A security hole has been discovered that allows anyone to see the email addresses corresponding to certain Facebook accounts. Worse yet, some appear to be accessible without even entering a password. However, a Facebook engineer now says that the company has disabled the feature that created the hole.
We first stumbled on this via a curious submission on Hacker News that points to a Google search for the query “inurl:bcode=[*]+n_m=[*] site:facebook.com.” The results pages reference direct links to an apparent 1.35 million personal Facebook accounts, and their corresponding email addresses embedded in the actual URL, although we could only get Google to display the first 590.
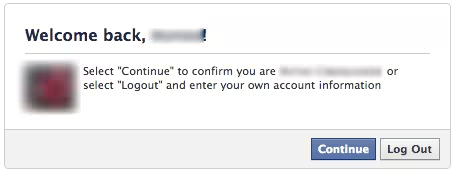
It appears that each of these links are temporary ones meant for a given Facebook user. If you click on it, it automatically expires. Since many users have already clicked on many of these links, most of them give you the person’s email address and prompt you for the corresponding password, as you can see in the screenshot below:
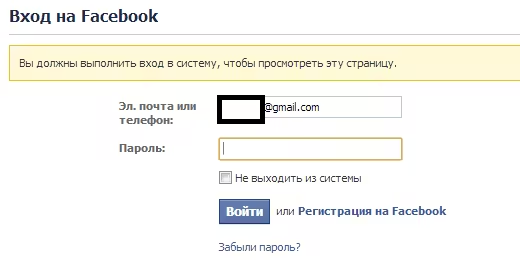 Some of them, as they have yet to be clicked, don’t ask you for a password at all. They let you go straight through to the person’s account:
Some of them, as they have yet to be clicked, don’t ask you for a password at all. They let you go straight through to the person’s account:
A lot of the accounts appear to be Chinese or Russian. Since it is a violation to access them, we have not done so and cannot verify if these are fake accounts or real Facebook users.
Hacker News member ‘nico-roddz’ initially shared the discovery and later elaborated on how it happened:
“This is how everything started: A friend forward me an email from a FB group notification. Something like:
http://www.facebook.com/n/?groups%[id here]%2Fpermalink%[id here]%2F&mid=[id here]&bcode=[id here]-mjoi&n_m=[email adress here]
When I clicked the url I got automatically logged into my friend’s account. So is definitely a Facebook security issue. Then I tried some Google searches to see if I could find some urls containing the parameters: ‘bcode= &email= n_m= mid=‘. Not a big deal, really.”
The best case scenario is that someone will click on such a link and not know your password, but will get your email address. The worst case scenario is that someone can access your Facebook account on the first try. Since the email addresses are in the URL, someone could potentially search for your email address and find the corresponding link that has yet to expire.
Facebook disables the feature
Matt Jones, a Facebook engineer with a history of discussing such issues on Hacker News, has now contributed to the thread, explaining that the company has investigated this following the discovery. He says that Facebook only sends these URLs to the email address of the account owner “for their ease of use and never make(s) them publicly available. Even then we put protection in place to reduce the likelihood that anyone else could click through to the account.”
Jones explains, “For a search engine to come across these links, the content of the emails would need to have been posted online (e.g. via throwaway email sites, as someone pointed out – or people whose email addresses go to email lists with online archives).”
He notes that they expire after a period of time and only work for certain users. “Even then we run additional security checks to make sure it looks like the account owner who’s logging in.”
Jones then notes that due to the disclosure of these links via Google search results, Facebook has turned this feature off until it can better ensure its security for users whose email contents are publicly visible. He also notes that Facebook is securing the accounts of anyone who recently logged in through this flow.
We have contacted Facebook for official comment about this issue. We will update this article if and when we hear back.
Update at 12:00PM EST: “These URLs were sent directly to private email addresses to help people easily access their accounts, and we never made them publicly available or crawlable,” a Facebook spokesperson said in a statement. “These URLs were subsequently posted elsewhere online, which lead to their indexing in search engines. While we have always had protections on these private links to provide an additional layer of security, we have since disabled their functionality completely and are remediating the accounts of anyone who recently used this feature.”
Image credit: AFP / Getty Images
Get the TNW newsletter
Get the most important tech news in your inbox each week.