SNCB Europe, the national railway operator in Belgium, over the weekend saw data of over 1.46 million of its customers leak out into the public space. The details, most of which belonged to customers in Belgium, France, and the UK, included first names, last names, genders, dates of birth, email addresses and, in some cases, home addresses and phone numbers. Unfortunately, SNCB has not apologized for its mistake and has simply proceeded to shoot the messenger that exposed the leak.
All this information was first spotted on Saturday by an ADSL-BC forum user who goes by the name Megatroll. He says he stumbled on the link to the file via Google, and reports suggests he used the query “inurl:b-europe.com filetype:txt.” Megatroll eventually removed the link from his forum post, but not before the data was quickly downloaded by many once it was made clear the file was publicly accessible.
RTL first reported the leak and received the following curious statement from SNCB spokesperson Thierry Ney (translated from French with Google Translate and my own edits):
There was indeed a list that was visible on the Internet which contained personal data of customers, such as their home addresses or e-mail addresses. This list was used to send best wishes to certain customers. In any case, it should not have been made public. In this case, a person tried and managed to get a hold of data belonging to the SNCB. He had to use a technique to get it as this data is not normally accessible to all users of our website.
We’re sorry Ney, but that’s a very poor statement. Your company made a mistake. SNCB Europe should apologize for leaking its customers’ personal details, and promise to do everything in its power to ensure it doesn’t happen again.
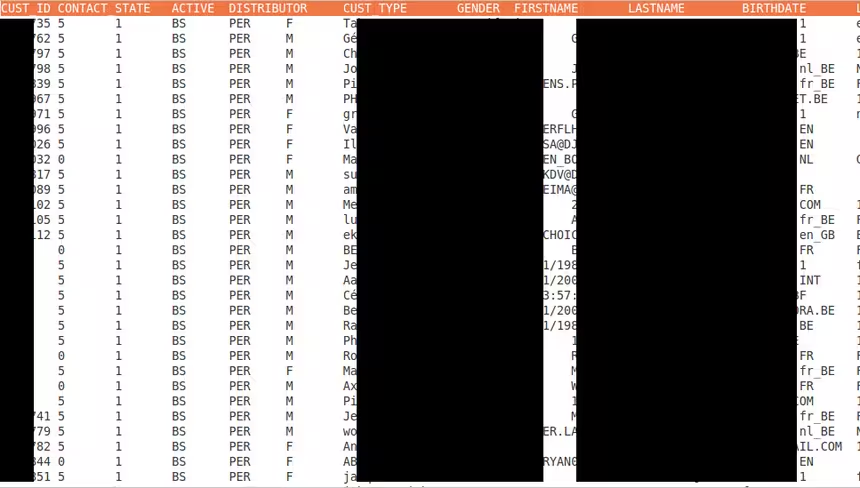
Nurpa examined the data, saying the 181.6MB text file contained the details of exactly 1,460,735 people. It looked like this:
A file available on the Internet is not “private” simply because its URL is not revealed; it is only private on the Internet if its access is restricted by some sort of authentication requirement.
Image credit: Piotr Lewandowski
Get the TNW newsletter
Get the most important tech news in your inbox each week.