It’s hard to believe, but the most popular password in 2018 was – get ready for it – “123456,” the winner and still champ six years running. According to internet researchers, that simple numerical string accounted for about 4 percent of the online passwords in use during 2018.
In fact, more than 10 percent of people use one of the 25 most popular passwords on this Wikipedia page – so hackers following that as a guide have a better than one in ten chance of gaining access to a victim’s account (obviously that doesn’t include TNW readers; they’re too smart to use those easy to guess passwords).
At this point, it’s hard to imagine that there are web users who are not aware of the risks of commonly used passwords – so if more than 10 percent are using the same common passwords, it’s clear we can’t rely on people to protect themselves.
That’s one reason for the rise in multi-factor authentication (MFA) – where a website requires, in addition to a password, the insertion of a code sent via text message, the submission of a one-time password, the use of a physical token (like a dongle), or authentication via biometrics (face scan, thumbprint, etc.).
With hacking and data breaches on the rise, it’s no surprise that the market for MFA is predicted to grow fourfold by 2025. The demand for MFA is growing on both sides – both by service providers and consumers – all of whom are tired of the never-ending hack attacks we’re subjected to.
Multi multi-factors — which is best?
The question, then, is which MFA is best, and for which purpose? With the MFA landscape being so diverse, which technique will grab the lion’s share of the market?
While as mentioned there are several to choose from, as an authentication expert, I believe that the one that will capture the imaginations of both consumers and businesses is push authentication.
Push is a technology that verifies the identity of users by sending a push notification to a mobile device associated with their account during the login process – meaning that there is nothing to remember; all that needs to happen is for the device to be in the hands of the person who owns the account they are trying to access. In essence, it turns the mobile device into an authentication token.
What’s better about push?
- It’s cost-effective in terms of implementation and maintenance
- It’s more secure than other forms of MFA
- It’s easy to use and doesn’t introduce complexity to the user experience
Let’s take a look at these individually:
Cost-effectiveness
The most secure form of MFA, experts agree, is a physical token – something you have that verifies who you are. In many organizations, for example, access is granted to a building or department using a dongle that is passed over a reader. Such dongles are also used for authentication on secure websites, with the individual seeking to connect a dongle to their phone’s power connection. That’s a secure system, but an expensive one.
With push, the device itself becomes the “dongle.” The fact that the user has it — assuming it was not stolen or lost, in which case the thief would not have the password that connections will still require — is sufficient to establish that they are who they claim to be.
Better security
SMS is not a preferred method for authentication, according to no less an authority than NIST, the National Institute of Standards and Technology. NIST retracted its support for SMS-based MFA, recommending that “implementers of new systems SHOULD carefully consider alternative authenticators” and explicitly states that “OOB (out of band authentication) using SMS is deprecated, and may no longer be allowed in future releases of this guidance.”
NIST isn’t such a big fan of biometrics, either. While there is room for use of biometrics, the agency said in its latest authentication guidelines that in order for the system to be effective, it “shall be used with another authentication factor.” Biometric characteristics, said NIST, “do not constitute secrets. They can be obtained online or by taking a picture of someone with a camera phone (e.g. facial images) with or without their knowledge, lifted from through objects someone touches (e.g. latent fingerprints), or captured with high resolution images (e.g. iris patterns).”
Easier to use
As mentioned, push is a no-brainer – literally. There is nothing to remember, no action to be taken. Because of the system’s ease of use and superior security, most vendors of authentication technologies in recent years have improved their solutions to support push authentication. And push authentication is in line with industry standards such as PCI DSS, and is compliant with regulatory requirements such as HIPAA and GDPR.
Companies that provide push authentication as an option include RSA Security, SecureAuth, Microsoft Corporation, CA Technologies, Symantec Corporation, Vasco Data Security International Inc., Okta Inc., Ping Identity, Gemalto, Entrust Datacard Corporation, and HID Global Corporation.
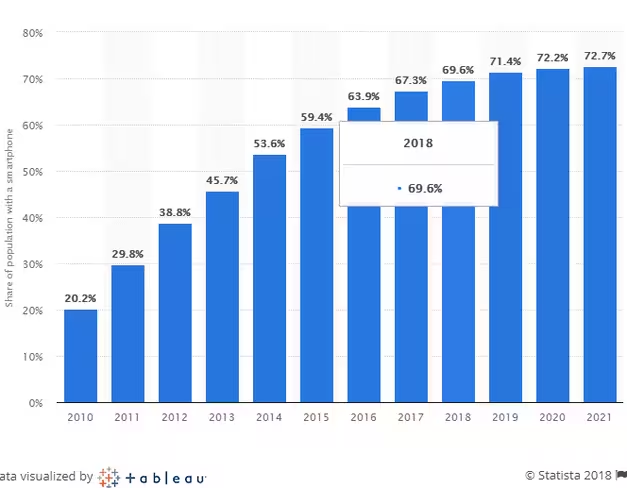 According to Statista, smartphone adoption rates will continue to rise in the next few years, meaning authenticator apps and phone-as-a-token MFA will likely continue to increase in popularity. Meanwhile, we are expecting to see SMS and software OTPs slowly become obsolete because they’re less secure and setting them up and employing them is more complex for users.
According to Statista, smartphone adoption rates will continue to rise in the next few years, meaning authenticator apps and phone-as-a-token MFA will likely continue to increase in popularity. Meanwhile, we are expecting to see SMS and software OTPs slowly become obsolete because they’re less secure and setting them up and employing them is more complex for users.
Other factors to consider when considering how to use push are how it will integrate into the organization; how users will respond to it; whether the solution is flexible enough to adapt to your organization’s network and server requirements; should push authentication be cloud-based, on-premises, or hybrid; whether you can (or should) drop passwords altogether and use password-less push authentication, together with another authentication solution such as biometrics; and, of course, the cost.
Of course, like with any other major move, research is needed, and organizations will have to decide how, and whether, push can help them be more secure. But given the history of data breaches – and despite the mountains of money thrown at the problem – security is getting worse, not better. Organizations that want to protect themselves really need to think out of the authentication box – and push may be just the thing they need.
Get the TNW newsletter
Get the most important tech news in your inbox each week.