Last week, the tech news cycle was dominated by the standoff between Apple and the FBI over a court order that required the former to create software to aid the latter in unlocking the iPhone of one of the San Bernadino shooters.
While the battle seems to be dying down a bit after recent revelations that the phone may have been wiped anyway, it did get me thinking about the steps I’d take to protect my iPhone, should the need ever arise.
I should point out two things.
One, this level of security on an iPhone is almost never necessary. Two, there is no such thing as a foolproof solution. Even the most careful security plans aren’t perfect.
But, if forced to try to think like Edward Snowden, while not donning a tinfoil hat, here’s how I’d protect my iPhone.
It all starts with the lock code
By default, we’re allowed six-digit unlock codes, but if those six digits are chosen carefully, it’s a decent way to protect your phone from most threats. The reason for this is due to a couple of security features from Apple and the sheer number of passcode combinations possible (1,000,000).
The first security feature is the requirement that all password combinations are attempted on the phone itself. Currently, it’s not possible to connect an iPhone running iOS 9 to a machine in order to brute force the passcode (guess every possible combination), you have to enter these by hand.
The second feature adds a delay to each attempt. This delay gets longer as you guess incorrectly. After four incorrect guesses, the attacker has to wait one minute before trying again, and then five minutes, 15 minutes and finally one hour.
There’s a third feature as well, but it has to be turned on. In Settings > Touch ID & Passcode, you’ll find an option at the bottom that says Erase Data; enable it.
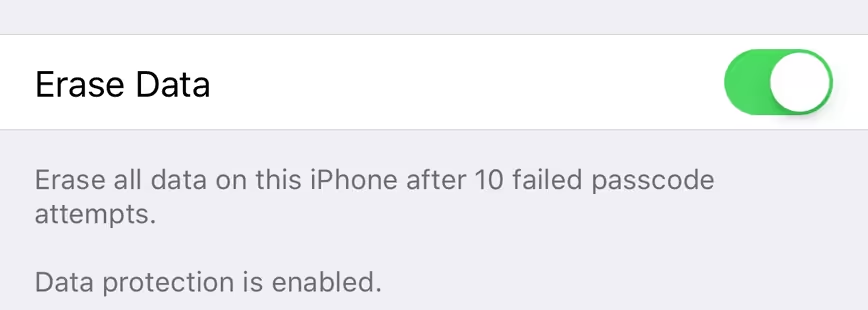
Enabling this feature gives attackers 10 tried to guess your passcode and then wipes all of the data from your phone.
All of the features above are what the Department of Justice ordered Apple to write new firmware for. If Apple created this new firmware, it would allow the FBI to bypass these security features and simply guess all possible password combinations. If allowed, the FBI could crack a six-digit numeric passcode in less than a day.
Of course, if you just want to call it a day and put this whole thing to rest right now, you have the option to create longer passcodes, or even to make them alphanumeric. In Settings > Touch ID & Passcode > Change Passcode, you have the option to set it to alphanumeric after you input your current passcode.
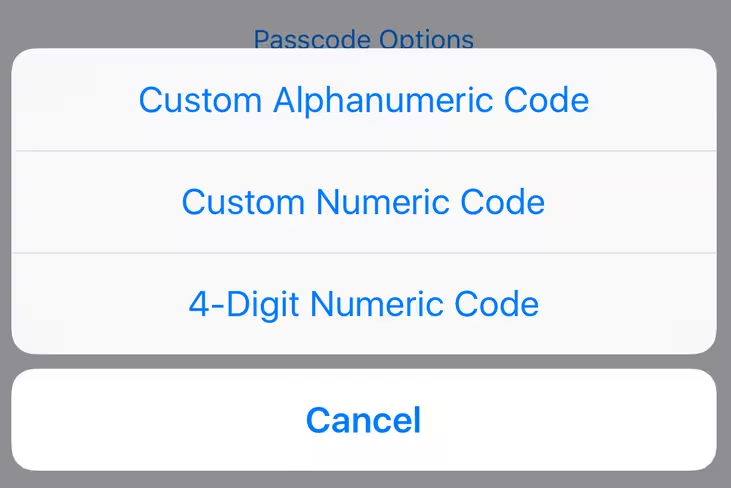
A 12-digit passcode with letters, numbers and special characters, for example, would take 4 million years to crack using current brute force techniques and hardware. Even if Apple did create the software the FBI is asking for, it’d be all but meaningless.
