It’s not been a great week for security, and after Twitter, WhatsApp and Intel, Google has now joined the list.
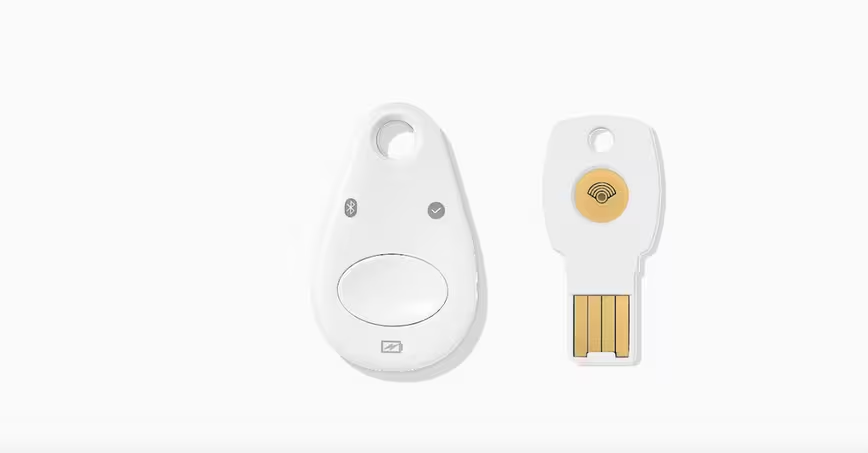
The internet giant has issued an advisory, stating it is recalling Bluetooth versions of its Titan Security Key after it found a vulnerability that allows attackers in close proximity to take control of the device.
The issue, which affects all Titan Bluetooth keys that have a “T1” or “T2” on the back, has been deemed serious enough that it’s willing to offer a free replacement for those who purchased them.
If you are one among those affected, you can head to google.com/replacemykey to replace your faulty key.
“This bug affects Bluetooth pairing only, so non-Bluetooth security keys are not affected. Current users of Bluetooth Titan Security Keys should continue to use their existing keys while waiting for a replacement, since security keys provide the strongest protection against phishing,” Google said in a statement.
That’s a bummer for owners of Google’s $50 security offering, which was launched in the US last July. The USB-based dongle, which is small enough to fit on your keychain, offers an additional layer of authentication and protects your Google accounts from phishing attacks and account takeovers by unauthorized parties.
Enabling Bluetooth makes these far more convenient to use (no plugging them in when you need to access your account), but it looks like even the big G couldn’t make the devices safe enough to use wirelessly.
A remote hijack flaw
The flaw stems from a misconfiguration in the Titan Security Keys’ Bluetooth pairing protocols, making it “possible for an attacker who is physically close to you at the moment you use your security key” to communicate both with your security key and the device it’s paired to.
However to exploit the flaw, an attacker would have to be within 30 feet of your key, and quickly connect their own device to your key even before your device connects to it soon after activation.
Succeeding in this attempt, and assuming they already have your username and password details, the attacker will be able to sign in to your account and take over control.
A separate vulnerability takes advantage of the pairing mechanism, the post noted. This allows the remote attacker to masquerade their device as your security key and connect to your device when you press the button on the key.
In doing so, they can change their device to appear as a Bluetooth keyboard or mouse, and use it to run malicious commands to hijack your device.
Concerns with Bluetooth-based authentication
“This security issue does not affect the primary purpose of security keys, which is to protect you against phishing by a remote attacker,” it pointed out in the blog post, and stressed that “it is still safer to use a key that has this issue” than completely turning off security key-based two-step verification for your Google Account.
Although Google has said it is not aware of this exploit being used to gain access to user accounts, the incident highlights the security issues that could arise from using Bluetooth-enabled security keys.
Yubico, which leads the passwordless authentication efforts along with Google and Microsoft, had expressed similar concerns when Titan was announced last year.
“Google’s offering includes a Bluetooth (BLE) capable key,” wrote Yubico founder Stina Ehrensvard in a post. “While Yubico previously initiated development of a BLE security key, and contributed to the BLE U2F standards work, we decided not to launch the product as it does not meet our standards for security, usability and durability. BLE does not provide the security assurance levels of NFC and USB, and requires batteries and pairing that offer a poor user experience,” she added.
Getting the key replaced
While you wait for your replacement key to arrive, Google is recommending that you continue to use your security key, but minimize the security risk by using it in a private place where a potential attacker is not within close physical proximity. It is also suggesting you immediately unpair it after signing in to your Google Account.
Google however cautioned that iOS 12.3, which Apple started rolling out on Monday, won’t work with vulnerable security keys. Hence to prevent your accounts from getting locked out, the company is recommending you do not sign out of your account until you get hold of a new key.
An alternative option would be to turn off key-based verification, and just use an authenticator app as the primary means of two-factor authentication in the meantime.
Get the TNW newsletter
Get the most important tech news in your inbox each week.