While Mac malware tends to be a rather rare occurrence, Ars Technica reports security researchers have discovered two separate, new macOS viruses that rely on old Windows tricks to get into your laptop and steal your data.
One of the attacks, documented by software firm Objective-See, exploits an established Windows technique which hides and executes malicious code using Word document macros.
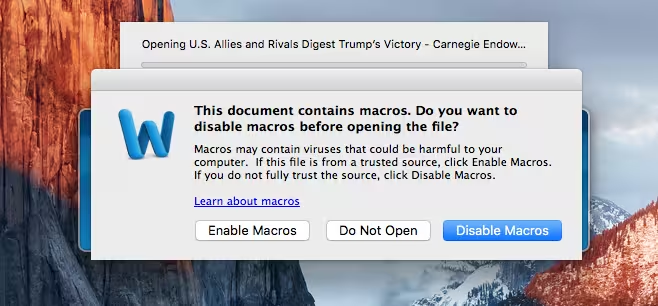
The hack tricks unsuspecting users into opening infected Word documents which subsequently run malicious macros once the file has been loaded. The good thing is that it’s fairly easy to identify infected files prior to opening them.
Anytime you open a Word file containing macros, your device will ask you for permission. Denying permission on its own is enough to prevent the malware from spreading.
But if you click ‘run’, all sorts of bad things could happen: A hacker could spy on you or pull your browsing history, or they could initiate a secondary infection by downloading additional malware.
More macOS malware
While also inspired from older Windows exploits, the other recently found malware – uncovered by researchers from Iran Threats – appears to be slightly more advanced.
Unlike the previous example, which used an infected Microsoft Word document as its attack vector, this one is merely disguised as a legitimate application.
The virus essentially prompts users to download and install a fake software update. It then proceeds to harvest the user Keychain and phish for usernames, passwords as well as any other credentials, before eventually relaying the recovered data back to the attacker.
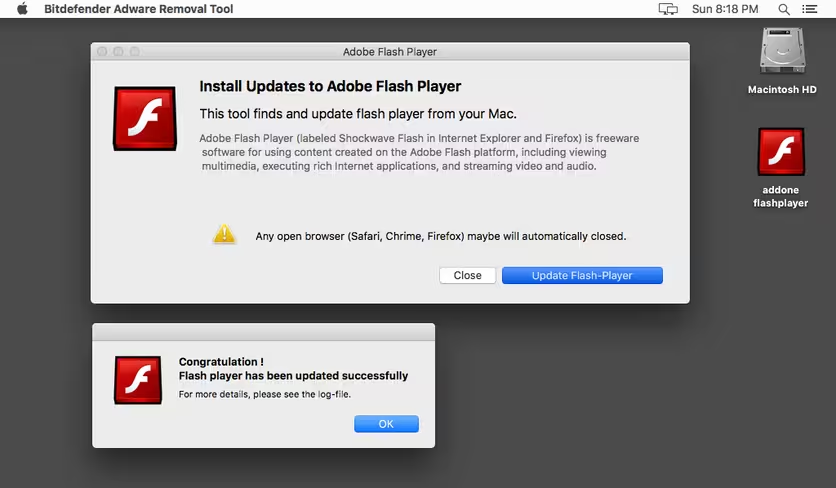
The best way to avoid this attack is to simply refrain from downloading software from third-party or untrusted websites. The safest route is to download updates straight from the App Store or simply from the official website of the app-maker in question.
While exploits for macOS are still mostly a rarity, Apple has dealt with a litany of bugs and glitches for iOS in recent months.
Not too long ago, numerous iOS users reported their devices had frozen after a malicious three-second video spread on the internet. In another similar case, thousands of users reported experiencing unexpected shutdowns after trolls discovered a glitch in iOS that could crash any device by just sending a short text message.
Get the TNW newsletter
Get the most important tech news in your inbox each week.