Twitter has finally done the impossible: it’s allowing users to enroll for its two-factor authentication (2FA) program without requiring a phone number. What’s more, it’s also providing an option to disable SMS-based 2FA, which is known to be flawed and insecure.
The decoupling comes in the wake of revelations that the social blogging platform “accidentally” targeted ads at some users by way of their email addresses and phone numbers, which they provided only for account security purposes.
Twitter admitted it didn’t know exactly how many were impacted by the inadvertent error, but said the issue was fixed as of September.
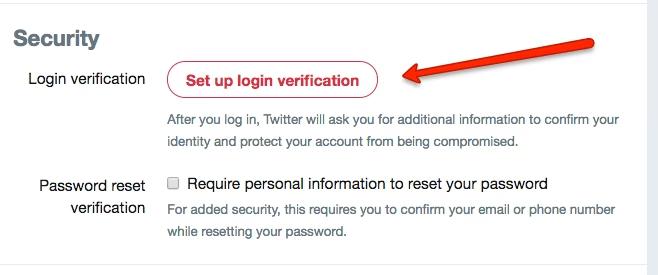
To setup your Twitter account for 2FA, all you need to do is download an authenticator app — such as Authy — that generates randomized six-digit one-time passwords to authenticate your identity when signing in. Another alternative is to use Yubico’s YubiKey.
2FA is the most effective means to safeguard your accounts from phishing and credential-stuffing attacks, where passwords stolen from previous data breaches are used on another site.
Although this can be done in a lot of ways — SMS, using an authenticator app, biometrics, or even a hardware security key — SMS-based verification has proven to be a risky proposition, what with a rising wave of SIM swapping attacks — thereby allowing cybercriminals to hijack the very SMS messages meant to keep your account safe.
We’re also making it easier to secure your account with Two-Factor Authentication. Starting today, you can enroll in 2FA without a phone number. https://t.co/AxVB4QWFA1
— Twitter Safety (@TwitterSafety) November 21, 2019
Things took a turn for the worse in September when hackers allegedly employed a SIM swap attack to gain access to the Twitter account of Jack Dorsey, the company’s CEO, after which it suspended the ability to tweet via SMS messages.
What made Twitter‘s 2FA setup even more egregious was the prerequisite that made phone numbers mandatory even if you were to use an authenticator app or a physical key for 2FA — effectively defeating the purpose of avoiding SMS-based authentication.
Other major sites, including Google, Facebook, and GitHub, don’t lock users into giving their phone numbers when turning on 2FA.
“Whose idea was it to use a valuable advertising identifier as an input to a security system. This is like using raw meat to secure your tent against bears,” cybersecurity expert Matthew Green tweeted following the incident.
Although adding a layer of SMS-based verification to your logins is better than relying on a password alone, it’s no longer the best way to do it. Viewed in that light, Twitter‘s decision to unlink the phone number from 2FA is a belated acknowledgement of the vulnerabilities associated with the SMS-based system.
Get the TNW newsletter
Get the most important tech news in your inbox each week.






