
Your Starbucks account is like catnip for hackers. In the past few days, the longstanding problem has become a story again, after a blog post by American journalist Bob Sullivan, was widely picked up.
He writes:
Criminals are using Starbucks accounts to access consumers’ linked credit cards. Taking advantage of the Starbucks auto-reload function, they can steal hundreds of dollars in a matter of minutes. Because the crime is so simple, can escalate quickly, and the consumer protections controlling the transaction are unclear, I recommend all Starbucks consumers immediately disable auto-reload on the Starbucks mobile payments and gift cards.
The fraud is a big deal because Starbucks mobile payments are a big deal. Last year, Starbucks said it processed $2 billion in mobile payment transactions, and about 1 in 6 transactions at Starbucks are conducted with the Starbucks app.
The story quotes several customers who have had significant amounts of money taken using the trick. A quick Twitter search reveals it’s a common predicament.
https://twitter.com/ally_gantner/status/598970607980695552
https://twitter.com/Drea_4/status/598870508306866178
For its part, Starbucks has been quick to downplay the issue, denying outright that its apps and systems have been “hacked”:
Starbucks takes the obligation to protect customers’ information seriously. News reports that the Starbucks mobile app has been hacked are false.
Like all major retailers, the company has safeguards in place to constantly monitor for fraudulent activity and works closely with financial institutions. To protect the integrity of these security measures, Starbucks will not disclose specific details but can assure customers their security is incredibly important and all concerns related to customer security are taken seriously.
Occasionally, Starbucks receives reports from customers of unauthorized activity on their online account. This is primarily caused when criminals obtain reused names and passwords from other sites and attempt to apply that information to Starbucks. To protect their security, customers are encouraged to use different user names and passwords for different sites, especially those that keep financial information.
It goes on to note that you’re not responsible for charges or transfers you didn’t make and that your balance is protected if you register your card.
The ‘how’ but not the ‘why’
Both Sullivan’s report (and the numerous follow-up pieces) and Starbucks’ response are fine to a point. But the company is relying on a particular definition of “hacked”.
Most media reports fail to get to the crucial question: what’s the end game of breaking in to Starbucks accounts when the money is seemingly trapped in its system? Are these criminals just huge coffee fans?
Firstly, on defining whether Starbucks has been ‘hacked’, Paul Martini, CEO and co-founder of security firm iboss, says:
This line of argument is so common now – it’s basically playing with words. Whether the app is literally hacked or not, it’s completely ridiculous. The design itself is flawed. Auto-reload should happen at the register. The second part issue is: why can people reload and drain a card within ten minutes?
It’s also clear that obtaining user names and passwords from other data breaches is not the only way criminals are gaining access to Starbucks accounts. Phishing emails designed to look like they’re from the firm are very common. I got one while I was in the process of researching this article:
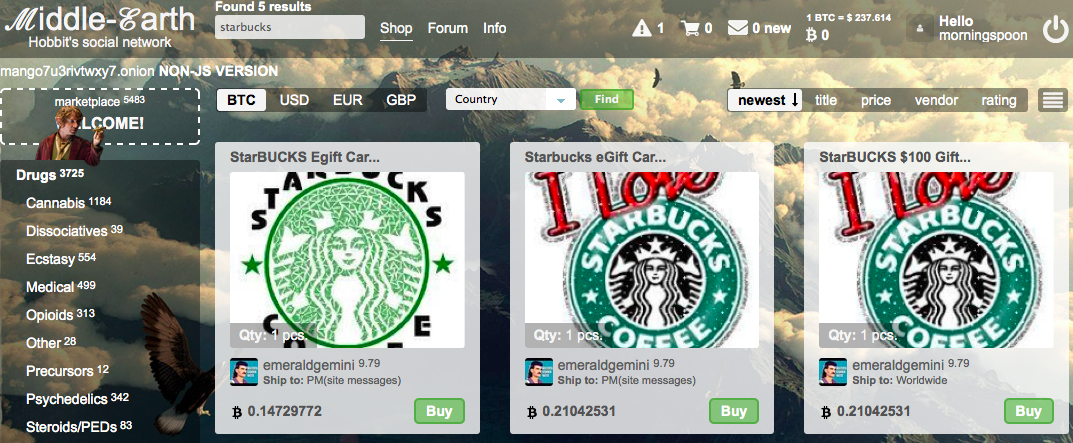
It’s clear that Starbucks accounts are very appealing to scammers. On ‘dark web’ marketplaces like Alpha Bay and Middle Earth – accessible only via the Tor browser – you can find numerous listings offering access to compromised user details.
