
Recently, I got a text message from my credit card company, informing me about charges my husband made on the card we use for purchases on an extremely popular mobile shopping app. The charges originated from Bakersfield and Atlanta, and we had never been to either city.
Consumers often get credit card warnings like this, but because they originated from a mobile app purchase, I decided to download and analyze the app to investigate further.
What I found was pretty disturbing: Analyzing the source code, I realized that the user’s login information could easily be accessed, enabling a hacker to potentially extract credit card numbers and addresses. It’s my suspicion that our credit card info was hacked this way, and then sold on the black market to fraudsters.
Again, this occurred on one of the world’s most popular shopping apps, which earns over a billion dollars in sales every year.
Sales on mobile sites and apps< are increasing, especially during the holidays. As mobile purchases rise, so does credit card theft via mobile apps. Last year, credit cards were used in a staggering 53 percent of mobile commerce fraud, according to LexisNexis.
And according to recent research my own firm just conducted, 100 percent of mobile commerce- related Android apps on Google Play’s top 200 list are decomposable exposing them to the very kind of credit card fraud I experienced.
To help us all have a safer holiday shopping experience on our mobile devices, here’s a look at the key security threats that shopping apps face – and some advice for both developers and shoppers to better protect themselves:
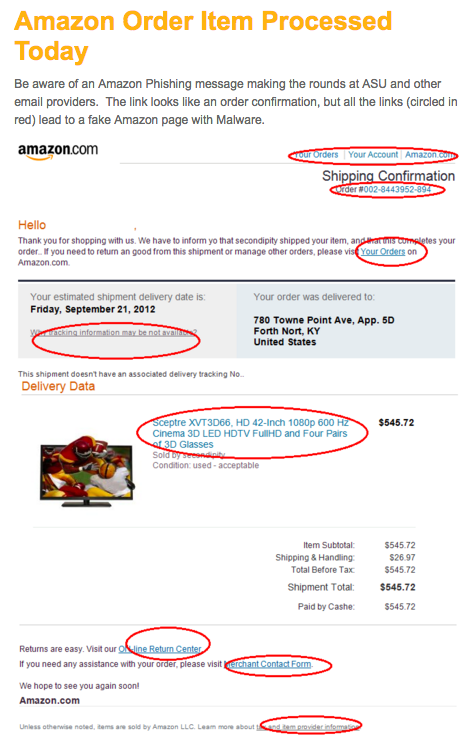
Phishing and smashing
“Phishing” is probably the most common hacking method, especially during the holiday season. Users get e-mails and text messages that contain a special (bogus) offer and a link to a compromised website. People click the link to what they think is a legitimate website, put in their credentials… and this data is secretly sent to the hacker’s server or bank account.
Similarly, “smashing” messages/texts, which include a malicious link, are also common. One smashing technique that’s especially common during the holiday season is the shipping notification. Everyone is excited about new deliveries, so the fake shipping notification works really well.
Malicious apps
During the holidays, we see a rise of malicious apps specially designed for shopping, downloadable through online websites, messages, or app stores. They may promise unprecedented pricing and hard-to-find products, but instead, steal users’ credentials and data, make charges to their accounts, or even take full control of their device.
In 2014, over 3100 potentially malicious mobile apps targeting Black Friday and Cyber Monday shoppers were detected. Many websites and app stores also offer popular games or holiday-themed games as freebies, but in reality, many of them spread malware. In 2013, thousands of malicious, dummy copies of Angry Birds and Grand Theft Auto 5 were found in Google’s Play Store.

Exploitation of login reuse
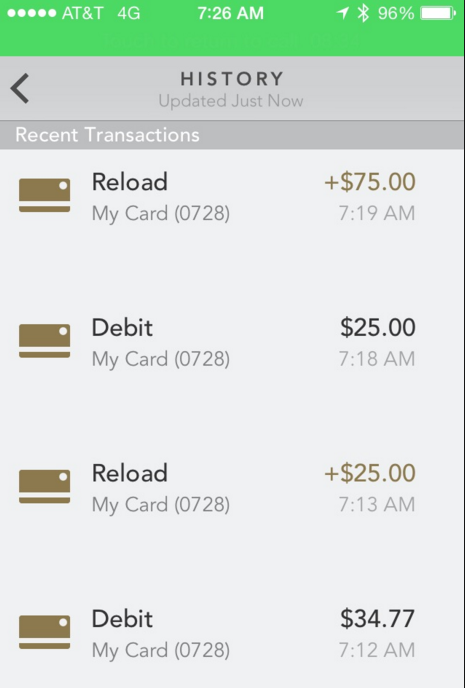
Mobile phone owners often re-use the same password on multiple sites and services, simply because it’s easier to remember one set for all of them. Unfortunately, this means that if hackers compromise one account, they can compromise many, if not all, of the users’ remaining accounts. This was especially disastrous in the case of the hacked Starbucks app, which prioritized usability and convenience at the expense of security.
The app allowed “auto-load” of money on the Starbucks card through customers’ linked credit card. Consequently, hackers who drained the account balance of a gift card were also able to steal more money from the linked credit card or bank account. Some Starbucks customers lost hundreds of dollars in a few hours.
The common practice of reusing logins can lead to chains of fraud across all the websites, services and apps which the same credit card is linked to.
How mobile developers can better protect their customers
The best security solution to avoid most hacking attempts is to avoid storing user login information locally, on the app. Instead, store them on a secure server. For similar reasons, communication tokens and keys should be encrypted and dynamically generated. You should also employ pre-emptive security measures to protect your app and source code – here are six reliable strategies.
Binary protection of the app to prevent source code analysis, reverse engineering and piracy is another good measure – particularly during the holiday season. As we saw with the bogus Angry Birds and GTA apps in recent holiday seasons, fake apps posing as your own often pop up, damaging your brand and trust, causing PR nightmares during the busiest shopping season of the year.
How mobile customers can better protect themselves
No app developer can protect its users 100 percent of the time, so it falls on mobile customers to take precautions of their own, especially during the holidays. Don’t click on links in messages sent from unknown people or companies. And if you are going to purchase something from a website that was sent through a text or e-mail message, first Google the URL to make sure it’s legitimate and hasn’t been flagged.
Related to this, only download shopping apps from legitimate app stores, such as Google Play and the Apple App Store, as they’re much less likely to have malicious apps than third party stores. But even Google and Apple are not entirely secure, so double check that the developer or app distributor is really the retailer, not a malware-infected false app.
Take a few seconds to read through the developer’s information to ensure you are downloading the right app and, when using it, be cautious about agreeing to unnecessary app permissions.
Finally, set up alerts to receive text messages for credit card charges as soon as they occur, especially during the holiday, and dispute any bogus charges immediately. As I recently learned myself, while even top retail apps aren’t totally safe from hacking, most credit card companies are interested in protecting customers whose apps have failed them.
Image credit: Shutterstock
Get the TNW newsletter
Get the most important tech news in your inbox each week.





