![Ethereum bug causes integer overflow in numerous ERC20 smart contracts [Update]](https://media.thenextweb.com/2018/04/ethereum-integer-overflow.avif)
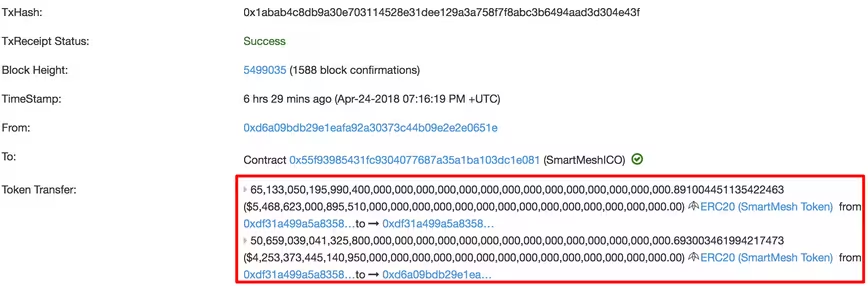
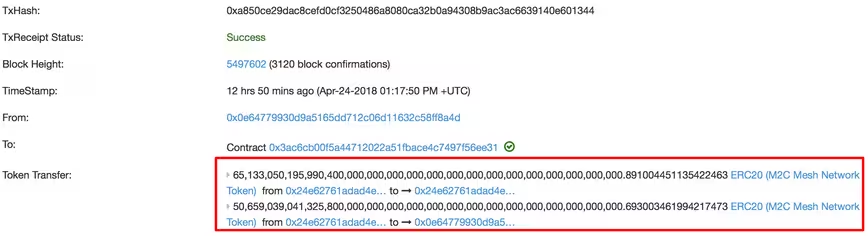
Blockchain security startup PeckShield has come across a critical vulnerability in multiple Ethereum smart contracts (based on the ERC20 protocol) which results in integer overflow – a common issue which occurs when computers deal with numeric values outside of the range that can be represented with a given number of bits.
The researchers have noted that their study found that the bug is present in a number of tokens, including UGToken, SMART, MTC, FirstCoin, GG Token, CNY Token, MESH and SMT tokens.
According to the researchers, the bug makes it possible for attackers to “transfer huge amount of tokens to an address with zero balance,” tacking the sender with huge fees in the meanwhile.
PeckShield remarks that while Ethereum has traditional mechanism in place to protect against such cases, it is of utmost importance to audit smart contracts thoroughly.
“A proper way to recover from these vulnerabilities and devastating effects requires coordination and support from all eco-system members, especially digital asset exchanges,” the company wrote. “In the meantime, we cannot over-emphasize the importance of performing a thorough and comprehensive audit of smart contracts before deployment.”
Cryptocurrency exchange desks like OKex and Huobi Pro already suspended ERC20 token trading for the time being.
“Meanwhile, we want to point out that certain affected tokens are still tradable on some exchanges (e.g., gate.io, HitBTC, YoBit, and CoinExchange),” the researchers added. “Note that the presence of non-centralized exchanges with offline trading services could pose additional challenges as they might not be able to stop attackers from laundering their tokens.”
This is not the first time researchers have come across bugs in Ethereum-based smart contracts.
Blockchain analysts have previously warned that there are over 30,000 glitchy smart contracts on the Ethereum Network.
In fact, a month ago popular cryptocurrency exchange desk Coinbase suffered from a similar issue which technically allowed users to reward themselves with practically endless amounts of Ethereum.
Those curious about the technicalities can read the full vulnerability report on the PeckShield site here.
Update 17:13 PM UTC: Some developers have since downplayed the severity of the vulnerability report in question, arguing that the faulty function outlined by PeckShield is not even present in the ERC20 standard – and rather an instance of poor Solidity development.
[H/T Oguz Serdar]
Get the TNW newsletter
Get the most important tech news in your inbox each week.