Two academics have been given permission to publish their security research which reveals vulnerabilities in a wireless car locking system. It comes two years after Volkswagen, one of the manufacturers using it, won a court injunction banning publication.
Despite a court order in its favour, Volkswagen has now allowed the report to be republished with only minor redactions. However the case reveals the tension between security researchers and software firms, or in this case the software used by car manufacturers. While some firms such as Facebook, Google and Microsoft offer financial rewards for those finding bugs, others such as Fiat Chrysler assert that such activity is criminal or as Volkswagen did, take it to the courts – while failing to address the highlighted problems that expose their customers to risks.
The car industry may feel bullied just now, but Volkswagen’s approach of using the courts to try to keep information about a key flaw under wraps is the equivalent of sticking your fingers in your ears and hoping everything will turn out well. This is a serious issue, one that is too important for the brute force of court rulings. In any case, the internet has little respect for national boundaries or court jurisdictions, and the information was available online regardless of the court’s ruling.
Knock knock, come in
The Megamos transponder wireless key.
Verdult/Ege/Garcia
The encryption used in the Swiss-made Megamos transponder is so weak that an intruder needs only listen to two messages transmitted from the fob in order to crack the key. The vulnerability relates to the poor, proprietary cryptographic methods used by the device, where the researchers found they could generate the transponder’s 96-bit secret key and start the car in less than half an hour.
This vulnerability has been well known since 2012, and code to exploit the flaw has circulated online since 2009. Yet there has been no product recall of the dozens of models from Audi, Porsche, Bentley and Lamborghini, Nissan and Volvo it affects, and no patches released to fix its problems.
Vulnerable wireless keys are a growing problem. It is reported that 42 percent of all car break-ins in London were related to various wireless key access systems, particularly for high-value cars from BMW and Audi.
For example, the RollJam device can be bought online for £20 and opens many well-known brands of cars – it “jams” the wireless signal twice when the user uses their key, and then is able to grab the access code for the car. It also opens most garage doors and disables some alarm systems.
A universal canopener, the RollJam device opens cars easily.
RollJam
Academic freedom vs industry interests
The researchers who have now been permitted to publish, Roel Verdult and Barıs Ege of Radboud University in the Netherlands and Flavoi D Garcia of the University of Birmingham, approached the manufacturer in May 2012, explaining that they intended to present their findings at the USENIX 2013 conference, giving the manufacturer plenty of time to produce a fix for the problem. Instead Volkswagen used the courts to block publication of the paper, pitting the prevention of the potential insecurity of Volkswagen cars against the freedom of academic publishing.
The scope of the patching required to fix Megamos’ problems would be enormous, as there is no simple update to replace the weak propriety cryptography at the heart of the problem. Clearly this was an incentive for Volkswagen to seek an injunction, but doing so hasn’t made the vehicles any more secure, nor has it prevented the information circulating on the internet.
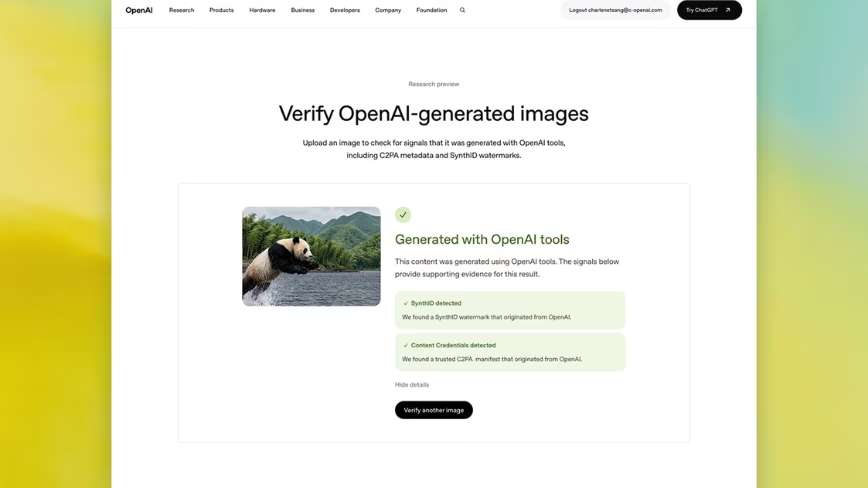
Table of models affected (bold indicates models the researchers tested).
Verdult/Ege/Garcia
Other manufacturers have been stung too – Ford recalled 433,000 Focus, C-MAX and Escape vehicles due to a software bug where drivers could not switch off their engines. And recently a security researcher showed how BMW cars could be breached by sending commands that told the cars to open their doors and lower their windows, leading BMW to issue a patch for over 2m BMW, Mini and Rolls-Royce vehicles.
But this case was avoidable: the Megamos vulnerability was one of poor design and implementation – using poor-quality, home-brewed encryption instead of one of the many common standards that would have proved far more impenetrable. This should have been reviewed as part of the due diligence process in evaluating the designs. Were they published, someone in the industry could have pointed out their flaws. Yet it’s this same process of research, publication and evaluation common in academia that Volkswagen tried to prevent.
This a sorry tale of responsible disclosure by academics followed by a gagging order, and ultimately for the problem to go unfixed. Unless the car industry takes this problem seriously, designs and tests systems properly before release then they will be weighed down by the costs of recall and repair and fines from regulators.
While some hunt vulnerabilities for glory, the researchers in this case were responsible and gave the companies involved a good amount of time to deal the problem before the paper was due to be published. While many in cryptography have faced pressures not to publish, such as government efforts to suppress Ron Rivest’s work on public key encryption, academic freedom to publish and review responsibly is a key part of how mistakes are discovered and how knowledge progresses.
Read Next: Google launches a central hub for your security and privacy settings
Image credit: Shutterstock
Bill Buchanan is Head, Centre for Distributed Computing, Networks and Security at Edinburgh Napier University
This article was originally published on The Conversation. Read the original article.
Get the TNW newsletter
Get the most important tech news in your inbox each week.