David Bozin is the VP of Business Development at Bindo, a New York based unique retail technology company with an innovative iPad POS system and soon-to-be launched online Marketplace.
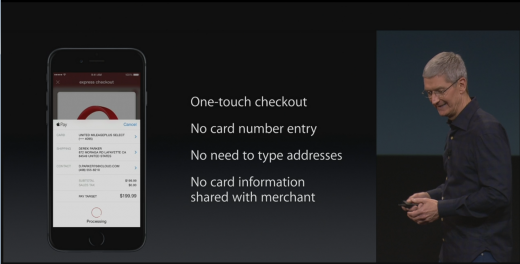
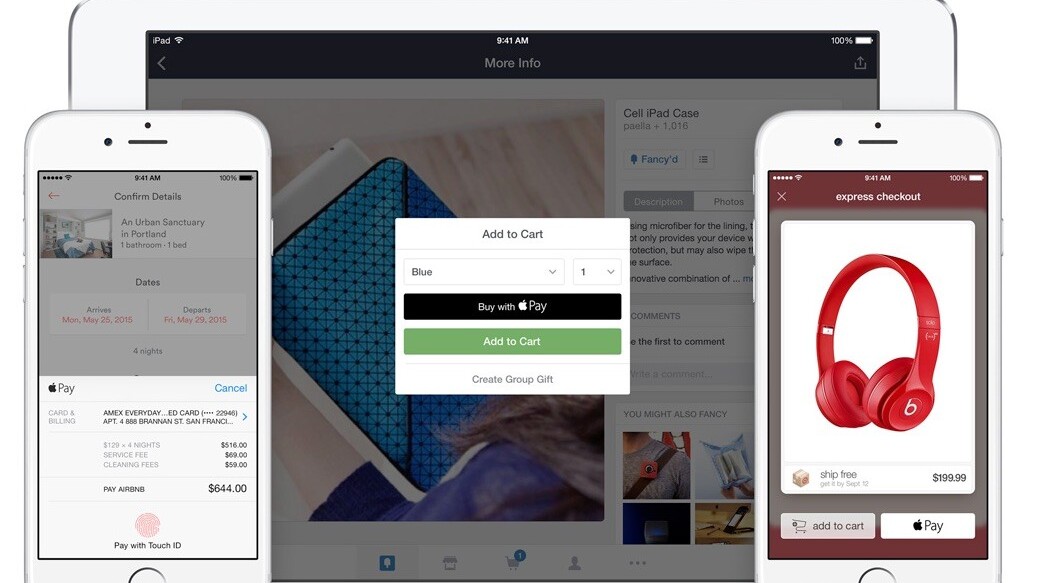
With Apple Pay coming out, it seems as if there is a whole new technology that has just been released. In reality, NFC payments have been around for a while, but Apple is the platform that has enough user adoption that will actually result in mass adoption. Thus far, we have seen just the start, with further tech such as the Apple Watch supplementing further growth.
With mass adoption of a new technology, especially one dealing with that which we value so highly (money), there will be ever increasing attention from all sides of the table. One of the perspectives is from the user and how they could make their lives easier by not needing to carry so many cards.
Another is from the merchant who takes into consideration what they need to use to accept payment, and how they could negotiate rates. Another comes from the hacker and fraudster, who sees an opportunity to obtain funds by finding loopholes, either internal or external to the platform.
Apart from the increased attention, mass user adoption will create massive checks on existing systems…a stress test of the greatest level, involving the payments infrastructure. The issue we are experiencing now, as a result of Apple Pay, is a result of an infrastructure that, up until now, has not really required too much monumental change.
Acquiring banks, payment gateways and the acquirers themselves have focused on one major thing: merchant acquisition. With Apple Pay, that still has its place, but it uncovers another major issue: infrastructure overhaul, from the process of authorizing individuals to how the card is input and authorized via an NFC payments platform and is finally authorized during payment.
