Last year, Apple expanded its security bounty program to include macOS after several years of offering the same for iPhone developers. But according to at least one researcher, the company isn’t acting quick enough on some exploits.
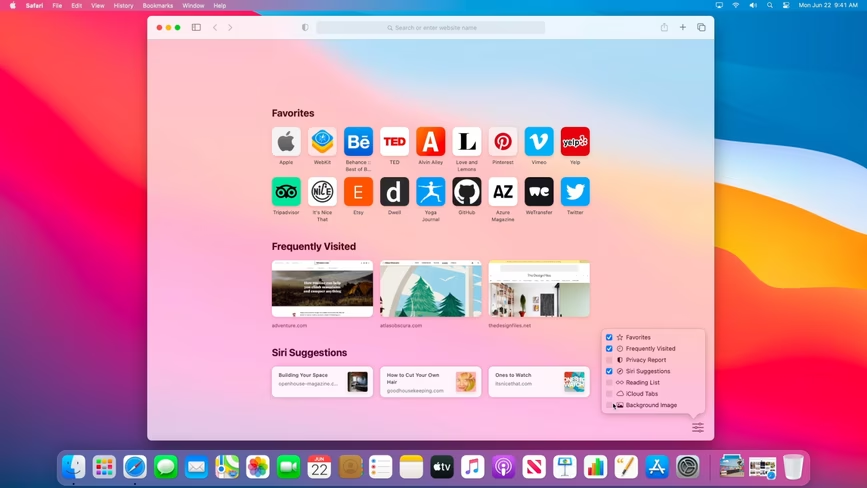
Developer Jeff Johnson informed Apple about an exploit that allowed an attacker to steal private data with a malicious clone of Safari over six months ago. Once a user is tricked into downloading the malicious file, the Safari clone is given undue access by macOS. Any restricted file available to Safari then becomes available to the attacker.
Johnson explains that the exploit works because Apple’s Transparancy, Consent, and Control privacy protection performs an inadequate check on a file’s authenticity. That means the modified version of Safari can be run without activating the aforementioned protection:
In this case, only Safari and Finder should be authorized (by Apple) to access the files in ~/Library/Safari, unless you grant special authorization to another app, such as giving “Full Disk Access” to Terminal. My bypass demonstrates that a maliciously crafted app can also access those files, without being given authorization. There are actually two maliciously crafted apps here: a modified version of Safari, which accesses the protected files, and the app that modifies Safari and launches the modified version of Safari. Any app that you download from the web could accomplish this privacy protections bypass. My sample exploit uploads some of your private data (your Top Sites, for example) to a server that I control, because that’s an easy thing to do when I can run any JavaScript I want.
And yes, the exploit works on the current macOS 11 Big Sur beta too. Somewhat ironically, Apple made a big deal about Safari updates in its latest OS.
Johnson says Apple told him the company is still investigating the problem, after initially telling him it’d be fixed in the spring of 2020. Of course, the world is currently engulfed in an ongoing pandemic, and employees around the world are operating with limited resources; it’s possible this could have contributed to the delay.
Either way, let’s hope the bug is sorted out by the time Big Sur rolls out publicly. For more on how the exploit works, you can check out Johnson’s blog post here.
Via VentureBeat
Get the TNW newsletter
Get the most important tech news in your inbox each week.