
Google has removed a fake Netflix app from the Play Store that aimed to spread malware by automatically responding to your WhatsApp messages.
Earlier this year, the security firm Check Point Research, found that an app named FlixOnline was assuming the look of Netflix, and promising two months of free subscription through WhatsApp messages.
However, a link attached to these messages would redirect you to a site to just capture your details, including your credit card.
Here’s how the malware worked. Once you installed the FlixOnline app from the Play Store, it asked for mainly three types of permissions: screen overlay, battery optimization ignore, and notification. Researchers from Check Point noted that overlay is used by malware to create fake logins and steal user credentials by creating fake windows on top of existing apps.
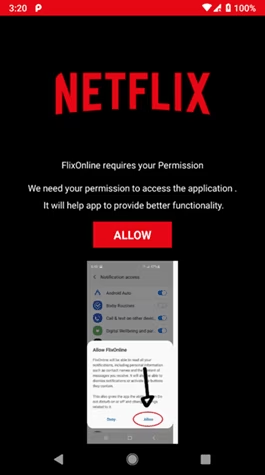
The app “listened” for notifications, and automatically replied to your WhatsApp chats with a message that looked like this:
“2 Months of Netflix Premium Free at no cost For REASON OF QUARANTINE (CORONA VIRUS)* Get 2 Months of Netflix Premium Free anywhere in the world for 60 days. Get it now HERE https://bit[.]ly/3bDmzUw”.
The link, of course, was a phishing page to collect your information.
Aviran Hazum, Manager of Mobile Intelligence at Check Point Software, said that this is a novel method of spreading malware, and while this app is removed from the Play Store, it could return in another form:
The malware’s technique is new and innovative, aiming to hijack users’ WhatsApp account by capturing notifications, along with the ability to take predefined actions, like ‘dismiss’ or ‘reply’ via the Notification Manager. The fact that the malware was able to be disguised so easily and ultimately bypass Play Store’s protections raises some serious red flags. Although we stopped one campaign using this malware, the malware may return hidden in a different app.
He added that this incident also indicates limitations of Play Store’s in-built protections and Google couldn’t detect malware in this app through its automated tools. Notably, WhatsApp doesn’t have any vulnerability that enabled this.
Attackers making applications and websites that masquerade Netflix is not a new trend. It was one of the most imitated brands for phishing attacks for Q1 2020.
FlixOnline app was live for two months and had nearly 500 installs before Google removed it last month.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




