In 2016, attacks against vulnerable IoT devices featured prominently in the daily news headlines. Hundreds of thousands of IoT devices were used to build botnets and wage some of the largest DDoS attacks against organizations ever seen. Well, until a few weeks ago.
In other news, connected consumer devices ranging from teddy bears to webcams and home routers were found to be vulnerable with active compromises that exposed consumer personal information. The fact is that cyber attacks against or leveraging vulnerable IoT devices are rapidly increasing.
At this year’s TNW Conference, cyber-war veteran, Mikko Hypponen, spoke about the dangers and benefits of living in a smart device-centric world. From the largest ransom trojan to date to why all you’ll be forced to buy a smart dishwasher, here’s what the computer security expert has to say about the Internet of insecure things.
It’s my party and I’ll cry if I wanna
It’s been a busy week for Hypponen and his colleagues over at F-Secure. The WannaCry epidemic is was the single, largest outbreak of DDoS trojan. While these types of cyberattacks have been a major headache in the past, to date, they had never before affected so many in such a short amount of time.
This exploitation of device vulnerabilities is the perfect example of the biggest issues with IoT devices. Though patch information was made released earlier this year, only a handful of affected companies actually fixed the issue. Many others did not.
On the plus side – if there’s one – is that when you’re hit by a non-ransom trojan, you don’t know. With ransom trojans, as the name implies, there is a ransom along with the hijacking. Unfortunately, what the common person sees as a ‘hack’ isn’t the whole story. As Hypponen pointed out, when we casually see a display that’s not currently in working order, employees are looking at a much bigger problem.
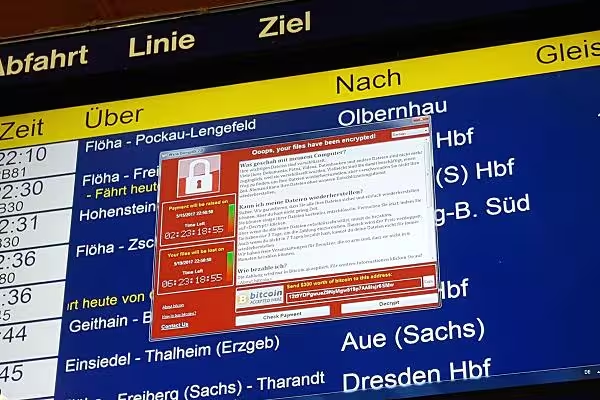
As you can see from the image below, WannaCry spread globally like wildfire, affecting over 150 companies worldwide.
As a traditional ransom trojan, hackers drop a component that encrypts files and demand payment to release the information.
As information and data became more sensitive, hackers began selling this info to the highest bidders. What made WannaCry so devastating was that hackers have since realized that the highest bidders of stolen data is usually the owner of said information.
This means industries from car manufacturers to hospitals to banks are now being targeted.
The burdens and benefits of blockchain
The first successful trojan was linked to a PO Box in Panama. Not too stealthy. However, with the advent of cryptocurrencies, modern trojans can now use these digital assets to make it hard to follow ransom attacks.
Hypponen stresses, however, that “this does not means bitcoin is bad. Bitcoin is just a tool.” Similar to hard-cash, it can be used for both good and bad.
But he also isn’t a bitcoin fanatic – understanding that it’s not bitcoin that will change the world, but the blockchain the currency is built upon.
Hypponen says that blockchain is the real innovation. While it may seem pretty obvious once people understand it, what makes it so innovative is because is “wasn’t obvious until after it was invented.”
Blockchain is just a way to structure data. The coding breakthrough, consisting of series of transaction blocks, allows competitors to share a digital ledger across a network of computers without need for a central authority. No single party has the power to tamper with the records. And those transactions are public forever.
But blockchain has only just begun to be explored, and potential applications to the Internet of Things and smart systems are vast, as the new data structure enables IoT devices to participate in transactions.
When your toaster’s more intelligent than you are
Some people hate the idea of everything becoming ‘smart’ as they fear that every day household appliances will become a privacy or security risk. Unfortunately, they’re not too far off. As time passes and more and more devices become connected to the network, it becomes more difficult to simply isolate or disconnect them.
But there won’t be any other options.
According to Hypponen, “in a decade, when you buy a toaster, it will be an IoT toaster. No one needs to know when their toast is ready.” The reason for this connectivity purely benefits the manufacturer.
The ability to collect data – how and how frequently products are used, how often they fail, etc – this is what’s valuable. It’s not extremely valuable, but it’s more valuable than the price of turning objects into smart devices.
Be smarter than your stove
Your traditional dishwasher already has vulnerabilities; connect it to the internet and be prepared to encounter very untraditional issues.
Why? Because developers are humans, and humans make mistakes. Humans are also lazy and uninformed.
Manufacturers expect users to configure everything from the time to a new password, but we don’t. We don’t read manuals, we don’t update security patches. There are also a plethora of questions left unanswered.
We don’t know how long the Cloud backend will be here. We don’t know how long the company will be around to pay their AWS bills.
Not to raise alarm here or anything, but I’m unable to turn off my #IoT oven ever since #s3 went down…
It’s getting kinda toasty in here
— P̶̻̖̯̗R͜O̥@ °.• ?? (@_pronto_) February 28, 2017
Despite the doom and gloom that could come with IoT, we’re just now on the dawning of the IoT age and thus can shape it into a more secure form of what we see today. But we must start preparing now.
We don’t care about smart toasters and we cannot rely on manufactures alone. If you can’t secure the device itself, you must secure them from the network via new hardware and a secure Wi-Fi, separate for your IoT devices.
Get the TNW newsletter
Get the most important tech news in your inbox each week.