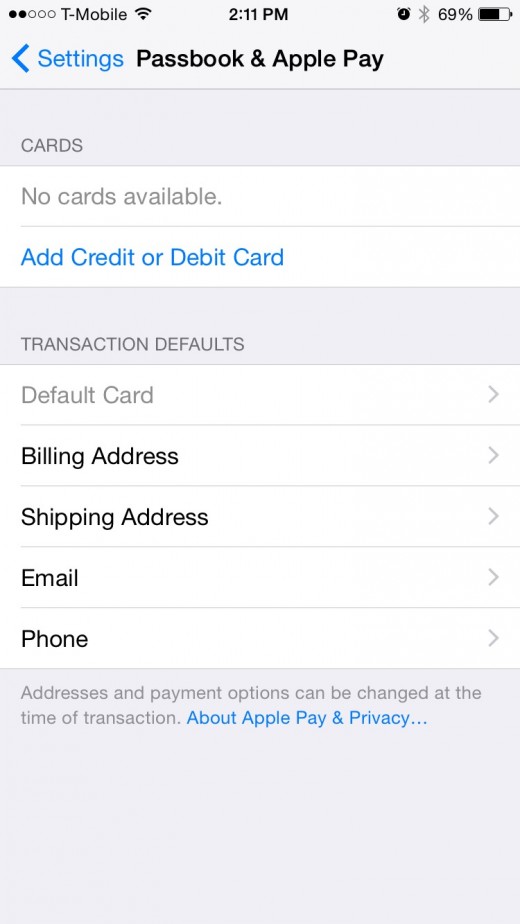
Thus, the ABC’s of how a card is loaded into your Apple Pay account:
- Load in the card information
- Apple encrypts the data and sends it to its own servers
- Apple Un-encrypts and sends the data to the card network
- Apple re-encrypts the data knowing the card’s bank and sends to that bank
- Bank receives the card information, along with certain information tied to the iTunes account on the device
- Bank either gives a greed, yellow or red light. Green = immediately approved. Yellow = additional security questions to confirm validity of the user’s id (done through the Apple interface). Red = Card not accepted.
- Pay away! (assuming it got approved)
Now it is point 5 & 6 where the fraud is actually occurring, outside of the Apple ecosystem. There is only so much that Apple can provide as regards user information. The weak point is pre-encryption, between when the card is swiped through old hardware, going through a potentially outdated hospitality management platform, and passing finally over to the payment gateway.
Whether it be via code or hardware that is placed between swipe and encryption of card data, it becomes relatively simple for a person understanding how payments work to find a way to pull credit card information.
The bank’s process of verifying a user is so important. What defines whether that card is actually yours? What happens if it is a prepay (where the majority of crime rings get their greatest success) and the regulations are most lax? What happens when someone steals a card off of someone where the name is known, as is the city where they live?
Many times, the fraud protocol will catch an anomaly. Fact of the matter is that there are many ways in which the card networks and banks can improve their processes and implement technology to enhance protection of the card users. This change will happen sooner or later, want it or not, as NFC payment through device will only continue to grow.
The loophole is relatively simple, which has resulted in the high rates of fraud. The prevalent number is 6 per cent, which is a very high figure indeed. Whether this figure is true or not, it is still significant enough to show that there is a major flaw somewhere. It has been made clear that the issue is not with the consumer-facing side, specifically via Apple Pay, but rather on the acquirer/network side, which amongst many other aspects, is responsible for authorizing that card to the user.
So we look into the details of the information that can be provided by Apple:
- certain information on the iTunes account
- general location of the user
- links to the bank apps that the user may or may not be using
That is basically it.
So now, if someone who wants to proceed with fraudulent activity gets a new iPhone and loads in a credit card of a person who obviously lives within the area (+ their name is on the card, making it rather easy to find out more about where they live and work, etc.), then it becomes somewhat simple to try for activation. Now we have either a green, yellow or red path. Green = fraud away! Yellow = Still have a pretty good chance. Red = Try another card.
So the yellow path is the major focus for fraud. What happens? You might get a few security questions, OR you get forwarded to the call center to talk with a person for activating your account. The issue is the fact that there is going to be a high volume of calls, and the only existing infrastructure for fielding them would be: Customer Service. Really?! I am trying to activate a card that could be used fraudulently and I get sent to customer service, whose sole purpose is to make customers happy?
I am sure that a person who can create a sense of urgency and can break the person on the phone whilst still keeping an ounce of credibility can achieve activation. Now the real numbers are not certain, but thousands of calls a day, with human error as a major factor, and a mildly intelligent fraudster can easily result in 10’s if not 100’s of active cards being authorized with the intent of fraud on a daily basis.
Now you think about it and see if that is a good means to prevent fraud. I would certainly not think so. Apple has done its job; now it is time for the card network and acquirers to do their job: multi-factor authentication. Instead of asking where I live or what my mother’s maiden name is (have we never heard of Facebook?), ask me where my last transaction took place.
Ask me about a specific location that I bought from a week ago that may or may not be a restaurant. I bet this small change in questions, without changing anything else, would at least half the rate of fraudulent authorized cards.’
Read Next: Apple Pay is now available at more than 700,000 locations
Get the TNW newsletter
Get the most important tech news in your inbox each week.