![A massive DDOS attack against Dyn DNS is causing havoc online [Update: Resolved]](https://media.thenextweb.com/2016/10/dns-ddos.avif)
A distributed denial of service (DDoS) attack against DynDNS is causing havoc online, with many major websites reportedly unavailable. According to Dyn DNS, the attack started at 11:10 UTC, and it targeted its managed DNS service.
The Domain Name System (DNS) is a tool used to resolve human-readable web addresses (like “thenextweb.com”) against IP addresses.
Many sites and services use DynDNS as their upstream DNS provider, including Github, Twitter, SaneBox, Reddit, AirBnB, and Heroku. All of these are reportedly experiencing outages and downtime, either partially or totally.

It’s not immediately obvious who is behind this DDoS attack. However, the fact that the attackers were able to disrupt the DNS provider used by some of the most popular websites tells a lot about their abilities.
Update [18:29 ET]: Dyn says the DDoS ‘incident has been resolved’ after the third attack. Indeed, all affected sites we tried seem to be working now. Here’s to hoping that the end of it.
Update [17:09 ET]: Dyn is now saying that a large swath of the attacks are coming from “Internet of Things” devices like printers and appliances that send information to the web, according to CNBC. The attack is coming from devices “infected with malware code released on the Web in recent weeks.”
Internet of things devices have previously been targeted because many of them feature poor security protocols.
Dyn does not yet know who the attackers are.
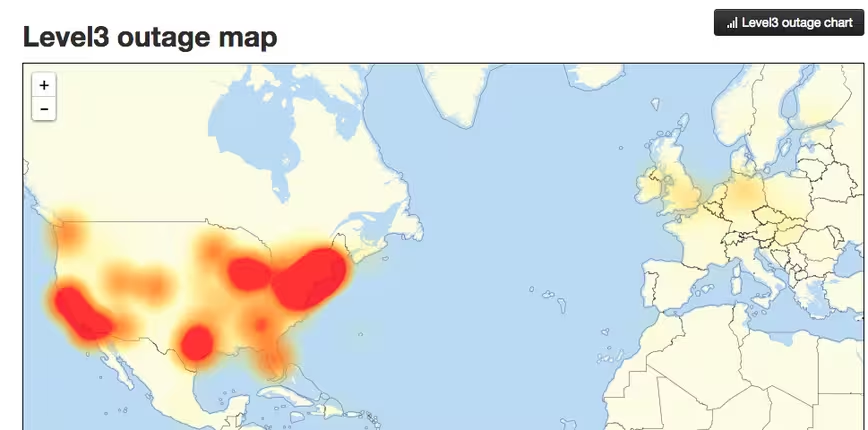
Update [16:22 ET]: There’s now a third wave attacking Dyn and it’s slowly eating up much of the country.
Update [13:35 ET]: Some have pointed out that switching to OpenDNS is a good way to mitigate the effect of the DDoS.
DNS not working? Try a different set:
– OpenDNS 208.67.222.222, 208.67.220.220
– google: 8.8.8.8, 8.8.4.4
– Level 3: 4.2.2.1, 4.2.2.4— Jay (@coolacid) October 21, 2016
Pro-tip: OpenDNS users generally see the Internet as they should. We do a good job of handing "last known good" IPs when we can't resolve.
— David Ulevitch 🇺🇸 (@davidu) October 21, 2016
Update [13:30 ET]: Some are having issues logging into the PlayStation Network.
BREAKING: Sony's PlayStation says it is investigating issues related to users logging into its network – tweet
— Reuters Tech News (@ReutersTech) October 21, 2016
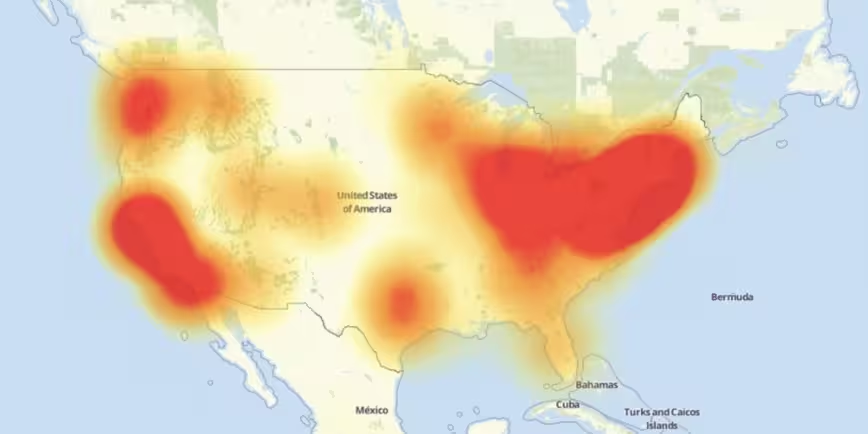
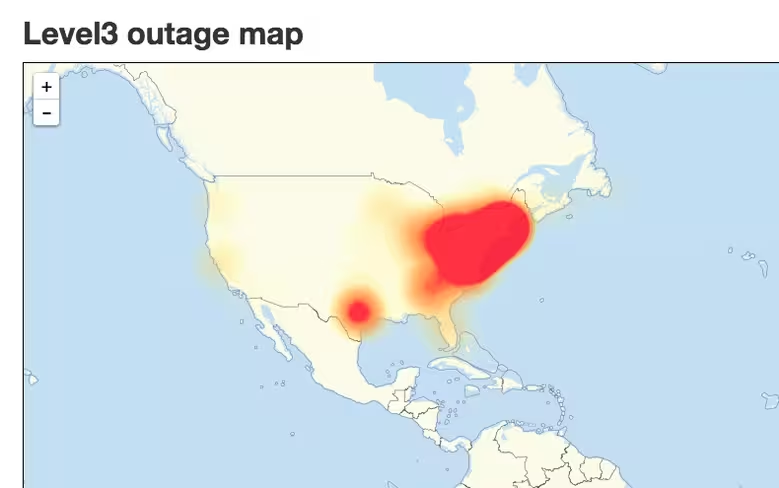
Update [13:15 ET]: This map from DownDetector illustrates the impact of the second DDoS attack against Dyn.
Update [13:00 ET]: According to CNBC, the Department of Homeland Security is investigating the attack against Dyn.
NEW: Dept. of Homeland Security tells CNBC it is "looking into" attack against internet traffic firm Dyn https://t.co/wjKOxJ9Eo8
— CNBC (@CNBC) October 21, 2016
Update [12:29 ET]: Dyn told TechCrunch it is experiencing another attack. Services seem to be hit or miss currently.
The DNS provider that suffered a DDoS attack causing widespread outages this AM says it’s facing another one https://t.co/aTcZbUvPHJ
— TechCrunch (@TechCrunch) October 21, 2016
Update [09:44 ET]: I just received direct confirmation from Dyn that normal service has been restored. Affected sites should be returning back to normal.
Update [09:41 ET]: CNBC is reporting that Dyn has restored service.
Update [09:17 ET]: Scott Hilton, EVP, Products at Dyn has issued a statement:
This morning, October 21, Dyn received a global DDoS attack on our Managed DNS infrastructure in the east coast of the United States. DNS traffic resolved from east coast name server locations are experiencing a service degradation or intermittent interruption during this time. Updates will be posted as information becomes available.
Upon recognition, active mitigation protocols were initiated and have been working to resolve the issues.
Customers with questions or concerns are encouraged to check our status page for updates and reach out to our Technical Support Team.
Update [09:13 ET]: This outage is mostly affecting users in the East Coast of the US, as illustrated by this heat map from Downdetector.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




