Did you #DeleteFacebook in 2018? Caring about our online privacy might be popular right now, but on a wider level, it’s not as easy as we think to escape the hole we’ve dug ourselves into.
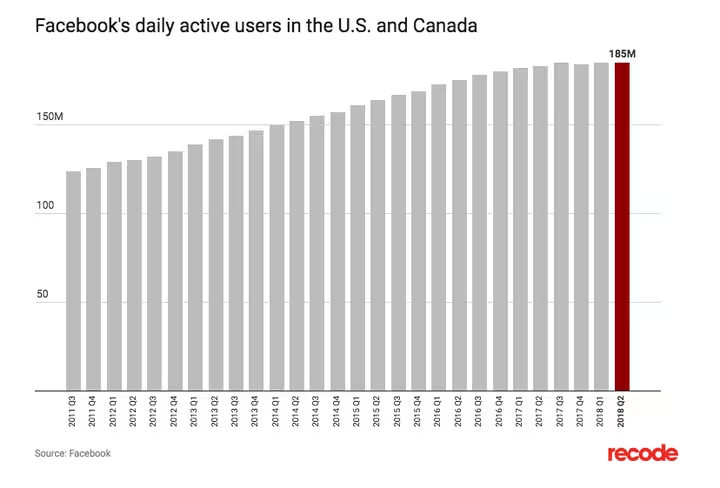
Don’t believe that this is more of a trend than a turning point? Just look at the difference between hype and action. Despite 26 percent of Pew poll respondents saying they’ve deleted the Facebook app, the company’s user stats have stayed essentially the same.
And even if we were deleting our Facebook accounts en masse, would it be anything more than a symbolic gesture in terms of our own online privacy?
Sadly, the answer looks bleak. Many of us have been handing over our personal data for years without paying much attention. Our Facebook accounts are just one scene in story the of our online privacy nightmare.
And while we’ve all been distracted by the story playing out on the main stage, there have been several other plot lines happening alongside it.
Facebook’s not in a unique situation
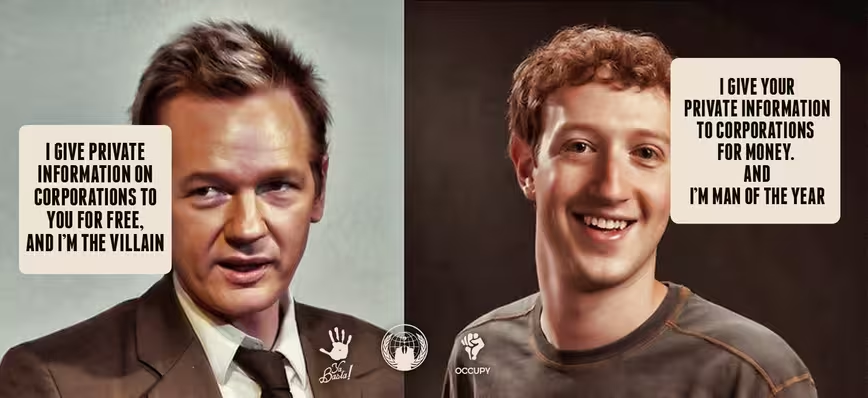
Consumers and the industry alike spent the year calling out Facebook for the amount of data the platform has amassed on its users, and what the company does with it. But Facebook’s not in a unique situation.
Okay, so perhaps no other social media networks are as closely associated with election tampering.
And only a few other tech companies were called before Congress this year.
But that’s not because they’re the only companies with risky data and security practices. They’re simply a few of the largest, and therefore great candidates to make examples out of. Facebook may be especially irresponsible with how it handles our data, but the way non-tech media portrays users as clueless pawns being conned out of personal info is far from the truth.
Even if you do decide to go cold turkey on your daily injection of dopamine from Facebook’s flagship product, what about Messenger, Instagram, and WhatsApp? Are there even viable alternatives for those services, which are owned and operated by Zuck and co?
Sure, there haven’t been as many high-profile hacks and breaches of these products as those suffered by Facebook itself, but there’s plenty of evidence suggesting that evil trolls are even more active on Instagram.

But hacks, breaches, misinformation and toying with our emotions aside, it’s our own desensitization towards sharing that really needs to change.
There’s a simple fact that we often overlook when talking about Facebook data scandals. We hand that data over willingly. Very willingly.
Cambridge Analytica and other “evil actors” were hardly stealing users’ info covertly. The bad behavior started after they obtained it. Facebook users (and users of so many free services) have long been eagerly pressing “grant permission” and similar buttons without reading the fine print. This has given companies like Cambridge Analytica access to whatever they needed.
