Windows 8 may block most malware out of the box, but there is still malware out there that thwarts Microsoft’s latest and greatest. A new Trojan variant, detected as Backdoor.Makadocs and spread via RTF and Microsoft Word document marked as Trojan.Dropper, has been discovered that not only adds a clause to target Windows 8 and Windows Server 2012, but also uses Google Docs as a proxy server to phone home to its Command & Control (C&C) server.
Symantec believes the threat has been updated by the malware author to include the Windows 8 and Windows Server 2012 references, but doesn’t do anything specific for them (yet). This is no surprise: the two operating systems were released less than a month ago but of course they are already popular, and cybercriminals are acting fast.
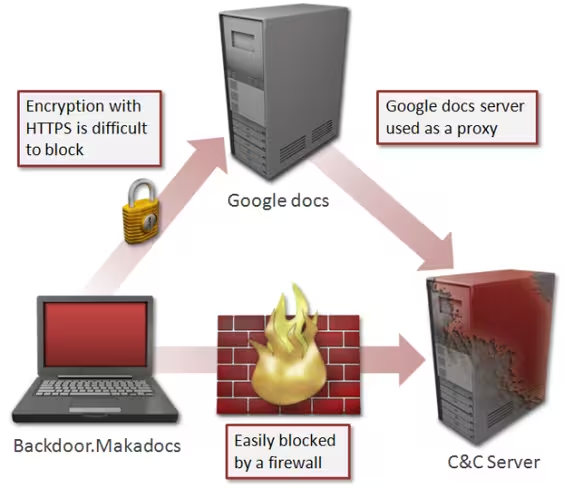
Yet the more interesting part is the Google Docs addition. Backdoor.Makadocs gathers information from the compromised computer (such as host name and OS type) and then receives and executes commands from a C&C server to do further damage.
In order to do so, the malware authors have decided to leverage Google Docs to ensure crystal clear communications. As Google Docs becomes more and more popular, and as businesses continue to accept it and allow the service through their firewalls, this method is a clever move.
The reason this works is because Google Docs includes a “viewer” function that retrieves resources of another URL and displays it, allowing the user to view a variety of file types in the browser. In violation of Google’s policies, Backdoor.Makadocs uses this function to access its C&C server, likely in the hopes of preventing the link to the C&C from being discovered since Google Docs encrypts its connection over HTTPS.
Symantec says “It is possible for Google to prevent this connection by using a firewall.” Since the document does not leverage vulnerabilities to function (it relies on social engineering tactics instead) it’s unlikely Google will be able to do much beyond participating in a game of cat and mouse with the malware authors.
Nevertheless, we have contacted Google and Microsoft about this issue. We will update this article if and when we hear back.
Update at 4:30PM EST: “Using any Google product to conduct this kind of activity is a violation of our product policies,” a Google spokesperson said in a statement. “We investigate and take action when we become aware of abuse.”
Update on November 19: “Social engineering is an industry-wide issue and we are aware these types of problems occur. We are committed to helping consumers have a safe, secure and positive online experience,” a Microsoft spokesperson said in a statement. “Our general guidance to customers is to exercise extreme caution when opening unsolicited attachments and links from both known and unknown sources and install and regularly update anti-virus software.”
See also – Security firm VUPEN claims to have hacked Windows 8 and IE10 and Microsoft’s security team is killing it: Not one product on Kaspersky’s top 10 vulnerabilities list
Image credit: Flavio Takemoto
Get the TNW newsletter
Get the most important tech news in your inbox each week.