Subgraph OS launched in public alpha at the weekend’s tech and democracy-focused Logan CIJ Symposium and got an endorsement from Ed Snowden – stamping it with some promise that it could be our future answer to an insecure online world.
“The internet is more hostile than its ever been,” the company’s president David Mirza Ahmad warned TNW.
“There are of course governments, law enforcers and intelligence agencies, but it’s not just state agencies using software vulnerabilities to implement malware systems for the purpose of surveillance, data infiltration or lateral pivoting.
“When people get compromised, it’s always this style of attack: you get sent an email with an attachment that exploits a software vulnerability in Microsoft Office or an email client or an image viewer that allows code to run and installs a remote access tool – a trojan horse – to steal documents.
“Subgraph is addressing that problem.”
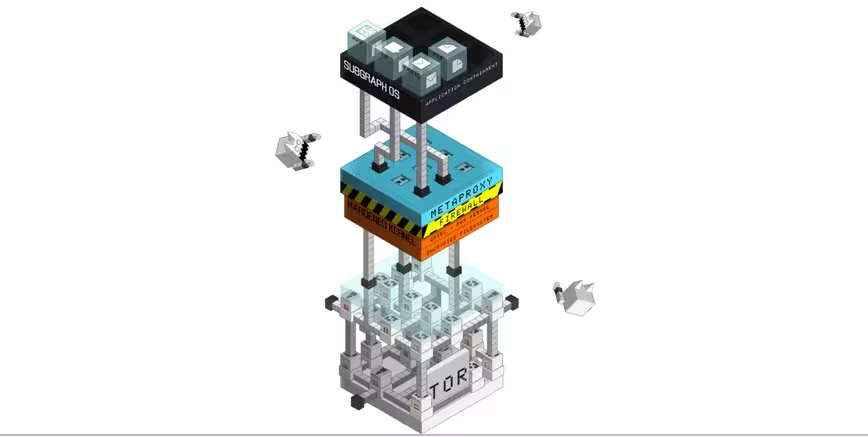
The OS is based on Linux, features the Gnome user interface and includes security experts’ favorite part of the kernel, grsecurity, which doesn’t usually come as standard.
Many newer secure systems by the likes of Apple and Microsoft are built on the innovations found in this.
Jail cells
At a low level, Subgraph creates “jail cells” around different applications so that those that do not need to be exposed to the network or do not need to be able to access certain features are simply isolated from doing so. This is designed to prevent something like a malware-laden PDF opening the backdoor to your whole computer.
“We want to remove the security decisions that the user has to make by providing a holistic end-to-end OS,” he explains.
“Rather than having to ask which chat tool you should use, we’re curating applications, based on our assessments, so that users are equipped with the best tools, all integrated within the OS.”
A notoriously open bunch, the company has already worked to bring a Tor-friendly chat client written by their friends at Thoughtworks, called Coy, onto Subgraph.
But, where Linux has often been accused of lacking, Ahmad says a nice user interface will also be crucial for the OS’ success too.
“Security developers and privacy developers get a lot of criticism for focusing on the geeky, cool stuff – but we know that stuff will never get used unless it’s put into something that’s familiar.
“The longterm goal is that it can be used by anyone, and include things like a new secure email client, secure IM, so we’re working on tools for everyone that just have security built in.”
Reproducible builds
The team is also putting a lot of effort into forwarding the idea of “reproducible builds,” a way to use the source code of open-source software to ensure it’s what it claims to be.
“The Debian project, which is what we’re based on, is doing really great work in reproducible builds. It’s what I call open-source++ meaning a better and more verifiable way to do open source software.”
Ahmad explains that companies like Google are actually using similar sandboxing technology to Subgraph. “They’re doing really good work, all of them, but it’s not open-source, it’s not free.”
Having spent six years working as a swat team of security experts, and being self-sufficient in that regard, Subgraph is now backed by the US government’s Open Technology Fund – which has also handed money to Tor, Tails and Open Whisper Systems, the team behind Signal.
But, of course, when asked about that ongoing encryption debate in the US, Ahmad said: “We need strong crypto even for basic commerce. It’s important to make sure that bad laws get fought.”
Subgraph is awaiting a security audit and its beta is still six months away, with a full product unlikely to emerge before the end of the year. But the company is looking for people with a bit of knowhow, who aren’t expecting security or stability, to come and try it out now.
➤ SubGraph
Get the TNW newsletter
Get the most important tech news in your inbox each week.