In all honesty, you could probably stop here and be plenty secure, but what’s the fun in that?
Disable Touch ID
I don’t need to spend a lot of time here, let’s just say that it’s been proven repeatedly that the fingerprint sensor isn’t a secure way to unlock your phone. To disable Touch ID, Settings > Touch ID & Passcode and then disable all of the settings that use the Touch ID.

The strongest passcode in the world means nothing if you can defeat a fingerprint sensor with a piece of plastic.
Instead, we want to force attackers to enter a passcode, and a long one at that.
There’s also precedent that police can force you to unlock a phone with a fingerprint sensor, even though they can’t require your passcode without a warrant.
Kill automatic backups
iCloud backups aren’t secure. Your files reside on Apple’s servers, non-encrypted, and are easily accessible by Apple, and anyone else who has a court order. Apple is fighting to keep from weakening security, not to avoid handing over un-encrypted files to law enforcement or government agencies when requested. It’s an important distinction to make.
Instead, start making local backups of your iPhone using iTunes. It’s not the most convenient of solutions, but if you’re looking for the safest way to protect your backups, this is it.
If you’re extra tinfoil hat-y, you can even disable the internet while making these backups, but it’s not necessary.
Don’t forget to encrypt the backup by checking the appropriate box.
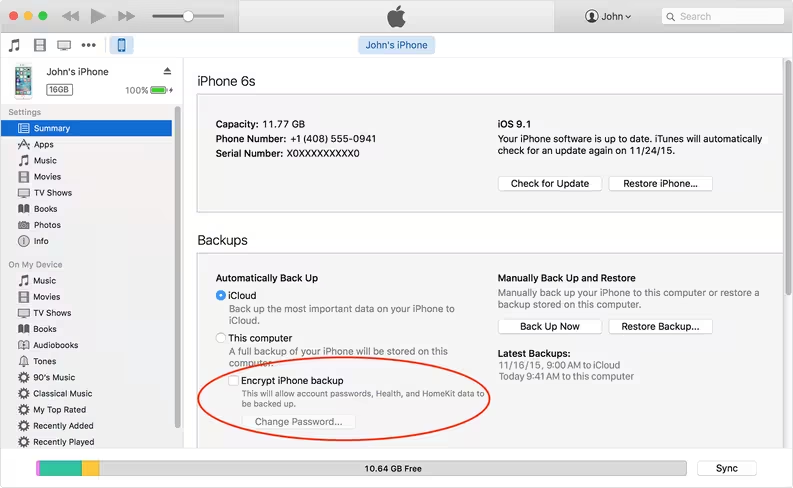
Now, you can store the encrypted backup file in iCloud, Dropbox, Google Drive, or any other cloud storage provider, or locally on your hard drive.
Additional considerations
The steps above are all reasonably easy changes to make and none require a significant shift in user behavior. They’re also going to prove remarkably efficient at keeping attackers out of your iPhone.
From here, the only common vulnerabilities are going to be from third-party applications, malware or perhaps a Bluetooth exploit, but the latter is said to have been fixed in iOS 9.
Stingrays are also a real threat, but even they can’t decrypt files within an iPhone. Instead, they trick your phone into believing it’s connecting to a cell tower and then handing over call and messaging data.
If you’re worried about bulk data collection tools, like the Stingray, you can avoid calls, email or sending text messages and instead opt for a secure messaging app that uses end-to-end encryption, such as Signal or ChatSecure.
Again, no security solution is perfect but if you were looking to protect your information, while not significantly altering usage behavior, we hope these steps will help.
Get the TNW newsletter
Get the most important tech news in your inbox each week.