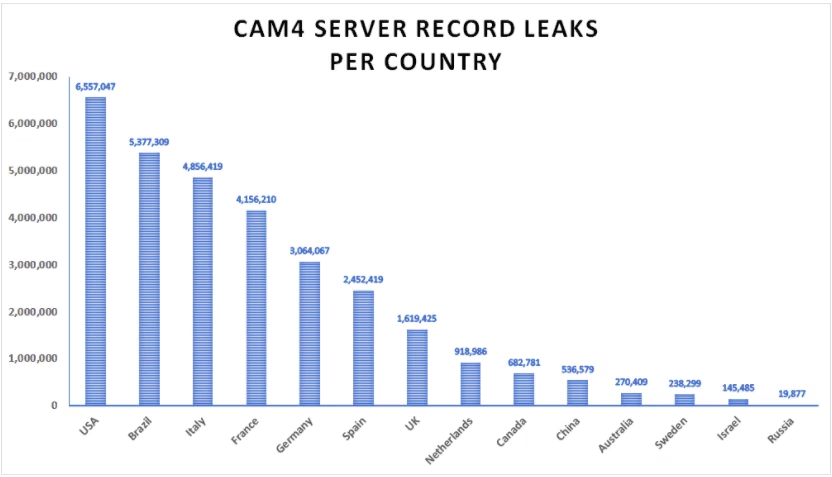
Adult live-streaming site CAM4’s unprotected database exposed millions of personally identifiable records including names, emails, user conversations, payment logs, and IP addresses dating back March, according to a worrying report that’s just been published.
The 7TB database was found by a team of researchers from Security Detective, a site focusing on security incidents and tools. The team’s lead researcher, Anurag Sen, said it had more than 10.88 billion records that included server logs, password hashes, and customer information. The production log dated back to March 16.
[Read: Facebook-backed Jio leaked trove of coronavirus app data because it didn’t have a password]
The team found 11 million email IDs, more than 26 million password hashes, and hundreds of records uncovering full names, credit card type, and paid amounts.
The database also contained details such as username, gender preference, sexual orientation, IP addresses, device information, transcripts of email correspondence, user conversations, and chat transcripts between users and CAM4.
Plus, it had information related to fraud and spam detection, giving a peek into the site’s security practices.
The research team noted that the availability of fraud detection logs “enables hackers to better understand how cybersecurity systems have been set up and could be used as an ideal verification tool for malicious hackers, as well as enabling a greater level of server penetration.”
Cybercriminals can use this data to target emails to extort money or for spear-phishing attacks. This is a highly sensitive issue for adult sites as most members prefer to stay anonymous. In 2015, a data hack on a hack on Ashley Madison, a website that connected potential adulterers with each other, exposed the personal data of 37 million users. Later, attackers targeted these customers and their spouses to demand money using the threat of blackmail.
While the database error has been plugged now, it’s not known if any hackers accessed the information.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




