Cross-site scripting (XSS) is common vulnerability found in web applications. The way it works is pretty easy to grasp. A website will take a text input – this could be anything from a post on a guestbook, to a Facebook update. The user will then pass the website a payload written in HTML and JavaScript that introduces some kind of undesired behavior.
This could be benign, like an alert that says something like “Hello World”. Or it might not be. It could redirect the user to a phishing website, or a page loaded with malware. The web application then fails to filter this payload, essentially forcing the user’s web browser to render it.
Nasty, isn’t it? As a result, most competent web developers make the effort to mitigate against these kind of attacks. But it’s extremely hard, if not impossible, to mitigate against all of them.
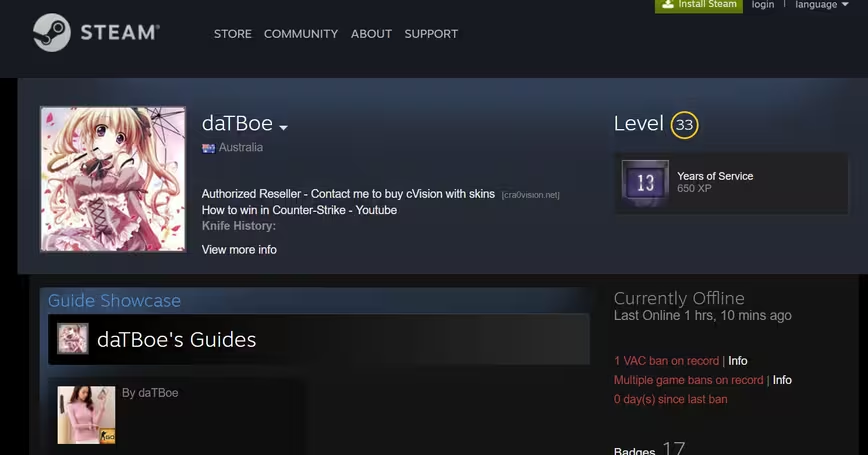
Now, one security researcher has identified a way to introduce their own arbitrary code into a Steam profile, essentially circumventing every protection Valve has created.
The researcher, Cra0kalo, has created a proof of concept that demonstrates the attack in action. If you’re curious, you can check it out here.
example one I made https://t.co/k7qjH1zgp0
— Cra0 (@cra0kalo) February 7, 2017
When you visit the page, the third-party code will attempt to download a Windows executable. As far as I can tell, this exe is pretty harmless. In a tweet, Cra0kalo says that it’s an intro animation he made with VB6 when he was 16 (still don’t download it though). But if anyone was so inclined, it could be something malicious, like a ransomware program or any variety of virus.
We’ve reached out to Valve. We’ll update this post when we hear back from them, or if the issue is fixed.
UPDATE: We heard back from Doug Lombardi, VP of Marketing at Valve. According to Lombardi, the issue has been resolved.
Get the TNW newsletter
Get the most important tech news in your inbox each week.





