 A massive flaw in the way iPhone application Quip creates and publishes individual message links has enabled many enterprising internet users to successfully access and download images sent by users of the free MMS service.
A massive flaw in the way iPhone application Quip creates and publishes individual message links has enabled many enterprising internet users to successfully access and download images sent by users of the free MMS service.
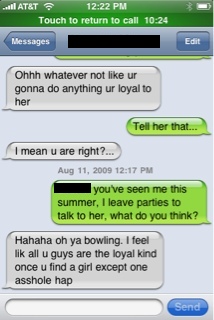
The 99¢ app allows iPhone users to send messages to other mobile phones for free and works by generating a URL appended with a five digit string of alphanumerics. The recipient simply follows the link or types it into their internet browser to view the picture in question.
Users on the popular social network Reddit worked out that if they typed in random five alphanumeric characters that followed the http://pic.quiptxt.com/ link, they would have access to hundreds, if not thousands of private messages.
Quip’s problems didn’t end there either. In a massive demonstration of the power of social networks, Reddit users set to work to create Quip specific scripts that would automatically enter the five alphanumeric characters and output sensitive and often adult images as a result.
Finally, Quip’s creators got involved, taking down their Amazon S3 storage account and all images stored with it. Their founder issued a statement to Reddit’s users saying:
Hello, this is Ish, the founder of Addy Mobile, makers of the Quip app.
As soon as this post came to our attention, we immediately shut down our servers. We have also now disabled all S3 access and have started to systematically secure all files in the system. We will not bring the system back up until we have adequate security around all files shared over Quip.
I apologize to our users for this security breach and promise we will do everything in our power to make sure none of their information is exposed once we bring the service back up.
The vision for Quip has always been to provide users a quick, simple, and affordable way for iPhone users to send picture messages without paying exorbitant carrier fees. We are a small company (3 people) but we will work as quickly as possible to bring back the service up in a safe and secure manner.
The key sentence in Ish’s statement is the insistence that the invasion of privacy was by way of a security breach, that simply wasn’t the case. The way the image URL’s were encoded was the problem, a fault of the creators not the people who accessed them.
Quip’s website is currently down and no images are being served. It didn’t stop a huge number of images being published elsewhere on different websites. There are no reports of anyone coming forward who could be identified in the compromised images but it could be a potential disaster for Quip if any charges are brought as a result of the “breach”.
We have embedded one below, one of the more tame images to illustrate the dangers of sending sensitive messages via a service such as this.
[Source – EverythingICafe]
Get the TNW newsletter
Get the most important tech news in your inbox each week.



