An online scammer is targeting the popular cryptocurrency, Dogecoin. To date, more than 10,000 individuals have been hit by the operation, with overall losses amounting to some $24,000.
Russia-based cybersecurity firm Doctor Web fingered the perp in a recent blog, spotted by BleepingComputer. Analysts have been tracking the suspicious activity of a particular cryptocurrency criminal, who has been using a wide array of malware and other methods to gain illegal income.
Security researchers bestowed our scumbag friend a few nicknames: Investimer, Hyipblock, and Mmpower.
I really like Mmpower, so let’s go with that one.
Trojan horses in all the fake Dogecoin things
Mmpower is not your average cryptocurrency scammer. They have actually manufactured an extensive set of fake online Dogecoin resources laced with credential-stealing malware.
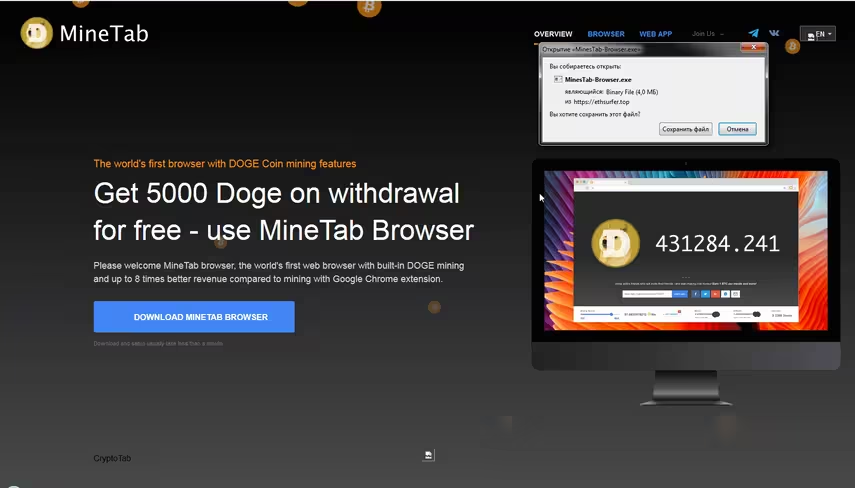
“The general scheme the cybercriminal uses to deceive Internet users is as follows: the potential victim is, by various means, lured to a fraudulent website that requires the user to download a certain client program to use it,” the analysts explain.
“However, instead of a client, the victim downloads a Trojan that installs other malware to the computer when the attacker signals it.”
Mainly, Mmpower uses Trojan horses to steal confidential data from Dogecoin fans, returning later to remove cryptocurrency and money from victim’s accounts.
The scam involves a fake cryptocurrency exchange that steals deposits, and a fake Dogecoin mining pool. There’s also a fake Dogecoin-mining browser extension, and one to earn Dogecoin when browsing the web.
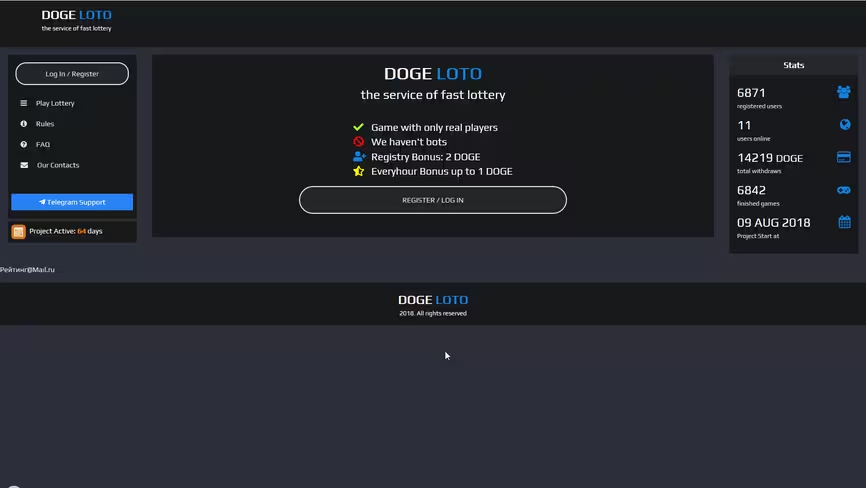
There’s even a fake Ethereum lottery that promises to pay winnings in Dogecoin, but is built in such a way that only allows the owner to win any money.
It currently has around 6,000 registered users. Go figure.
Dr. Web notes Mmpower uses a “wide range of commercial Trojans that are currently prevalent in the underground market.”
But most of the fake services are being hosted on servers that are Cloudflare protected, which hide IP addresses, keeping Mmpower anonymous.
This means there is currently little chance of identifying the fraudster and reporting them to the authorities.
Still, here is a handy guide on staying safe from phishers and other internet fraudsters. It’s worth reading, considering world-renowned cybersecurity team Group-IB has just detailed how cryptocurrency thefts are only going to increase over the next year.
The full list of compromised Dogecoin-related services operated by Mmpower are found here.
Get the TNW newsletter
Get the most important tech news in your inbox each week.