One of the most harrowing tales of security woe in recent memory is that of Mat Honan, clearly a tech-savvy guy, who had a hacker call Apple and use social engineering gain access to his Amazon and iCloud accounts, and thus wound up losing a ton of data on his Mac, iPhone and iPad plus his primary Google account.
Apple has since quit allowing iCloud password resets over the phone, but it wasn’t merely social engineering which allowed Honan’s account to be so thoroughly hijacked. Mat didn’t use Google’s 2-step authentication, which requires you to use a password and a text message to your phone to verify who you are. This one simple thing could have saved him from losing a year’s worth of photos of his daughter.
Unfortunately, 2-step authentication is rare among web services like Gmail. Banks will often use it, as do companies who subcontract through RSA, makers of the SecurID (which was notoriously hacked some time ago). Amazon offers a security fob for AWS customers, but if you want to reset your password the most you’ll have to fight off is a captcha. Like most websites, Amazon just sends a reset link to the email you have on file. If that email were compromised, your account would be too. On Monday Amazon also quit allowing customers to call in to reset their passwords.
As it’s best described, 2-step, or 2-factor authentication, uses something you know (a password) and something you have (a phone). Matt Cutts breaks it down in this video.
Be careful that you aren’t sending texts to a phone that is actually a Google Voice number being used by the same account! Think about it: if someone has access to your email, sending a text to that same email by way of Google Voice wouldn’t really lock them out, would it? What you need are two separate systems. That’s why many security vendors use those little fobs with the numbers that eternally change — those are generated to be the failsafe, backup key which verifies who you are because a bad guy would have to have physical access to that fob to know the numbers.
It’s nice to hear Apple and Amazon plugging holes, but in the end security (and backups!) are our responsibility. I think it’s important that Google uses a 2-step authentication, and I suggest you set it up now. Dropbox has promised it will implement 2-step authentication, and after Honan’s experience I’m guessing a ton of others will, too.
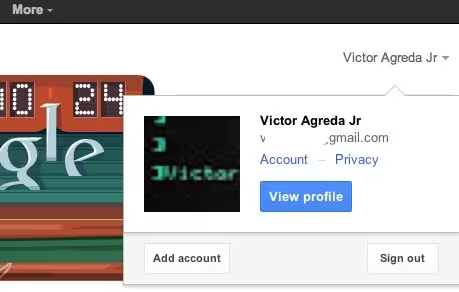
Google has instructions to enable 2-step authentication now, but make sure you’re near the phone you want to tie into your account. It’s quite simple: log in to your account, go to your settings by clicking your name and go to Account. On the right there’s a button for Security, and there you can see if you have 2-step auth turned on. If not, click Edit and set it up now. You’ll be glad you did!
Get the TNW newsletter
Get the most important tech news in your inbox each week.