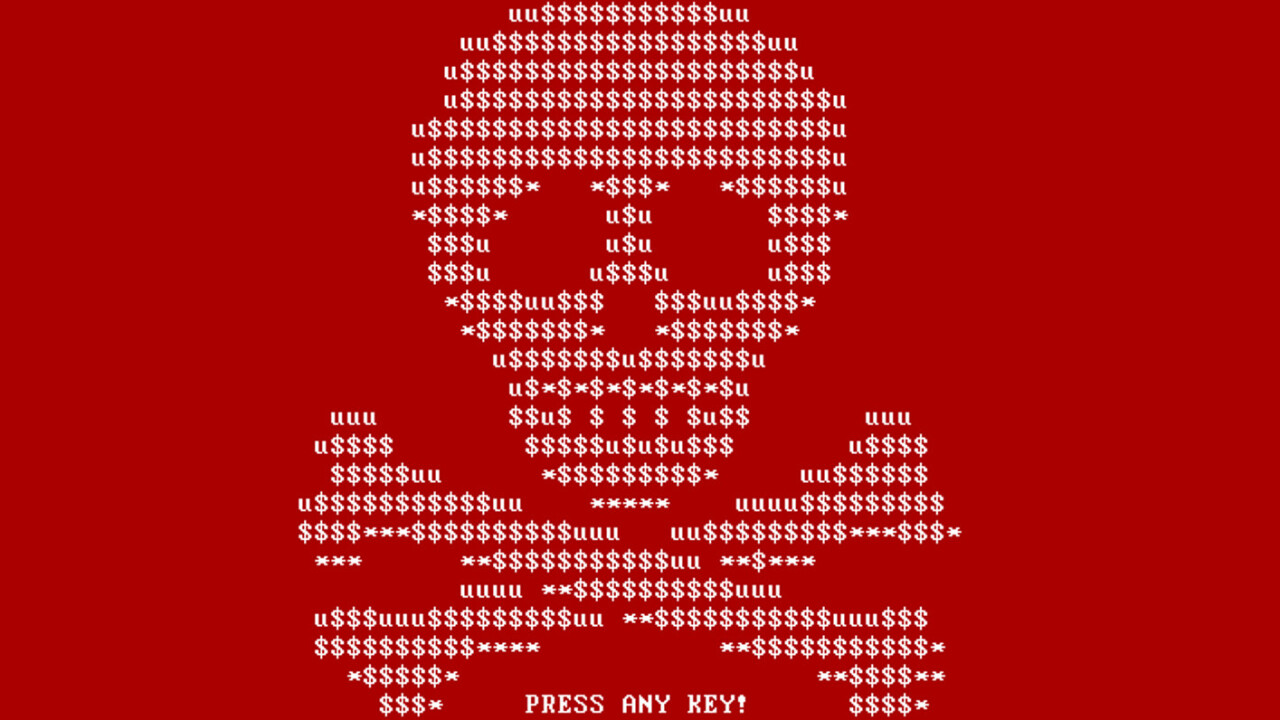
If malware that holds the files on your computer to ransom isn’t bad enough, news that there’s a new variant in the wild that locks down the whole of your computer by taking over the boot process just made the situation a whole lot worse.
Called ‘Petya’, the new threat bypasses looking for the most important files to encrypt, and just goes ahead and locks up the entire drive instead, according to G Data Software.
To achieve its goal, the attacker sends out innocuous looking email that purports to be from a job applicant, with instructions to download a CV hosted in a Dropbox folder. Naturally, the CV is the ransomware and it immediately trashes your boot record, forcing your computer to crash.
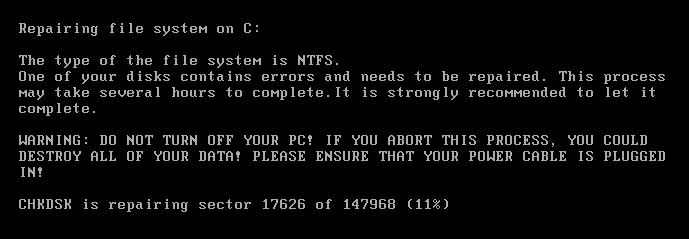
When it reboots, a message will appear saying that it needs to fix errors and that it may take several hours. During this time, the entire hard disk is encrypted.
Once complete, on next boot, the user is presented with the sad truth: pay a ransom via Tor or lose access to everything on your hard drive- and that ransom doubles after seven days.
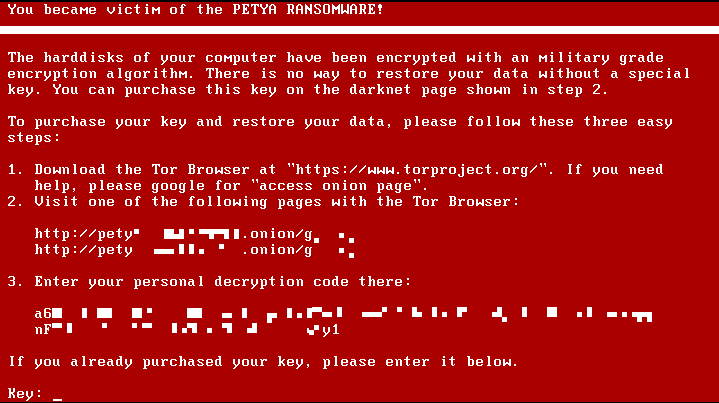
G Data recommends not paying the requested ransom and instead ensuring that all your data is backed up. That way, you can just copy that image back across, should the worst happen.
While this is by no means the first ransomware online, it’s part of a worrying trend that seems to line up businesses as more lucrative victims than individuals – one hospital this year has already paid $17,000 in bitcoins after it was locked out of its network.
As with many of these attacks, Petya relies on computer users clicking links sent in emails before really considering what they are, or the potential implications.
One sure-fire way to cut down on these is just to simply refuse to open random files from people you don’t know.
Crazy, huh?
Update, March 29: A Dropbox spokesperson got in touch with the following statement:
We take any indication of abuse of the Dropbox platform very seriously and have a dedicated team that works around the clock to monitor and prevent misuse of Dropbox. Although this attack didn’t involve any compromise of Dropbox security, we have investigated and have put procedures in place to proactively shut down rogue activity like this as soon as it happens.
Get the TNW newsletter
Get the most important tech news in your inbox each week.