
The GitHub account of Canonical Ltd., the company behind the popular Ubuntu Linux distribution, was hacked over the weekend on July 6.
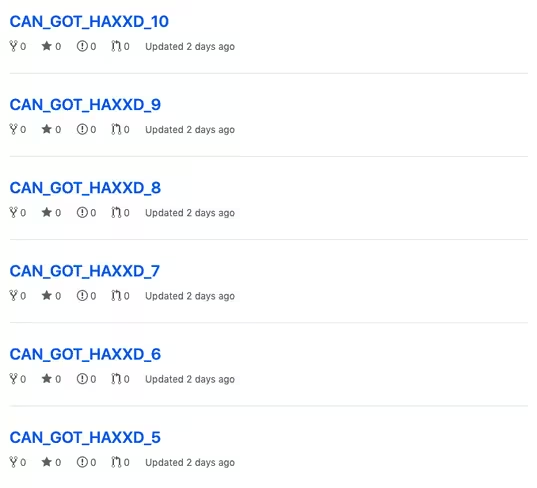
While the hacker‘s identity remains unknown, they managed to compromise the account’s credentials to create 11 new empty repositories. The repositories were named “CAN_GOT_HAXXD.”
“We can confirm that on 2019-07-06 there was a Canonical owned account on GitHub whose credentials were compromised and used to create repositories and issues among other activities,” Ubuntu Security team said in a statement.
Canonical said it has removed the compromised account from the Canonical organization in GitHub and that it’s still investigating the extent of the breach. But it has established there’s no evidence that any source code or personally identifiable information was affected.
Although the hack has proved to be less scary than originally thought, this is not the first time Canonical and makers of other Linux distros have been a victim of a breach.
Attackers managed to get away with personal details of millions of users on its official Ubuntu forums in two separate incidents in 2013 and 2016.
We can confirm that on 2019-07-06 there was a Canonical owned account on GitHub whose credentials were compromised and used to create repositories and issues among other activities. Canonical has removed the compromised account from the Canonical organisation in GitHub and
— Ubuntu Security (@ubuntu_sec) July 7, 2019
Linux Mint suffered a major incident in 2016 after hackers created a modified version of its Linux distribution with a backdoor, and hacked its website to point to it. Then last year, Gentoo Linux distribution’s GitHub account — which is used as a base for Google’s Chrome OS — was hacked, and its code was replaced with malware.
Ubuntu has confirmed it uses Launchpad to host, build and maintain its codebase, that it’s disconnected from GitHub and that there have been no indications that it has been affected.
It also plans to publish a public update once it completes its investigation into the incident, and after it carries out an audit and any other required remediations.
Update on July 11 9:00 AM IST: Ubuntu’s security team has once again confirmed there’s no evidence of further compromise than originally disclosed. “We are still investigating but at this time we see no other indicators of compromise that would suggest access beyond our original disclosure,” the company said.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




