
Researchers have found serious security vulnerabilities in over 600,000 GPS trackers available for sale on Amazon and other online retail merchants that may have exposed user data, including the exact real-time GPS coordinates.
Czech cybersecurity firm Avast, which disclosed the vulnerabilities, said it informed the manufacturer about the flaws on June 24, 2019, but added they never got a response to their repeated messages.
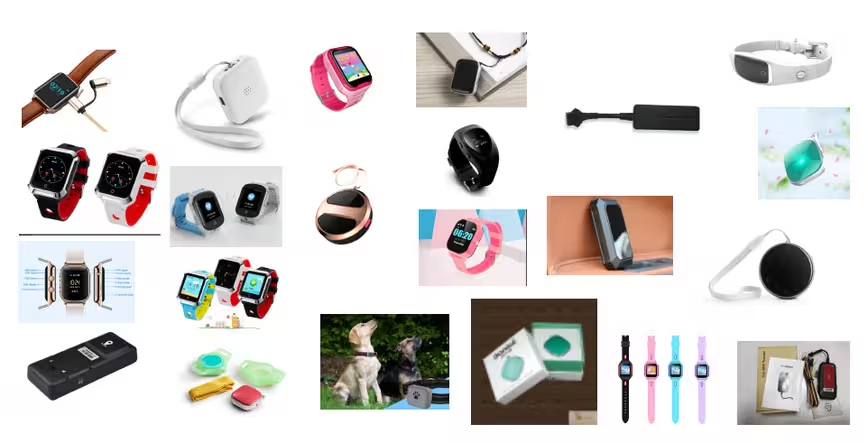
The trackers — 31 models in all that are made by Chinese IoT manufacturer Shenzhen i365 Tech — allowed users to keep tabs on their childrens’ whereabouts through a companion app and a web portal, while the trackers uploaded the location information to a cloud server that communicated with the apps.
But researchers noted this setup was replete with flaws. Not only was the information on the web portal and the Android app sent to the server unencrypted (i.e. HTTP as opposed to HTTPS), the usernames were based on the trackers’ IMEI (International Mobile Equipment Identity) number, with the default password being “123456.”
Avast warned that hackers can use this information to intercept data and issue unauthorized commands, using the tracker to call and message arbitrary phone numbers, thereby letting them spy on conversations around the tracker without the user’s knowledge.
In addition, this can also allow a malicious user to take over victims’ accounts by going through the trackers’ IMEI codes in sequence and the same password “123456,” effectively locking them out. The attacker can even get the real-time GPS coordinates by just sending an SMS to the phone number associated with the SIM card that’s inserted into the tracker.
Conveniently for the threat actor, the account settings make it possible for the attacker to force “the tracker [to] send an SMS to a phone number of a phone in his possession which allows him to tie the ID of a tracker with its phone number.”
Scanning a random sample of four million sequential IMEI numbers, the researchers zeroed on at least 600,000 devices still in use with default passwords, out of which over 167,000 were locatable.
Although the trackers were manufactured in China, Avast found the trackers to be widely used in Europe, South Africa, Australia, Brazil, the Middle East, and the US.
This is not the first time a flaw of this nature has been revealed. Back in May, UK cybersecurity firm Fidus Information Security revealed a vulnerability in a popular GPS tracker used by elderly patients that can be tricked into sending its real-time location simply by sending it a text message with a specific command.
As a consequence, the UK is considering laws that would mandate internet-connected gadgets to be sold with a unique password, and not a default.
GPS tracking devices are often used for a variety of purposes, from locating family members to pets, and from cars to valuables such as keys. Given that the issue exists to this day, it’s yet another cautionary reminder as to why you should change default passwords.
Get the TNW newsletter
Get the most important tech news in your inbox each week.



