It’s been obvious for a while now that the security industry is turning in circles. Users have walked a very insecure tightrope for decades, clicking on links, opening attachments, and downloading unchecked files without a safety net in place.
I always find it sad when organizations are surprised that the bad guys found a way to trick an employee into clicking something malicious even though that employee has successfully completed a security awareness seminar.
In a survey last year, my team and I found that 99 percent of CISOs see users as the last line of defense against the bad guys. My question is, “is this remotely fair to end users?” The fact is, no matter how much training is offered to organizations, there will always be someone who clicks on something bad and it just seems naïve to think that this will ever change.
One bad apple spoils the bunch
According to the SANS Institute, 75 percent of attacks on endpoints initially enter organizations via email attachments; and another 46 percent of attacks were executed by users clicking web links in emails. The common school of thought is that companies can educate and train employees to be aware of the risks and therefore the company will be protected against email-based attacks.
Many agree that this logic makes sense, but the fact still remains – it only takes one person to be tricked and trigger a breach. In a report from Verizon in 2017, they found that 30 percent of phishing messages get opened by targeted users, with 12 percent clicking on malicious items multiple times.
And success breeds sophistication with hackers unveiling a wide range of tactics to try and fool employees into making that single mistake – whether it’s through spear-phishing with a CEO’s email address, or leveraging infected USB drives, insecure hotspots, man-in-the-middle attacks, or polymorphic malware. The odds are undeniably stacked against the user.
Human behavior = Security vulnerabilities
So, let’s admit that the idea of making employees responsible for security simply isn’t practical. Even after all the training and education, human beings will make mistakes and expose the company to risk. Even the most security-conscious employees get tired, overworked, busy or distracted.
Employees across the business are being asked to assess risk vs reward every time they visit a webpage or open an email attachment – something they likely do dozens, if not hundreds, of times a day. In some cases, their behavior is just habit, and sometimes they decide the reward of that activity is more important than the risk.
To counter human behavior, many businesses are turning to technology to prohibit users, but this often causes more problems than it solves. For example, many companies restricted social media websites following the 2012 LinkedIn breach, as they see these sites as vulnerable points of entry for an attacker.
But, often these sites are a critical path for departments like marketing, sales, or HR, who are then unable to carry out essential tasks as a result of limited or zero access. Employees still need to do their jobs, and this puts them at odds with prohibitive security practices.
Click with confidence
Modern threats need modern solutions. Let’s stop putting the responsibility and blame on end users, who should never have had to shoulder the burden in the first place. Most of the IT security industry is focused on stopping the symptoms, rather than creating a cure.
Alternative approaches help minimize cybersecurity risks more effectively, and in a scalable manner, which are far less restrictive on the business and its employees. In fact, a new approach to security can become a competitive advantage because your users can get back to work and stop being afraid.
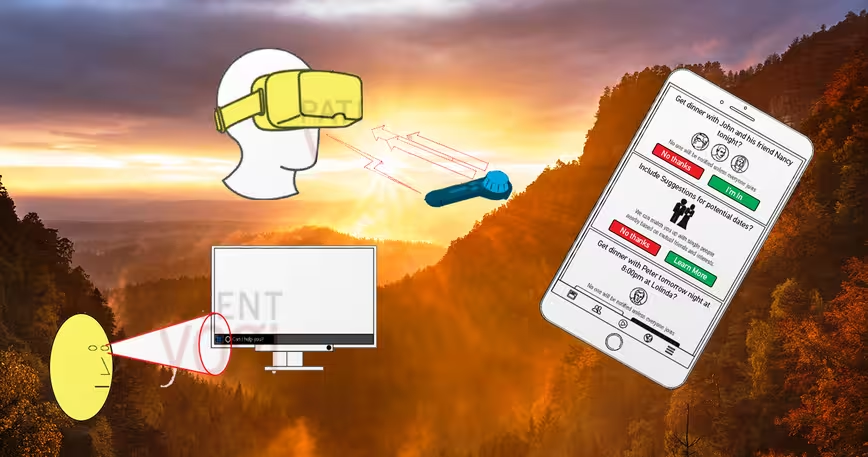
Imagine, instead of wasting time trying to stop users clicking on potentially harmful links or trying to detect malware before it has a chance to launch, you let it execute. Here’s the catch: it’s executing in its own completely secure virtual environment. This ensures that each user task is contained within its own fully isolated and disposable virtual machine.
As a result, any malicious activities are trapped within that virtual machine, posing no risk to the rest of the machine or the network. If a user discovers a malicious email or document, they can simply close the window or browser tab, and the threat disappears forever.
The logic is simple: if a user is opening a downloaded document, working with an application or clicking on a web page because they need to get their work done, then why not isolate those high-risk activities in a completely isolated, controlled environment? This gives CISOs the ability to trust end users because the safety net they need is in place. They can click with confidence.
We’re only human
As the ‘80s band, Human League, sang, “we’re only human…born to make mistakes.” Cybersecurity obviously needs to improve, and there are smarter ways to deliver protection and take the human aspect out of the equation. I mean, seriously, enough is enough.
Application isolation offers a profound solution. Today’s patient-zero, detect-to-protect approach still allows for vulnerabilities. Just to be clear, cybercriminals still haven’t been locked out. They are still having tremendous success. As long as exploiting end users remains profitable, hackers will continue seeking to pound away at earnest employees, who are only human.
Today the hackers are winning, but it doesn’t have to be that way. While organizations waste time and money educating employees, trying to break habits that are based on human nature, the bad guys keep getting through. Businesses that are using application isolation are finding they no longer pin their hopes on solutions that work only after a breach has been detected.
This allows end users to click with confidence, can restore productivity, and even allow for innovation because end user prohibition is no longer a security strategy. Instead, employees can focus on getting work done without worry.
Get the TNW newsletter
Get the most important tech news in your inbox each week.