Hackers who come across exploits often relay their findings back to the company responsible for the product and/or code, which typically earns them a few bucks in the process. Apple’s recent foray into this field is already bringing out the wolves, with one offering double if you don’t tell Apple what you know.
Last week, Apple announced a bug bounty program targeting kernel exploits and data security. It’s top-end payout is $200,000 for exploits related to boot firmware, and scales down to around $25,000 if you discover an issue with its sandboxing process.
It’s fairly run-of-the-mill stuff; hackers discover a problem, report it back to the company and make money for their work while helping the community at-large.
A company named Exodus will pay over double — $500,000 — for exploits, but is vague about what might earn you that much cash. The company operates on behalf of private firms, and has no apparent interest in the greater good.
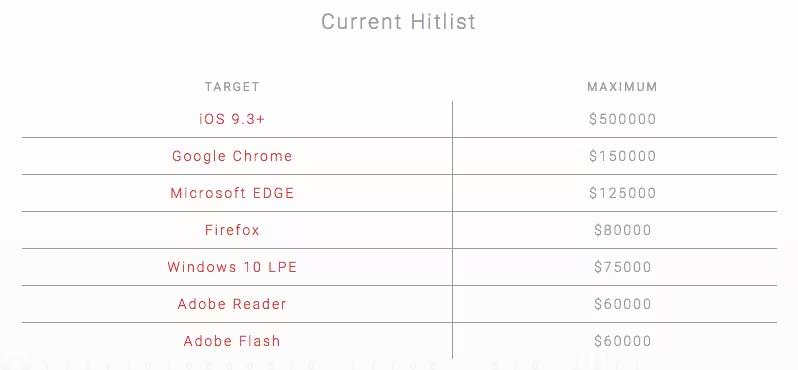
That’s made more evident by its payout structure. On top of whatever the company will pay upfront, Exodus offers to pay quarterly if a discovered hack goes unnoticed by others. It even pays via Bitcoin, and has a ‘hitlist’ for “software targets of immediate interest.”
All told, Exodus wants hackers to become hired guns.
Exodus also doesn’t say why they’d pay so much or keep paying if a vulnerability went unnoticed. It’s likely the company is simply shoring up exploits its customers (which Motherboard reports pay up to $200,000 to retain Exodus’ services) may have before selling your discovery to Apple themselves, but that’s speculative.
Get the TNW newsletter
Get the most important tech news in your inbox each week.






