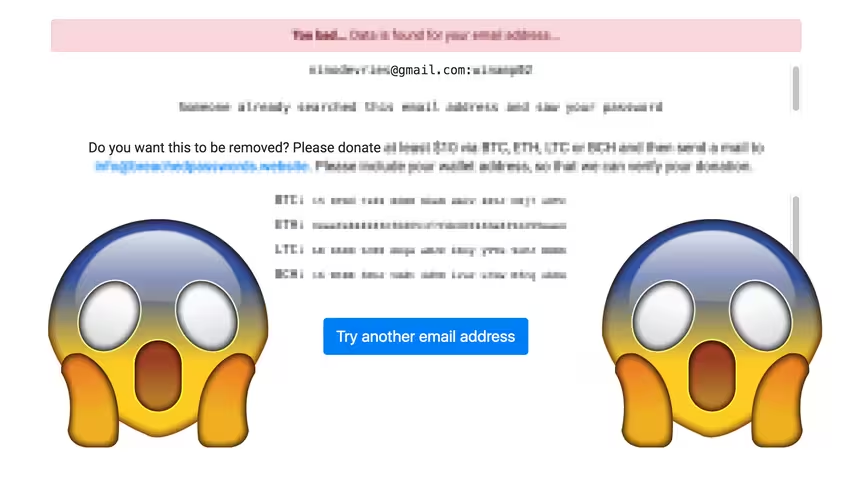
This is pretty nasty. Someone has built a malicious copycat of the popular breach database Have I Been Pwned that will reveal your password in plaintext – unless you pay up a cryptocurrency ransom in Bitcoin, Ethereum, Bitcoin Cash, or Litecoin.
Just like Have I Been Pwned, the malicious copycat will let you check whether your associated email address has been breached in the past. The disturbing part is that it will also display leaked passwords of such compromised accounts. The website then asks users for a one-off $10 donation in cryptocurrency to hide the passwords.
According to the instructions on the website, leaked passwords will only be removed after users have successfully provided proof of payment. It is worth nothing that – depending on how widely you used your passphrase – it might be faster to update your old password than to pay up the ransom.
We have been able to confirm that the sketchy website does indeed have a database with legitimate passwords. The good thing is that it appears the platform does not store plaintext passwords for all compromised accounts found in its database.
It is unclear precisely how extensive the data is, but the website insists it contains 1.4 billion compromised accounts with their associated passwords. Another thing to point out is that some of the leaked passwords are at least several years old from what we can tell. Journalist Daniël Verlaan has said the website uses the same database as popular breach look up service Gotcha.
We have decided not to publish a direct link to the website for security reasons, but it appears that the platform is hardly getting any traction as of now. Indeed, a quick lookup of the associated wallet addresses indicates that nobody has paid the requested ransom fee as of the time of writing.
So in case it has been a while since the last time you updated your password, there is no better time to do that than now – especially if your account was compromised recently.
Update: Shortly after our coverage, the website’s search functionality stopped working. As pointed out by Verlaan, the site is now surreptitiously running a crypto-miner in the background to hijack your computer power.
Update: It appears that the database might have been lifted from a public torrent, according to a tip from readers and corroborated by Verlaan. In any case, there are certainly overlaps between the two data troves.
[H/T Daniël Verlaan]
Get the TNW newsletter
Get the most important tech news in your inbox each week.