We’ve seen elaborate Twitter scams before, but this new one spotted by Panda Security takes the cake. It manages to combine a racist tweet about US President Barack Obama as well as fake Facebook and YouTube pages, all in the hopes of stealing your Twitter credentials (user name and password) as well as serving up malware to infect your computer.
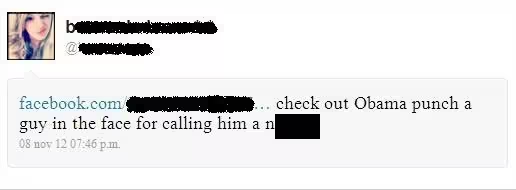
Here’s the message in question (we’ve chosen to block out the racist slur):
If the user clicks on the fake link, they are taken to a bogus Facebook page where they are asked to enter their Twitter login details. If you are hit by this scam, please don’t enter your Twitter credentials. If you do, your account will be hijacked and will in turn start sending the same malicious message to all your contacts.
The scam doesn’t end there. Once the victim has handed over their Twitter user name and password, they are taken to another bogus Facebook page, this time with a fake YouTube page embedded within.
This time, you are asked to update your “YouTube player” to watch the video. Again, please don’t do this. If you do click on the blue “Install” button, you will end up downloading the Koobface.LP worm, which will infect your computer and steal all your personal data.
Luis Corrons, technical director of PandaLabs, explains why this scam is so effective:
This attack exploits the two most popular social networking sites, Facebook and Twitter, to trick users into believing they are viewing a trusted site. It also relies on its victims’ curiosity by using a scandalous story involving U.S. President Barack Obama and racism. Cyber-criminals know people are curious by nature and take advantage of this to trick users and infect them with their creations.
If the Koobface name sounds familiar to you, that’s because its name is an anagram of “Facebook” and the computer worm originally targeted Facebook users. First detected in December 2008, the worm also spread on social networks Twitter, MySpace, hi5, Bebo, and Friendster. Koobface was designed to infect Windows and OS X users, but it also worked in a limited fashion on Linux.
Eventually, later versions stopped targeting these sites because they improved their security. It’s unclear if we are seeing cybercriminals trying to give Koobface another go, but this one is definitely an elaborate attempt.
We do know, however, that Facebook shared information about the Koobface gang and named those it believed were responsible for its creation in January 2012: Stanislav Avdeyko (leDed), Alexander Koltyshev (Floppy), Anton Korotchenko (KrotReal), Roman P. Koturbach (PoMuc), and Svyatoslav E. Polichuck (PsViat and PsycoMan). The group, referred to as Ali Baba & 4 with Stanislav Avdeyko as the leader, or just the Koobface gang, are based in St. Petersburg, Russia.
For Facebook and Twitter users currently seeing this scam, I recommend that you don’t click on links attached to dubious messages. Every time you receive a tweet or direct message that looks suspicious, check with the sender to make sure they knowingly sent it to you, especially if it contains a link.
See also – Security firm Sophos reveals how it caught the gang behind Facebook malware, Koobface
Image credit: Christa Richert
Get the TNW newsletter
Get the most important tech news in your inbox each week.