This year, NetGalley, the website that provides advanced e-copies of books to reviewers, sent its season’s greetings in a different tone. In an email to its users before Christmas Eve, the company declared: “It is with great regret that we inform you that on Monday, December 21, 2020 NetGalley was the victim of a data security incident.”
According to the company’s advisory, “What initially seemed like a simple defacement of our homepage has, with further investigation, resulted in the unauthorized and unlawful access to a backup file of the NetGalley database.”
The database in question included sensitive user information, including usernames and passwords, names, email addresses, mailing addresses, birthdays, company names, and Kindle email addresses.
Unfortunately, many users took to social media and started discussing the incident without thinking about what they are putting up for everyone to see. And in their haste to be the first to tweet about the breach, many users made awful mistakes, which could further compromise their security.
The following is perhaps the worst way to tweet about the incident. The user admits using his NetGalley password for several other accounts.
While that tweet might have been a joke, this next one certainly isn’t. The user posted an image of the NetGalley advisory email that contained her full name (covered in image). Since the Twitter account name is pseudonymous, the user just revealed the full name of the person behind it.
There were other milder tweets, in which users admitted that their NetGalley account wasn’t under their real name. Less dangerous tweets were by users who admitted they had a NetGalley account, and they had just learned of the hack and had either changed their password or deleted their accounts.
At first glance, many of these tweets might look harmless because NetGalley doesn’t store very sensitive information such as bank account and credit card data. But the NetGalley breach was already bad, to begin with.
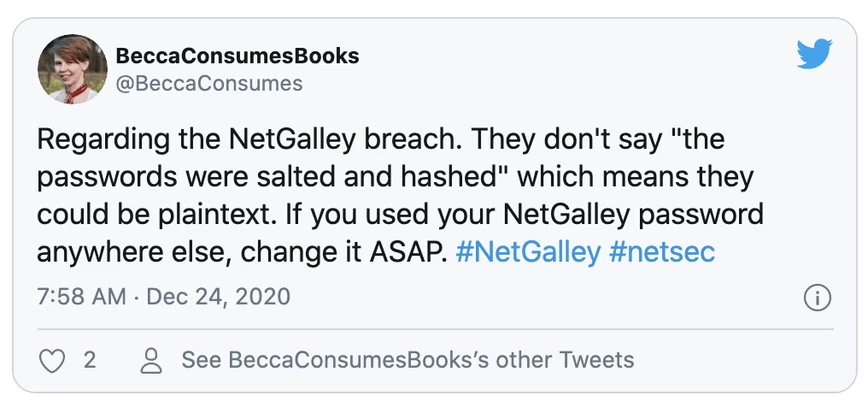
When revealing security breaches, most companies explicitly state the measures they have taken to protect users’ data. For instance, many organizations quickly point out that leaked passwords were encrypted or hashed, which makes it hard (but not impossible) for the attackers to access the accounts. There is no mention of encryption in neither the original advisory nor the updated version published on NetGalley’s website on Sunday, which suggests the hacked database stored user passwords and other information in plain text.
[Read: ]
On December 23, when NetGalley sent the first advisory, the company invalidated all login credentials and notified users that they will have to reset their passwords the next time they try to log in. But by then, the damage had already been done. The hackers defaced the website on December 21, as users had pointed out on Twitter and the company confirmed in the advisory. And there’s nothing to prove they didn’t have access to the data much sooner.
Even if the company had invalidated passwords before the attackers had the chance to use them, the data would still be valuable to them. As the first tweet I shared suggested, users often reuse their passwords across many accounts. After the NetGalley hack, the attackers have access to a fresh list of emails and passwords. They can use this information in credential stuffing attacks, where they enter the login information obtained from a data breach on other services and possibly gain access to other, more sensitive accounts. Cross-service account hijacking is something that happens often and can even include high-profile tech executives.
The attacks can also combine the data from the NetGalley breach with the billions of user account records leaked in other data breaches to create more complete profiles of their targets.
So, alone, the NetGalley data breach might not look like a big deal. But when viewed in the context of other security incidents and the growing sophistication of cyberthreats, every piece of information that falls into the hands of malicious actors can become instrumental to a larger attack.
Some users have dismissed the hack as harmless. As one user said, “What’s the worse [sic] that can happen, somebody gonna write a review posing as me?”
The real answer is, “No, the worst that can happen is that some threat actor can use your data and all the other public information they can gather about you, and use them to attack you from another, more sensitive spot.”
To be clear, this doesn’t mean you shouldn’t tweet about data breaches. In fact, I found plenty of good information about the data breach on Twitter, like this user who first raised concern about the leaked data possibly being unencrypted…
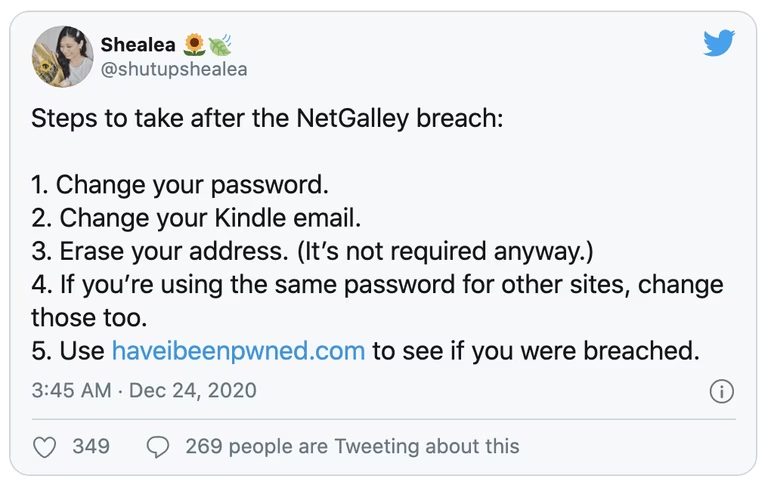
… and this other tweet that shared some decent tips.
It’s also fine to criticize the way the company handled the breach, though I would advise against spreading conspiracy theories that would only add to the confusion.
But in general, you must be very careful when posting information on social media about data breaches. So, before posting about a security incident, stop and think twice. If what you’re about to share reveals any personal information about you or someone else, such as services you’re using, your devices, email address, location, and IP address, then resist the urge to post something witty to your followers. It’s not worth it.
The point is, the dark web is already replete with sensitive information about billions of users. Don’t make things worse by revealing more information about yourself and others through careless tweets.
This article was originally published by Ben Dickson on TechTalks, a publication that examines trends in technology, how they affect the way we live and do business, and the problems they solve. But we also discuss the evil side of technology, the darker implications of new tech and what we need to look out for. You can read the original article here.
Get the TNW newsletter
Get the most important tech news in your inbox each week.