Next week, Obama is expected to unveil an update to the US’ CFAA law against hacking in a State of the Union address, hot on the tail of Sony’s massive hacking attack that unfolded in late 2014.
A draft version of the new law has been published on the White House website and gives us a look into a scary future in which clicking a single link could make you complicit in committing a hacking crime.
A letter accompanying the proposal dated January 13 introduces the new law to Congress for discussion.
Remember when Sony wanted to sue Twitter (and individual users) who posted screenshots or links to its stolen data? According to Errata Security, these new laws could pin you as a “racketeer” who willingly participated in hacking if you were one of those users (or if you clicked one of those links); punishable by up to 10 years in jail.
Didn’t click a link? There are plenty of other ways you could be in legal trouble; Errata points out that something as trivial as being in an IRC channel where others are discussing a hack or having an online conversation with a “hacker” could make you a member of a “criminal enterprise,” which would allow the FBI to confiscate all your electronics.
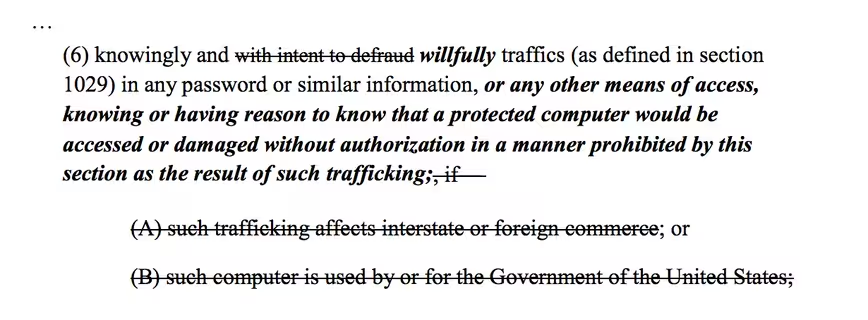
The piece of legislation also could cover data like email address and password dumps that might be found on services like Pastebin. If you accessed one of those knowingly, you could be punishable for the complete hacking offense under the draft legislation.
This is to say, that if you accessed a data leak from inside a company that was shared online by another party, the language in the updated proposal says that you would now be punishable to the same extent as those who performed the hacking themselves. That’s up to 20 years in prison, along with other potential penalties.
The proposed legislation is also worrisome for those in the penetration testing industry. I talked with Dan Tentler, a prominent computer security researcher on Twitter, who is worried that his job itself could become legally sketchy.
that literally means "Make a statement of work document for a pentest, get charged for the felony that would be the pentest"
— D̒̕ᵈăᵃn̕ᶰ Ť̾̾̓͐͒͠ᵗe͗̑́̋̂́͡ᵉn̅ᶰtᵗl̀̓͘ᶫe̓̒̂̚ᵉrʳ🫡 (@Viss) January 15, 2015
Tentler told me that even a contract that requires him to work as a penetration tester for a company that explicitly asks him to “find weak points” in the network could land him in hot water. If he performed the work and found something that the employer decided was “out of scope,” he could then be referred to law enforcement charged with multiple felonies under the proposed law.
so the whitehouse thinks that by disarming the good guys, it'll stop bad guys.
Good job, fellas.
*slow clap*— D̒̕ᵈăᵃn̕ᶰ Ť̾̾̓͐͒͠ᵗe͗̑́̋̂́͡ᵉn̅ᶰtᵗl̀̓͘ᶫe̓̒̂̚ᵉrʳ🫡 (@Viss) January 15, 2015
Obama’s proposal — which is expected to be made next week — has a few major hurdles to make it into actual law, but it’s cause for concern that even a draft is so broad about the definition of hacking itself and who can be held accountable for it.
Tentler expressed concerns that the definition of “protected computer” is so vague that it could be stretched to almost anything. Is a “protected computer” one that is wide open to the internet with minimal security? Or does simply having a basic firewall enabled imply protection?
The Washington Post expressed similar concerns, citing that it’s hard to define when a computer is protected if information is available online, without hindrance.
The wording could make almost anyone who found themselves stumbling over data they shouldn’t — let alone those that make a living searching for and reporting security flaws — liable for a crime they didn’t commit.
Errata Security also pointed out in its blog that “most hacking is international and anonymous” and says the government “can’t catch the perpetrators no matter how much they criminalize the activities.” He believes that instead, “while Obama’s new laws will dramatically increase hacking prosecutions, they’ll be of largely innocent people rather than the real hackers that matter.”
The story of Weev’s imprisonment in 2013 for accessing and sharing data that wasn’t properly protected shows how vague laws can be a problem in a world where companies often aren’t being held responsible for customer data.
Since it’s still early days for the law, it’s hard to say what the implications truly could be, but if it’s as broad as it appears, it could put people in danger unwittingly. Cyber security legislation is important in the wake of the Sony hack, but this doesn’t appear to be the right way to go about it.
Get the TNW newsletter
Get the most important tech news in your inbox each week.