As smart devices continue to replace countless physical objects such as books, cameras, GPS systems and even ATM’s, keeping our sensitive information away from hackers is a topic worth heavy investment.
While biometric authentication like fingerprint scanning and facial recognition are currently considered the safest authentication systems on the market, scientists have found that our own sweat might hold the key to a more secure future.
Research conducted by scientists from the University of Albany suggests that by monitoring our own sweaty skin secretions, a unique amino acid profile can be built that accurately and securely authenticates our identity. Jan Halamek, an assistant professor at the university explains:
We are developing a new form of security that could completely change the authentication process for electronic devices. Using sweat as an identifier cannot be easily mimicked or hacked by potential intruders. It is close to “full-proof.”
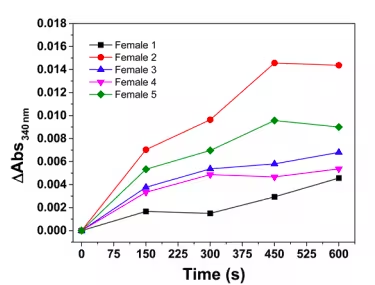
To build a profile capable of identifying us, a small sensor is placed on a device, such as a smartphone, to monitor our sweat levels during various activities. Samples are taken from the skin on our fingers that are full of eccrine glands: a type of sweat gland with a high density on our palms.
Results have proven that the concentration of various components in our sweat is controlled by reactions regulated by our hormones. As hormone levels vary according to our age, sex, race, and lifestyle, researchers concluded that no two people can possess the same profile.
For an added layer of security, by pre-monitoring concentrations of the ingredients in our sweat over time during various actions, patterns specific to each of us can be recorded and compared against.
Using sweat to authenticate devices could make life easier for those with certain disabilities and you would never have to remember a passcode again. As Halamek explains, this new approach was developed to overcome the many shortfalls of the authentication systems we presently use:
The current forms of authentication have proven to be less than ideal. Passwords and pins can easily be seen over someone’s shoulder and there are many internet tutorials on how to create a fingerprint mold that is capable of opening a device. There are also issues with facial recognition, which often, at times does not work correctly.
As we use our devices for more and more each day, it’s critical that security measures keep up to protect the growing amount of personal information we keep stored. While sweating on my device did initially sound like a gross way to gain access, it turns out I do it anyway, without even realizing. So here’s to a secure (and sweaty) future.
Get the TNW newsletter
Get the most important tech news in your inbox each week.