A South Carolina woman says she was the victim of peeping Tom hackers last week when her WiFi-connected baby monitor was surreptitiously used to observe her and her baby in a bedroom.
The mother, Jamie Summit, wrote a Facebook post describing the incident in which her device, a FREDI Wireless Camera Baby Monitor, had been hacked and may have been used to spy on her while she slept or even breastfed her baby. In the post she says:
This afternoon I had the app pulled up and was watching Noah sleep in the bassinet in our room. I was in the living room with the only two people who had access (or so I thought) to the monitor. All of a sudden I noticed out of the corner of my eye that the camera was moving…and it was panning over to our bed. The exact spot that I breastfeed my son every day.

Summit says everyone who was supposed to have access to the baby monitor, through a smartphone app, was gathered in the room with her. It quickly became apparent a stranger was controlling the device.
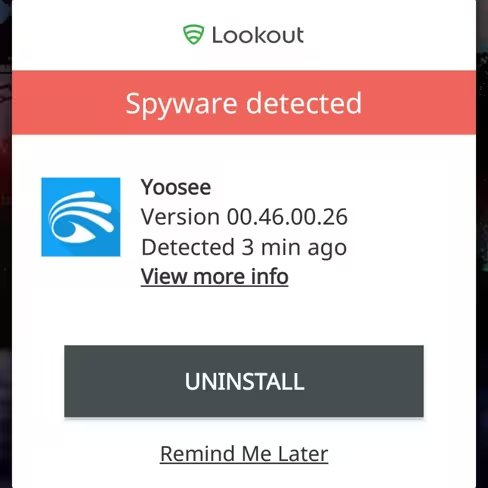
The FREDI baby monitor features motorized panning that allows it be turned remotely to point anywhere in a 360 degree rotation. It can be viewed and controlled entirely via one of two different smartphone apps — one of which Lookout security software flags as spyware.
The morning of the incident, Summit says, she awoke to notice the baby monitor was pointing at her, and not the bassinet where she recalled leaving it last. At the time, she assumed her husband had used the app to check on her, but later he explained he hadn’t accessed the app that morning.
Summit revealed she was distraught over the incident in her Facebook post:
I feel so violated. This person has watched me day in and day out in the most personal and intimate moments between my son and I. I am supposed to be my sons protector and have failed miserably. I honestly don’t ever want to go back into my own bedroom.
Tech industry insiders often take for granted that unsecured devices are wide-open portals for so-called “hackers” to exploit. These bad actors often need no special computer knowledge and can exploit vulnerable devices with nothing more than a web browser.
Summit says she bought the device on Amazon. When she reported the problem, the company gave her a contact number for the seller. But she says that number is disconnected and the seller won’t respond to her emails.
She told NPR:
I would have never, ever bought something if I thought it was this easy of a security risk. When I was making my baby registry, nobody warned me — no other mom said anything. It’s not common knowledge.
We reached out to the makers of the FREDI baby monitor but didn’t immediately receive a response.
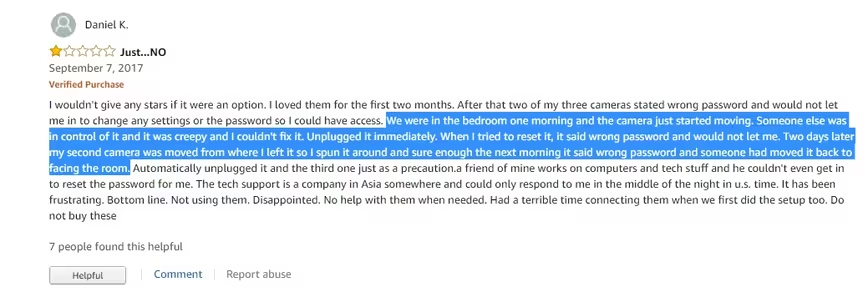
According to several reviews and answers on pages for the device on Amazon, Summit isn’t the first person to have a problem with voyeurs hacking this particular baby monitor.
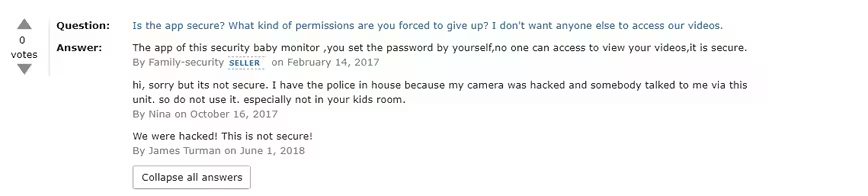
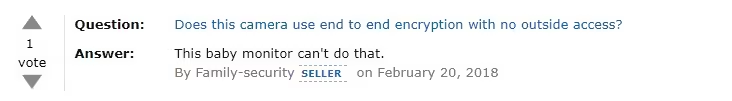
That isn’t to say it’s the only such vulnerable gadget: if you asked most experts they’d likely tell you to assume any device that can connect to WiFi is vulnerable to hackers. Unless you have well-researched reasons to believe the company that developed it engineered it to be secure, and continue to update that security as new threats emerge, you should probably treat it as an unsecured device.
In other words: assume the worst. Last year the FBI released a public service announcement informing parents of the dangers of WiFi-connected toys and gadgets. You can read the bureau’s safety suggestions here, and more about how to protect your family from hackers here.
In the meantime, make sure you change usernames and passwords immediately upon activating a new device, don’t use the same password twice, perform firmware updates immediately, and turn off any gadgets you aren’t using.
Get the TNW newsletter
Get the most important tech news in your inbox each week.






