When was the last time you got a data breach notification, a letter in the mail about a potential compromise, or an email triggering a password reset on one of your accounts?
What about your kids?
When it comes to data breaches, we almost exclusively focus on adults. It’s automatic, instinctual: compromised data impacts customers, consumers, employees, and executives. We immediately assume they must be adults.
Unfortunately, that’s not the case — far from it.
A concerning trend
In my role as a security researcher, stolen identities and compromised payment cards are just a normal part of the workday. Criminal marketplaces hidden away on the dark web have entire economies devoted to buying, selling, and leaking stolen information — it’s a full time job for cyber criminals, and they’ve built entire ecommerce platforms to keep up with it.
I’m used to stolen data. It’s everywhere. It doesn’t surprise me.
Recently, however, I’ve seen slow traction around a new trend: advertisements for compromised data belonging to children. Child data isn’t popular on the dark web. In fact, it’s almost entirely unheard of. Fraudsters are in business to make money, and in most cases that involves stealing and exploiting information from people who have money and who transact in the world — namely, adults.
That’s starting to change.
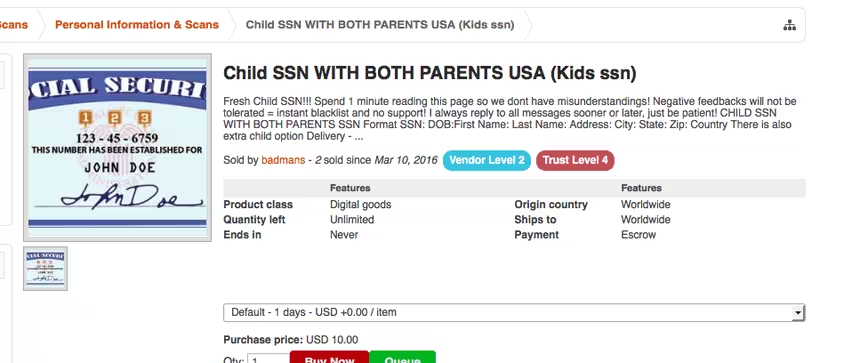 The first red flag appeared in early 2016. A single ad appeared on a major dark web market, advertising “Child SSNs” packaged with parent information. Children’s Social Security numbers, served up in a convenient family pack, all for the low price of $10. It was a strange and unusual apparition at the time, and I wrote it off as a fluke.
The first red flag appeared in early 2016. A single ad appeared on a major dark web market, advertising “Child SSNs” packaged with parent information. Children’s Social Security numbers, served up in a convenient family pack, all for the low price of $10. It was a strange and unusual apparition at the time, and I wrote it off as a fluke.
Then, nearly a year later in late 2017, another listing appeared. This time from a different vendor, on a different market, with targeted advertising: “infant fullz,” the listing read, “get em before tax season [sic].” Fullz is slang for a full identity kit, a designation that the data contains everything a fraudster needs to steal an identity: name, address, account credentials, payment card data, answers to security questions, etc. Infants, mere weeks or months old, have less data than adults, but they still have enough information for cyber criminals exploit.
Two advertisements is concerning. Three is a trend.
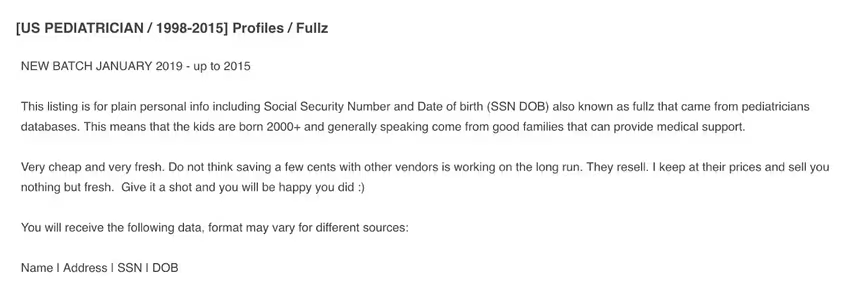 The third listing appeared just a few months ago, near the end of 2018. Yet another vendor showed up on the dark web with child data for sale. This time, the vendor was explicit about their sourcing: as part of their breach of a major hospital network, the vendor had a collection of child data from pediatricians’ offices.
The third listing appeared just a few months ago, near the end of 2018. Yet another vendor showed up on the dark web with child data for sale. This time, the vendor was explicit about their sourcing: as part of their breach of a major hospital network, the vendor had a collection of child data from pediatricians’ offices.
Offering records for children with birth dates ranging from 2010-2015, the vendor was quick to highlight the quality of the data sets: “generally speaking,” the vendor stressed, the kids “come from good families that can provide medical support.”
The kids are not alright
So why does this matter? What can a criminal do with the data on your first grader? Unfortunately, quite a lot.
Some of these data sets are being actively advertised for tax fraud, where fraudsters use child data to take advantage of the child tax credit while filing fraudulent tax returns. More frequently, criminals are using child data to create what are called synthetic identities.
Traditional identity theft exploits a real, complete identity. Synthetic identities take a more nimble approach to fraud, piecing together new identities from a collection of individuals, often hinging on an unused (or unchecked) Social Security number. That’s where the kids come in.
While it might surprise you, there are limited checks in place to prevent someone from using a synthetic identity with an underage SSN to apply for credit, and once this newly invented individual has access to an initial credit line, they can slowly build credit, develop account access, and amass incredible debts over time. That’s the benefit of using children for the scheme: kids are too busy learning to read and write to check their credit reports, and parents typically don’t put credit freezes on their baby shower wish lists.
The problem goes unnoticed for years — possibly decades — before the child goes to apply for student loans, open their first credit card, or buy their first car. Anyone who’s had their credit card compromised knows how much damage criminals can do in the span of a few minutes. Imagine what they can do with a few years. Industry numbers indicate that synthetic identity fraud may have accounted for $6 billion in losses in 2016 alone — at least some of those losses will be attributed to children.
The future is bright (with a side of identity theft)
These listings aren’t the first time children have been caught up in data compromise. In November 2015, toymaker vTech announced a breach impacting 200,000 children around the world. Days later, they adjusted the number, reporting that, in fact, more than 6.3 million children were exposed.
Only weeks ago we saw two separate reports indicting Facebook for their negligence with child data, including the use of a research app to spy on minors and willfully turning a blind eye to friendly fraud to encourage children to embed themselves even further in video games without parental permission.
As the market for customer data grows, manufacturers, tech companies, and advertisers are collecting data on their target audiences at younger and younger ages. The more children are drawn into data collection, whether by governments, manufacturers, or tech giants, the more likely they are to face the same exposure as adults, with the same consequences.
We need to take data security more seriously for the children in our communities — our data is already exposed, and we’re forced to do more and more damage control with each new data breach announcement. If we act swiftly and firmly, we may be able to stem the damage before our children, and their children, face the same reality.
Get the TNW newsletter
Get the most important tech news in your inbox each week.