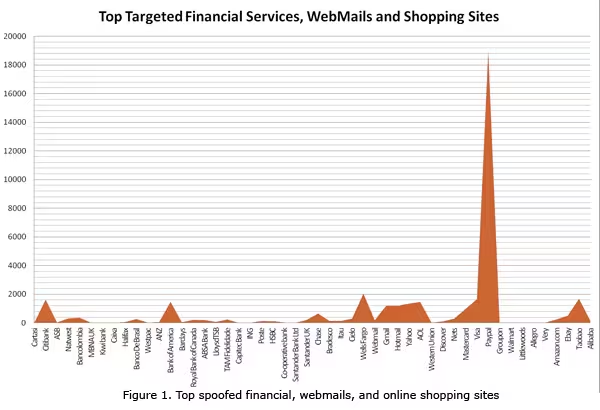
What was the most phished website during the 2012 holidays? If you thought it was a bank, you’d be pretty close; it was actually PayPal, which saw nine times more phishing sites than the next closest victim. Seriously: it was the only company that saw spoofed sites in the five figures.
The new figures come from Trend Micro, which notes that while online shopping is certainly convenient, it poses a much greater security risk than physically going to a store, at least when it comes to criminals looking to steal your personally identifiable information. The company identified the top created phishing sites for December 2012. Here is the result:
The first table lists the top 10 most spoofed sites, which are all financial: aside from PayPal, the list includes banks and credit card companies. The second table lists the top four email account providers and the third features online shopping/auction/deal of the day sites.
PayPal saw 18,947 spoofed sites under its belt. Trend Micro says it was “followed closely by the American bank Wells Fargo” but we completely disagree. In fact, this graph of 50 popular brand names better shows how much more PayPal is targeted:
Users tricked into visiting spoofed sites often have their systems infected with malware. This past holiday season, those visiting the fake PayPal sites (mainly from Taiwan, Thailand, and the US) were infected with TROJ_QHOST.EQ, while those visiting Citibank phishing pages (usually from Japan and the US) were infected with WORM_CRIDEX.CTS, a threat known to steal sensitive data like online banking credentials, as well as TROJ_CDOWN.A, SWF_BLACOLE.BBB, JAVA_DLOADR.XM and WORM_CRIDEX.EZ respectively.
Trend Micro offered some advice on remaining vigilant against phishing attacks, especially during the holidays and other special occasions:
- Spoofed email messages usually contain generic greeting and not addressed to the recipient.
- Legitimate email notifications do not contain glaring grammatical errors, typos, and formatting gaffes.
- Spoofed emails have an “alarmist” tone, usually urging users to click a link or divulge personal information.
Generally speaking, don’t open attachments or click URLs even if they appear to come from seemingly known sources. If you need to click, read the message body thoroughly and make a habit of copying the shortcut link and checking its legitimacy before going to the page.
Image credit: Pierre Amerlynck
Get the TNW newsletter
Get the most important tech news in your inbox each week.