Last week we discovered that the owner of SEOnix.org hacked in to our backend and threw himself a sweet SEO party. The only invitee was obviously his own website, but he still managed to have a good time all alone. In the last 3 months he got a couple of nice gifts from us in the form of juicy links and an occasional canonical tag.
But it wasn’t only us. He managed to do the same on other authorative sites as well. We’re leaving the names out to protect the innocent. In total he has injected several hundred posts, getting links from 25 domains, most of which it’s safe to assume weren’t earned like you or I would earn them.
So What Happened?
This person managed to get in via one of our editors’ logins and put links to his own site in 124 posts. And not just links; he went on to add some nice anchor texts like ‘search engine optimization’, ‘SEO’ or ‘movie downloads’. But it wasn’t just a matter of inserting links, he also scraped content from our site, as well as many others.
Content scraping is nothing new, and it happens to us all the time. But usually scrapers aren’t able to change the canonical links on the site they scrape. This guy obviously was. In doing so, what he essentially accomplished was to tell Google and other search engines that our post wasn’t the original, and in fact his own was.
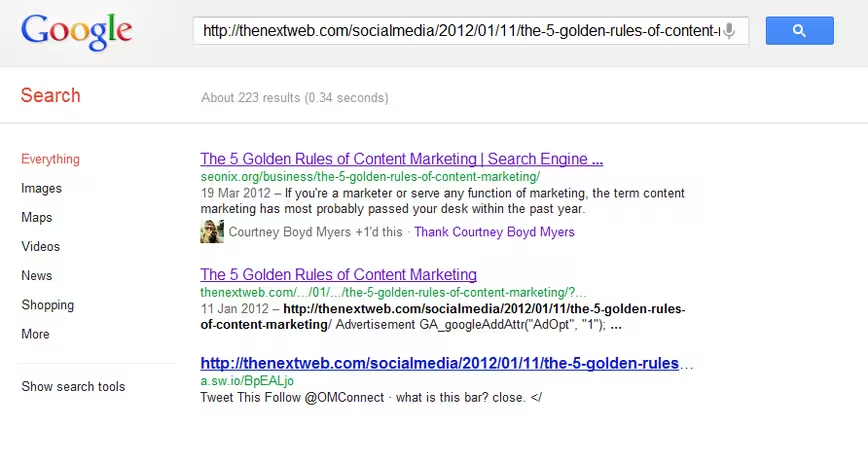
Here’s a good example – when searching on one of the URLs from TNW you see his post is at the number 1 position not ours. And Google Plus even gave the +1 from our beloved Courtney to the hacker’s post while in reality she gave it to ours.
 Get Greedy, Get Caught
Get Greedy, Get Caught
We luckily discovered this because the swell fella got enthusiastic and put links in places where we never do – like in the title of one of the posts, linking ‘social media’ to one of his categories. When seeing it for the first time, we thought “well that’s a nice SEO present to give, but why would we do that?”
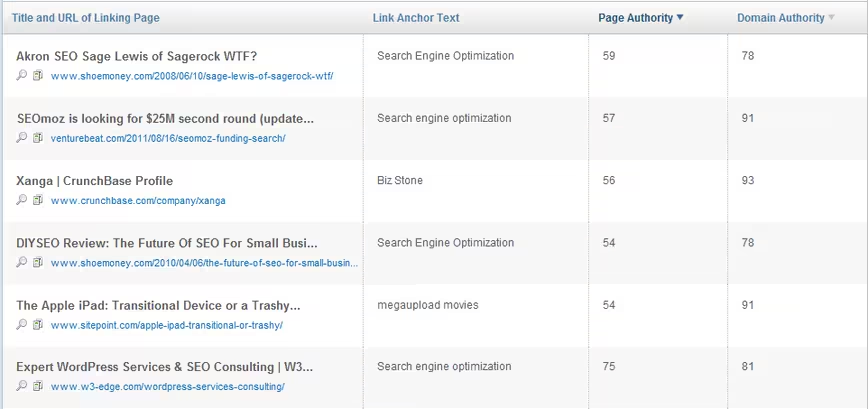
So we looked into it and found the rest of the posts with nicely-chosen anchors. After some more searching we saw other sites linking to him as well and it didn’t seem that they did so on their own. Below is a snapshot from SEOmoz Open Site Explorer of domains linking to SEOnix.org, with anchor text and the authority per page and domain.
We can look back at this now and have a laugh, but we honestly felt very stupid when we discovered this. Luckily the hacker had limited privileges with this editor login, so the damage isn’t that severe. But still it didn’t feel less awkward, even when you discover other big sites were attacked as well.
We informed all the other sites that we found and shared information with them. One other site tells us that the hacker was able to get himself an account with the user lists, while another says that there are some security points that his site normally has in place which hadn’t yet been implemented after a server switch.
Ultimately we’ll chalk this up to a learning experience, and we’ve indeed gained some valuable knowledge from trying to find the holes and how to keep them closed (thanks to W3-edge as well). For obvious reasons we can’t go into all of the details as to how we plan to prevent things like this from happening in the future.
We’ll be keeping a close eye on every aspect of the site, including user accounts. Password security is a serious thing, so if you manage a site with multiple users, do your level best to keep that first door tightly closed.
See also: Google rolls out a refresh to its Panda search update, affects only 1.6% of queries
Get the TNW newsletter
Get the most important tech news in your inbox each week.