They were exploiting rules and behaviors that never made sense in the first place, but that we never stopped to question or think about.
Instead, we all rushed to share our latest personality quiz results and didn’t pay attention to what permissions we were granting. We invited our friends to play games for more virtual coins without considering everything we were inviting them into.
And we posted about our plans, feelings and experiences. A lot.
Our own willful ignorance extends well beyond Facebook, and multiple companies are taking advantage of to this day. In ways that mean we’re all probably still at risk – regardless of whether you deleted Facebook.
Other everyday sites and services are after you
Just like Facebook has third parties and vendors exploiting it and its users, so do so many other sites and apps you use every day.
Facebook is just a favorite to point fingers at, possibly thanks to the “If you aren’t paying for it, you are the product” concept, which we can all have incensed #mindblown reactions to. But this concept is hardly specific to Facebook or even social media. It’s actually an iteration of concepts explored in a 1973 art film called Television Delivers People about the dangers of broadcast media.
Think you’re exempt because you’re a cord cutter and you pay your way with a Netflix subscription? Nope – you’re still a pair of eyeballs that can be monetized.
Netflix might not (yet) be trying to earn more from you than they can with a monthly subscription fee, but what about services where the end goal is consumerism itself? Even of Amazon exists – in your mind, at least – as a platform for convenient shopping, it’s also a major ad platform.
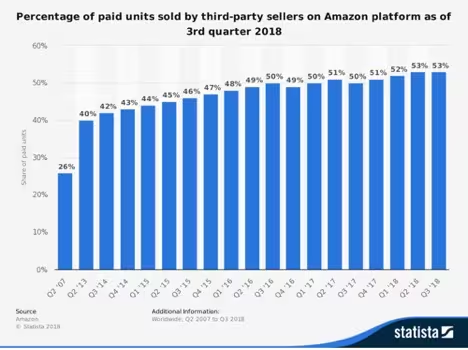
Just remember that as of 2017, more than half of the goods sold on the marketplace were from third-party sellers.
And unfortunately, we can’t trust those third parties as quickly as most shoppers do. This year alone saw over a million new sellers enter the Amazon marketplace, and not all of those sellers are running their businesses with the due diligence expected of an international brand. And they’re unknowingly giving too much data to other services, just like in the case of Facebook and Cambridge Analytica.
The majority of China-based Amazon sellers use local third-party tools for extra business services like payment processors and fulfillment companies.
Some of these third parties take advantage of merchants’ lack of knowledge and request their secret key to access the Marketplace Web Services API instead of the developer ID path that’s supposed to be used.
Sellers, in the meantime, willingly hand over access to the data not knowing the wiser, just like users on Facebook. And similar to the Facebook security loopholes, the Amazon API problem impacts more than just the individual who forgot to read the fine print. Once a seller hands over their secret key, the processor gains access to loads of personal data, including shopping history.
With these processors building major monetize-able assets in the form of private transaction data, they don’t need to charge merchants reasonable transaction fees, which means they can provide a “cheaper” service than mainstream fintech from the West, thereby attracting sellers unaware. But Amazon itself doesn’t seem interested in doing anything about it.
It’s time to take action
Even if you don’t shop at Amazon and have indeed deleted your Facebook account, your data’s not safe.
For example, did you get a 23andme or similar genealogy test for the holidays? The security breach of a DNA testing service in June pointed out the danger of sending DNA off to tech companies. With data privacy regulation so inadequate in most countries and health privacy laws that haven’t caught up with technology, that’s instilling a lot of trust in these companies.
And unearned trust is what many of these examples to come down to. Because we rarely stop and think of the implication of clicking “I accept the Terms of Service” before doing so.
It’s time to start.
We’ve reached a point where the evidence of misconduct is all around us. It’s on the social networks and shopping sites we visit, and too many of the other services we use as well. It’s too prevalent to pretend to ignore.
As an industry, we need to deal with the bad actors.
Center for Humane Technology Co-founder Aza Raskin recently discussed some of these issues in his “How to Create Human Protective Technology” presentation at the Slush conference in Helsinki.
If there once was a time when the tech industry and end users could ignore the pitfalls of under-vigilant data privacy, that time is now history. The trust we once had can probably never be re-established.
It’s not enough to address individual exploiters as they pop up, as it’s happening too frequently. We’ll never be able to chase wrongdoers down faster than new ones will arrive. We need to address the systems allowing them to exploit us, our customers, and our data.
Get the TNW newsletter
Get the most important tech news in your inbox each week.