It looks like Lenovo has been installing adware onto new consumer computers from the company that activates when taken out of the box for the first time.
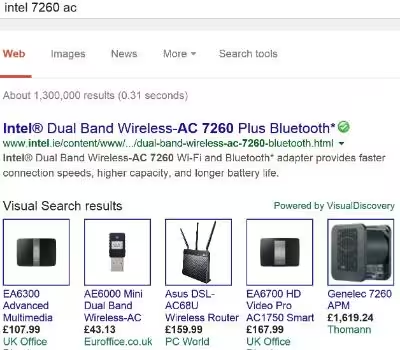
The adware, named Superfish, is reportedly installed on a number of Lenovo’s consumer laptops out of the box. The software injects third-party ads on Google searches and websites without the user’s permission.
Superfish appears to affect Internet Explorer and Google Chrome on these Lenovo computers.
A Lenovo community administrator, Mark Hopkins, wrote in late January that the software would be temporarily removed from current systems after irate users complained of popups and other unwanted behavior:
We have temporarily removed Superfish from our consumer systems until such time as Superfish is able to provide a software build that addresses these issues. As for units already in market, we have requested that Superfish auto-update a fix that addresses these issues.
Hopkins defended the adware, saying that it “helps users find and discover products visually” and “instantly analyzes images on the web and presents identical and similar product offers that may have lower prices.”
He also says that users can refuse the terms and conditions when setting up their laptop, which means the software will be disabled. It doesn’t sound that straight-forward, however.
Lenovo installs a MITM cert and proxy called Superfish, on new laptops, so it can inject ads? Someone tell me that's not the world I'm in.
— Mike Shaver (@shaver) February 19, 2015
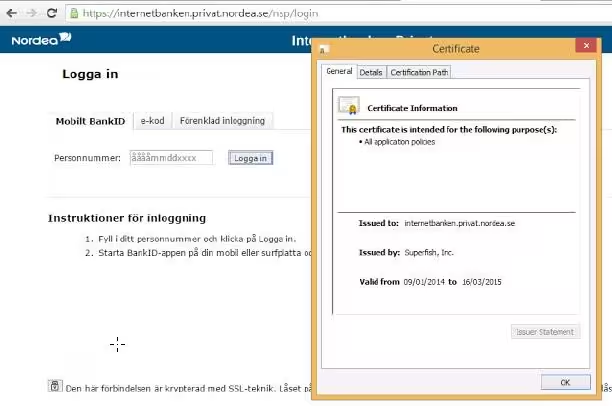
Other users are reporting that the adware actually installs its own self-signed certificate authority which effectively allows the software to snoop on secure connections, like banking websites as pictured in action below.
This is a malicious technique commonly known as a man-in-the middle attack, where the certificate allows the software to decrypt secure requests, yet Lenovo appears to be shipping this software with some of its products out of the box.
If this is true — we’ve only seen screenshots so far — Superfish could be far more dangerous than just inserting advertising.
Superfish is identified by antivirus products as adware and advised to be removed. One user created a video that details how to remove the software manually, for those that are affected.
Even though Hopkins says the company has stopped installing the software on computers, it appears that’s only “temporary” until the company behind the software makes some tweaks to stop pop-ups.
Reports of Superfish being pre-loaded on Lenovo computers have appeared on forums as early as mid-2014.
If this is as widespread as it appears to be, the news is not good for Lenovo computer owners. If you own a Lenovo machine, let us know in the comments if you find the Superfish software on your machine.
We’ve contacted Lenovo for comment on the Superfish software and will update when we hear back.
Read Next: Lenovo’s bundled adware also comes with a worrying security hole
Update: Mozilla Firefox does not appear to be affected by the SSL man-in-the-middle issue, because it maintains its own certificate store.
Update 2: Lenovo contacted us with the below statement and says that it has disabled the Superfish software and will not bundle it in the future. The company did not, however, respond to the root security certificate flaw and does not appear to have fixed it.
“Superfish was previously included on some consumer notebook products shipped in a short window between September and December to help customers potentially discover interesting products while shopping. However, user feedback was not positive, and we responded quickly and decisively:
1) Superfish has completely disabled server side interactions (since January) on all Lenovo products so that the product is no longer active. This disables Superfish for all products in market.
2) Lenovo stopped preloading the software in January.
3) We will not preload this software in the future.
We have thoroughly investigated this technology and do not find any evidence to substantiate security concerns. But we know that users reacted to this issue with concern, and so we have taken direct action to stop shipping any products with this software. We will continue to review what we do and how we do it in order to ensure we put our user needs, experience and priorities first.
To be clear, Superfish technology is purely based on contextual/image and not behavioral. It does not profile nor monitor user behavior. It does not record user information. It does not know who the user is. Users are not tracked nor re-targeted. Every session is independent. Users are given a choice whether or not to use the product. The relationship with Superfish is not financially significant; our goal was to enhance the experience for users. We recognize that the software did not meet that goal and have acted quickly and decisively.
We are providing support on our forums for any user with concerns. Our goal is to find technologies that best serve users. In this case, we have responded quickly to negative feedback, and taken decisive actions to ensure that we address these concerns. If users still wish to take further action, detail information is available at http://forums.lenovo.com.”
Update 3: A developer has created a website that helps Lenovo owners quickly check if they’re affected by the root security certificate and offers suggestions on how to fix if they are.
Update 4: Lenovo has released detailed instructions on how to fully remove Superfish from affected systems.
Top Image credit: 360b / Shutterstock.com
Get the TNW newsletter
Get the most important tech news in your inbox each week.