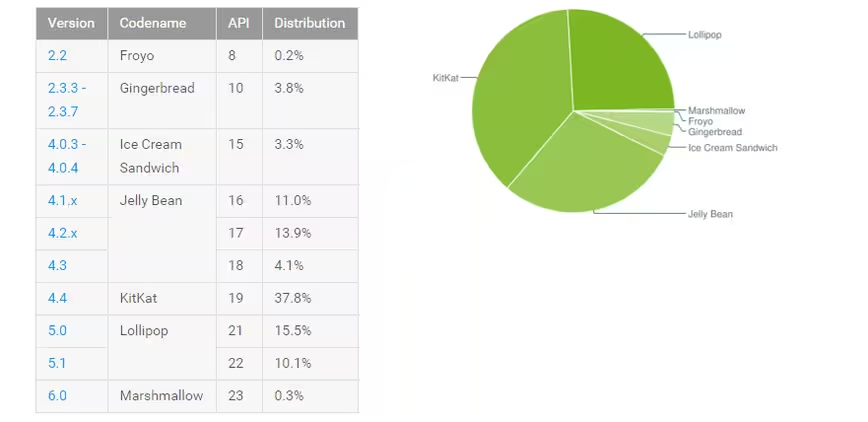
According to a document prepared by the New York District Attorney’s Office, older versions of Android can easily be remotely reset by Google if compelled by a court order, allowing investigators to easily view the contents of a device.
The document, which looks at the impact of full disk encryption on access for law enforcement, says that devices running Android 5.0 (and newer) are unable to be remotely reset as they use full disk encryption – it’s not switched on by default for many devices, however. Anything using an older version is vulnerable to remote reset.
“Forensic examiners are able to bypass passcodes on some of those devices using a variety of forensic techniques.
For some other types of Android devices, Google can reset the passcodes when served with a search warrant and an order instructing them to assist law enforcement to extract data from the device. This process can be done by Google remotely and allows forensic examiners to view the contents of a device.”
According to the Android Developer Dashboard, that means that 74.1 percent of devices are still using a version of Android that can be remotely reset at any time.
iPhone users fare a little better. Any device using iOS 8 or higher can’t have its passcode bypassed by Apple, and full disk encryption is enabled by default.
For any Android users wanting to enable full disk encryption, the setting is often found in the ‘security’ or ‘storage’ sections of the settings, though it does vary by manufacturer. It will slow your hardware down a little, though.
➤ REPORT OF THE MANHATTAN DISTRICT ATTORNEY’S OFFICE ON SMARTPHONE ENCRYPTION AND PUBLIC SAFETY [PDF via Reddit]
Update: A Google spokesperson responded to a request for comment to clarify that remote reset was only ever possible for handsets secured with a Pattern (rather than PIN or Password) using a version of Android before Lollipop (5.0). Google has never had the ability to remotely reset encrypted devices.
Get the TNW newsletter
Get the most important tech news in your inbox each week.