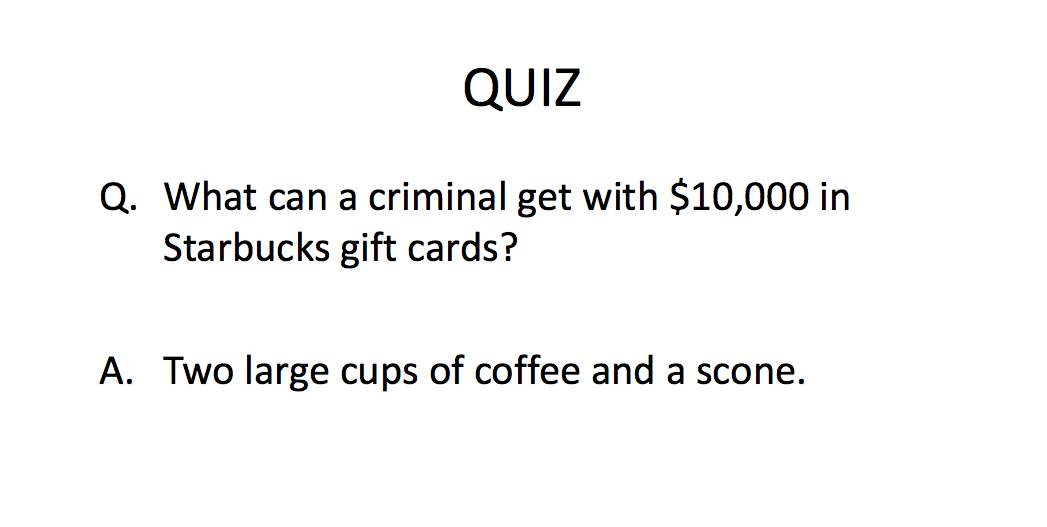
But back to the question of how criminals can profit from the accounts once they have access. The easiest way is by exploiting the auto-reload function and buying a string of gift cards, which can then be sold online at a reduced price.
Starbucks confirmed to me that while it’s not possible to buy e-gift cards with your Starbucks card or app, you can use them to purchase gift cards in store.
The trouble with that approach is that it is very labor-intensive and the rewards are not particularly high versus the effort required.
Paul Martini suggests another take on the scam:
Purchases of coffee in bulk and selling that on the black market could work. A bag of Starbucks espresso runs at $10 to $15 [Ed: in fact, it’s cheapest ground coffee online comes in at $11.95 a bag]. My theory is that if you do it in enough quantity, maybe purchasing and shipping stuff is the end game. It’s the bridge between a digital hack and an actual physical theft.
There is also the remote possibility that the individuals exploiting the Starbucks card have found a way to move the money out of the closed system, but no one has yet identified a loophole allowing them to do that.
How dirty money gets clean
Another factor in the appeal of Starbucks accounts to criminal actors is how useful consumer cards can be for laundering money. An FBI presentation from 2011 notes:
Separate organized crime, narcotics and white collar investigations have identified similar trends of pre‐paid store gift cards purchased under suspicious circumstances.
The benefit of moving moving to pre-paid gift cards is that its source is obscured and the cards themselves become a new form of clean currency that can be sold on.
One reason Starbucks account details are popular on the dark web may be as a means of further distancing these transactions from their originators.
How Starbucks (and you) can fix it
Despite the corporate shrugging the current Starbucks card system is broken. Brendan Rizzo, Technical Director for HP Security Voltage, says it needs to make changes fast:
If this continues to happen or gets worse, it’ll start looking complacent. I think it’s now going to be about saving face and reassuring customers that it is safe to do business with.
There seems to be a very defined pattern to the amounts that are charged. It should be quite rudimentary for Starbucks to notice that behavior and shut down accounts that match it.
The company already has measures in place to detect unusually large transactions, but has struggled to deal with smaller but rapidly repeated payment patterns.
Ultimately, it’s about the old battle between security and convenience. Retailers like Starbucks are usually inclined to lean towards the latter. Gavin Reid, Vice President of Threat Intelligence at network security firm Lancope, says:
We’re seeing the rough edge of convenience here. One time passwords would be a lot more secure than expecting people to use and remember a long password, as Starbucks does. Another easy fix would be to send customers a notification by SMS or email with every use.
In the mean time, the best solution available to you as a Starbucks customer is to turn off auto-reload entirely and ensure that the username and password you’re using for the account is distinct. But then, that’s not necessarily so convenient, is it?
Read Next: The art of creating a secure password that you can remember
Get the TNW newsletter
Get the most important tech news in your inbox each week.




