Microsoft is investigating a new remote code execution vulnerability in Microsoft Word. The company has issued a security advisory after confirming reports that the flaw is being exploited as part of targeted attacks against Word 2010.
The company has found that the vulnerability affects all supported versions of Microsoft Word. The flaw in question makes remote code execution possible if you open a specially crafted RTF file using an affected version of Word, as well as if you preview or open a specially crafted RTF email message in Outlook while using Word as the email viewer (Word is set as the default email viewer in Outlook 2007, Outlook 2010, and Outlook 2013). Doing either could allow the attacker to gain the same user rights you have, meaning if your account is configured to have fewer user rights you could be less impacted than if you have an administrator account.
While we wait for a patch, which Microsoft has not provided a date for (April’s Patch Tuesday is possible, but it will likely come in May), the company is offering the following workarounds and mitigations:
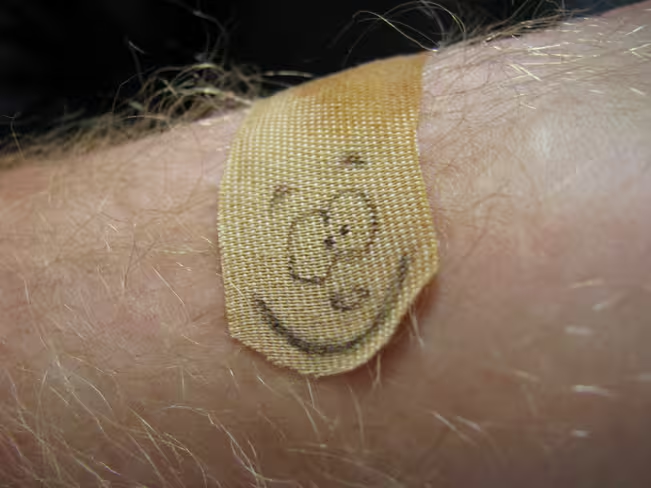
- Apply the Microsoft Fix it solution “Disable opening RTF content in Microsoft Word.” This temporary fix configures the Microsoft Office File Block policy to prevent the opening of RTF files in supported versions of Microsoft Word.
- Read emails in plain text: To help protect yourself from the email attack vector, read email messages in plain text format. Outlook 2003, Outlook 2007, Outlook 2010, and Outlook 2013 all provide such an option.
- Use Microsoft Office File Block policy to prevent the opening of RTF files in Word 2007, Word 2010, and Word 2013.
The first option can be enabled and disabled on the fly. The second and third options require a bit more effort. Still, all are valid until a patch is available to plug the security hole for good.
Top Image Credit: Nate Brelsford
Get the TNW newsletter
Get the most important tech news in your inbox each week.