligence agencies to monitor mobile communications on respective SIMs without permission from telephone companies. It also sidesteps the need for a warrant or wiretap, and does not leave a trace wireless providers can track.
Furthermore, the key theft allows intelligence agencies to decrypt old communications data the spy organizations had previously acquired but could not decode.
While within the US, the NSA and other American agencies can jsut obtain court orders to force telecom companies to allow them to access customer communications, things don’t usually go so smoothly on foreign soil. So instead of trying to persuade international authorities to provide access or actively hack into devices, the stolen keys could let the NSA monitor devices from anywhere undetected.
In order to access Gemalto’s servers, MHET breached email and Facebook accounts from employees at telecom providers and SIM manufacturers, looking for any information useful to the heist.
Gemalto, for its part, says it had no idea anything was amiss until it was contacted by The Intercept. After setting its security team to look for signs of a breach on Wednesday, it found none.
“I’m disturbed, quite concerned that this has happened,” said Paul Beverly, an executive vice president at Gemalto.”What I want to understand is what sort of ramifications it has, or could have, on any of our customers.”
➤ The Great SIM Heist [The Intercept]
Image Credit: The Intercept
Get the TNW newsletter
Get the most important tech news in your inbox each week.