
The spate of crypto-jacking plaguing the internet shows no sign of slowing down. After infesting hundreds of thousands of routers in Brasil with cryptocurrency mining malware, reports indicate hackers have compromized a further 30,000 routers across India.
As Hard Fork previously reported, black-hat hackers are waging a war on the internet. Attackers have already forced almost 280,000 MicroTik routers in Latin America to mine Monero (XMR) non-stop, so the discovery of the malware running on routers elsewhere is nothing but troubling.
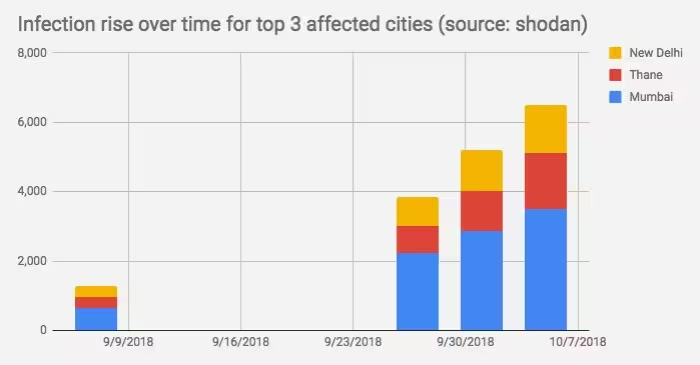
“The number of compromised routers [in India] has doubled in the past month,” wrote internet security unit Banbreach. “For the top three cities with the most infected routers, the growth has been [500 percent].”
Worryingly, it appears internet service providers (ISPs) in India are distributing infected routers, presumably unaware hackers have rigged them to mine Monero on every page passing through their networks.
“I found [CoinHive] in the router provided by my ISP a couple of days ago,” tweeted a security enthusiast from Mumbai. “Probably all the routers used by them are infected and outdated.”
Crypto-jackers favorite tool is CoinHive
CoinHive is a supposedly neutral piece of code enabling browsers to mine cryptocurrency, particularly the anonymity-focused altcoin Monero.
It’s best to think of CoinHive as a tool; charities use it to raise funds indirectly, but here, internet baddies are using it to steal the computing power of unsuspecting users to mine cryptocurrency for themselves.
To complicate matters, hackers are also intensifying efforts by rapidly sharing new, modified versions of their malware in a bid to spread it as quickly as possible.
Data shared by McAfee Labs shows more than two and a half million different versions of crypto-jacking malware (most of it CoinHive related) have been issued in the past three months.
Crypto-jacking succeeds in non-metro areas
Security researchers, like Banbreach and fellow malware-tracking group Bad Packets Report, use powerful search engines to listen to internet traffic. Services like Google only show websites, but those are only a small part of picture.
These detect all the devices on the internet with public IP addresses. As routers fall into that category, it is possible to snoop on some of the traffic passing through them.
Some of the publicly available data relates to its source location. This allows for the mapping of internet traffic.
Researchers grouped populated areas of India into three tiers. One contains the most dense, metropolitan areas, with two and three increasingly remote.
The chart below shows a great disparity in infection rates. Note, there are far more infected routers running in remote areas than in cities; 45 percent of the infected routers in India are in the most rural areas.
Banbreach explained that cybersecurity awareness is “much, much lower in the ‘non-metro’ areas” of India.
To give an understanding of the scope of CoinHive, related studies suggest the total output of all the machines running CoinHive scripts generates more than $250,000 in XMR every month – although remember, not all of it comes by way of crypto-jacking.
If it helps – the hackers are primarily exploiting vulnerabilities in MicroTik brand routers. If you have one, refer to the manufacturer for an official patch.
As well, here is a handy guide on how to best protect your browser against crypto-jackers.
If you’re interested in everything blockchain, chances are you’ll love Hard Fork Decentralized. Our blockchain and cryptocurrency event is coming up soon – join us to hear from experts about the industry’s future. Ticket sales are now open, check it out!
Get the TNW newsletter
Get the most important tech news in your inbox each week.





