In June 2007, the National Institute of Standards and Technology (NIST) released guidance that said that sites should check potential passwords against previous data breaches, in order to ensure they are totally unique.
While most websites are yet to offer that functionality, Troy Hunt, the founder and creator of Have I Been Pwned, has launched a tool where you can check passwords to see if they’ve been compromised.
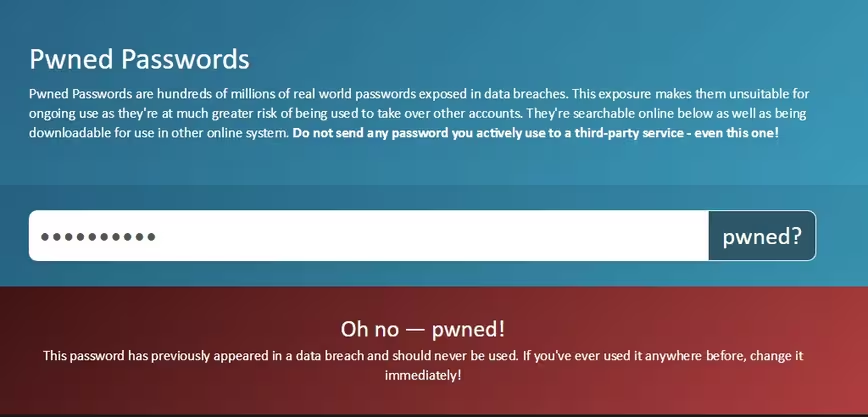
The way it works is pretty simple. Just type in a password, and it will compare it against a database of over 306 million passwords, collected over several years, in order to determine how unique it is.
Hunt has also made the data freely available to download, so that developers can integrate it into their websites.
The site also serves as an exploration of the passwords people use, which admittedly can be pretty weird. It bizarrely common for people to use full names as passwords, and amusingly, it seems someone used ‘troyhunt’ as a password somewhere.
You have some explaining to do pic.twitter.com/OUicVWJIdB
— lektol󠅉󠅦󠄠󠅹󠅯󠅵󠄠 (@lektol1) August 3, 2017
https://twitter.com/MrOwenNelson/status/893040219968110592
Others were weird, or just plain rude.
Looks like passive aggressive passwords aren't secure either: pic.twitter.com/lyqnlqtWov
— Tom van Enckevort (@tomvanenckevort) August 3, 2017
Strangely both "ilovetrees" and "ihatetrees" are pwned
— Tom Newton (@thomasnewton) August 3, 2017
https://twitter.com/notskend/status/893041093742350338
You can try it out for yourself here (although, please don’t use any passwords you’re actively using). While it’s incredibly important that sites learn to protect our private data (passwords in plaintext – not even once), it’s also important that individuals practice good password security and hygiene. You can learn about the best practices here, or alternatively, get yourself a password manager and use an ultra-complicated password for every site you visit.
Update: We changed the wording in this post in order to emphasize that readers shouldn’t test passwords they’re currently using.
Get the TNW newsletter
Get the most important tech news in your inbox each week.





