Microsoft today announced the latest Internet Explorer 0-day flaw (CVE-2013-3918 will be fixed on this month’s Patch Tuesday. The patch will thus be released on Tuesday (tomorrow) at approximately 10:00 AM PDT.
On November 8, Security firm FireEye discovered a new IE 0-day flaw was being exploited in the wild. The company followed up with more details on November 10.
On every Thursday of every month, Microsoft reveals what security patches it will be releasing on every second Tuesday of the given month. November was no different, and the company today revealed that this particular flaw in question is indeed already slated to be patched.
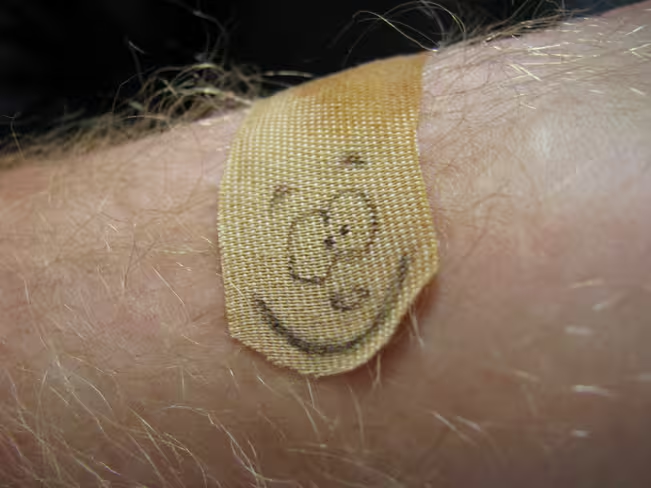
In other words, Microsoft has taken the time to test that it has already developed a patch for the IE flaw that is being exploited since Friday. Now that it is confident that the patch will address the issue in question, it can reveal that the fix falls under Bulletin 3 from November’s Security Bulletin Advance Notification.
Microsoft doesn’t reveal too much in its advance notifications so it doesn’t give away anything critical to criminals. We do, however, know that Bulletin 3 is for Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008, Windows 7, Windows Server 2008 R2, Windows 8, Windows Server 2012, and Windows RT.
In other words, this flaw is present in all supported versions of Windows and IE. It’s no wonder criminals have taken an interest in it, and they likely will continue to do so long after the patch is available.
Between then and now, however, Microsoft offers the following mitigations to prevent exploitation:
- Set Internet and local intranet security zone settings to “High” to block ActiveX Controls and Active Scripting in these zones.
- Configure Internet Explorer to prompt before running Active Scripting or disable Active Scripting in the Internet and local intranet security zones.
- Deploy the Enhanced Mitigation Experience Toolkit (EMET).
The first two options will help prevent exploitation but may affect usability, so Microsoft recommends that trusted sites be added to the Internet Explorer Trusted Sites zone to minimize problems. The third option can be turned on and off as needed.
Update on November 12: Microsoft has now released the fixes for this month’s Patch Tuesday.
“Bulletin MS13-090 addresses the publicly-known issue in ActiveX Control, currently under targeted attacks,” Dustin Childs, group manager of Microsoft Trustworthy Computing, said in a statement. “Customers with automatic updates enabled are protected against this vulnerability and do not need to take any action.”
Top Image Credit: Nate Brelsford
Get the TNW newsletter
Get the most important tech news in your inbox each week.