Update on October 11 – Skype malware steals more than your money: User accounts from Facebook, Twitter, PayPal, and more
Cybercriminals are once again targeting Skype users, although this time they are using ransomware and click fraud on their victims. For the uninitiated, ransomware is malware which restricts access to the computer it infects (either by encryption or locking the system and spamming with prompts), demanding a ransom paid for the restriction to be removed.
Click fraud meanwhile is a type of scam that occurs when someone or a program imitates a legitimate user by clicking on an ad for the purpose of generating revenue for another party. As such, the authors behind this malware are making money off ignorant Skype users in at least two ways.
GFI first reported this issue on Friday, but then released an update today when it became clear ransomware and click fraud were being used. GFI detects the malware as Backdoor.Win32.Hupigon, Sophos detects it as Troj/Agent-YCW or Troj/Agent-YDC, and Trend Micro just calls it a variant of the Dorkbot worm (also known as NRGbot).
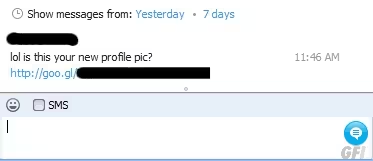
The malware in question uses the message “lol is this your new profile pic?” followed by a link to spread via the messaging platform. The link has already been changed a few times, and the message can also likely be altered. In fact, Trend Micro says the malware is so far spreading in English and German, but it could of course be translated into various other languages as well.
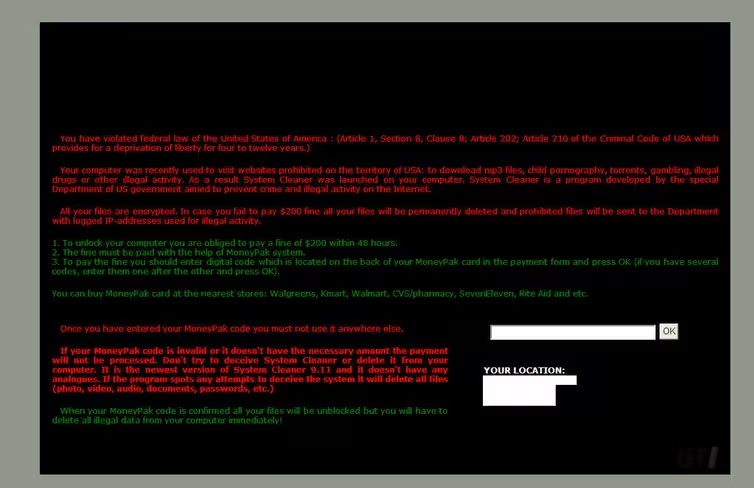
If you click the link, you will end up with a zip file on your PC. Running the executable inside (skype_02102012_image.exe or skype_06102012_image.zip or skype_08102012_image.zip) will infect the PC and will leverage a Java exploit via BlackHole 2.0. Minutes later, you will be prompted with this warning:
GFI explains how it works:
The above is a typical Ransomware scare message that locks the user out of their data, encrypts the files and demands payment (via Moneypak) to the tune of $200. The IP address and geographical location is displayed in the bottom right hand corner, along with various threats related to the downloading of MP3s, illegal pornography, gambling and more besides.
That’s not all. Behind the scenes, the malware is also making click fraud attempts. We’re not just talking about a few clicks: in the space of 10 minutes, GFI recorded 2,259 transmissions.
Sophos meanwhile details that the Trojan horse opens a backdoor, allowing a remote hacker to take control of the infected PC to communicate with a remote server via HTTP. The security firm also notes that the malware makes sure it is always running:
On execution the malware copies itself to %PROFILE%Application DataJqfsfb.exe
and sets the autostart entry as below:entry_location = “HKCUSoftwareMicrosoftWindowsCurrentVersionRun”
entry = “Jqfsfb”
description = “Skype ”
publisher = “Skype Technologies S.A.”
image = “c:documents and settingssupportapplication datajqfsfb.exe”
launch_string = “C:Documents and SettingssupportApplication DataJqfsfb.exe”
As a general word of caution, don’t click on links sent to you via Skype or any other instant messaging service. Furthermore, don’t extract zip files and open files within, especially if you don’t know what they are. If Windows warns you that “The publisher could not be verified, are you sure you want to run this software” – listen to it and click Cancel.
We have contacted Microsoft about this malware. We will update this article if and when we hear back.
Update at 1:55Pm EST: “Skype takes the user experience very seriously, particularly when it comes to security,” a Skype spokesperson told The Next Web. “We are aware of this malicious activity and are working quickly to mitigate its impact. We strongly recommend upgrading to the newest Skype version and applying updated security features on your computer. Additionally, following links – even when from your contacts – that look strange or are unexpected is not advisable.”
Update on October 11 – Skype malware steals more than your money: User accounts from Facebook, Twitter, PayPal, and more
Image credit: Michaela Kobyakov
Get the TNW newsletter
Get the most important tech news in your inbox each week.