
There’s a blockchain bandit on the loose – and they’ve already thieved over $6.1 million worth of Ethereum.
According to a report published by security consulting firm Independent Security Evaluators (ISE), an unknown entity has been bypassing weak private keys to swipe large amounts of Ether.
The findings show that during last year’s price rally, the stolen funds amounted to over $54 million (roughly 38,000 ETH).
As part of its investigation, ISE looked at several weak private keys, starting with simple key combinations and soon realised that associated wallets had been funnelled.
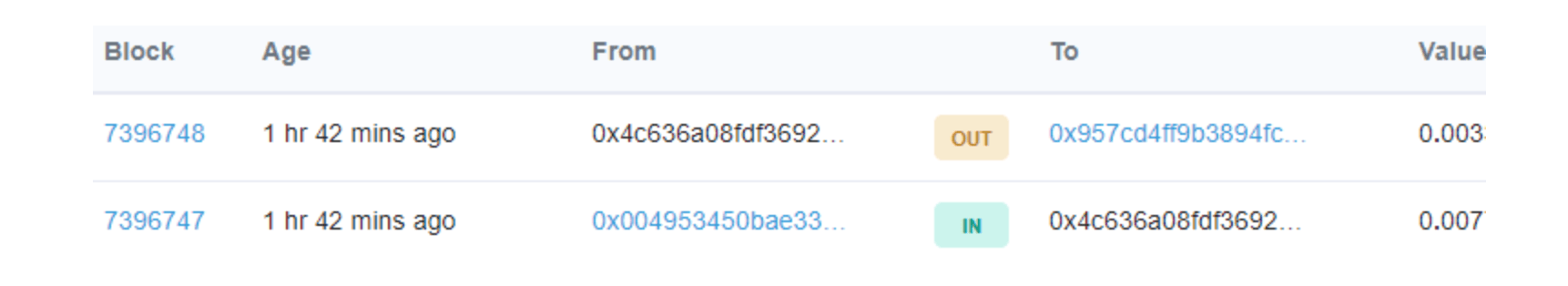
To determine the speed at which the thief was working at, researchers sent $1 in ETH to the address linked to one of the weak private keys and realised that it was “instantly” sent to another account.
“We discovered that funds from these weak-key addresses are being pilfered and sent to a destination address belonging to an individual or group that is running active campaigns to compromise/gather private keys and obtain these funds,” said the researchers.
“Blockchainbandit” as the culprit is known, is now thought to hold some $6.1 million (44,744 ETH).
“Whoever this guy or these guys are, they’re spending a lot of computing time sniffing for new wallets, watching every transaction, and seeing if they have the key to them,” ISE researcher and analyst Adrian Bednarek told Wired.
For context, private keys are a string of data, which in the cryptocurrency world, allow users to transfer funds from their wallet addresses.
The keys need to be protected at all times to avoid them becoming compromised, and to stop nefarious actors from accessing and stealing associated funds.
In this instance, weak keys could have been generated in various different ways. Researchers say they could potentially derive from a coding error which truncated what should have been a longer – and more secure – data string.
“While it is improbable that a weak key would ever be generated under legitimate circumstances using the appropriate code paths, we hypothesized that weak private keys may still be generated by coding mistakes, or operating system, device, and execution environment errors, and that these issues are common,” the report reads.
The researchers were unable to determine the thief’s identity but Bednarek told Wired he “wouldn’t be surprised if it’s a state actor, like North Korea, but that’s all just speculation.”
At the same time, it’s also worth noting that the researchers have not yet identified which wallets are associated with the weak keys, stating only that they’d been emptied.
Some question marks remain but one thing’s for sure: if the stolen funds are withdrawn and find themselves coming into the real world, the mastermind behind this criminal operation is likely to find themselves in hot water.
Did you know? Hard Fork has its own stage at TNW2019, our tech conference in Amsterdam. Check it out.
Get the TNW newsletter
Get the most important tech news in your inbox each week.





