Leading cybersecurity unit Kaspersky Labs has warned hackers are “reprofiling” the world’s most well-known botnets en masse in order to spread their cryptocurrency mining malware as widely as possible.
A new security bulletin shows 2018’s significant decrease in Bitcoin price and investor interest hasn’t really correlated with a collapse in cryptojacking incidents.
Researchers also declared the legislative control flexed by world governments does little to curtail cryptojackers, as hidden mining malware is commonly found in countries where cryptocurrency like Bitcoin is outright illegal.
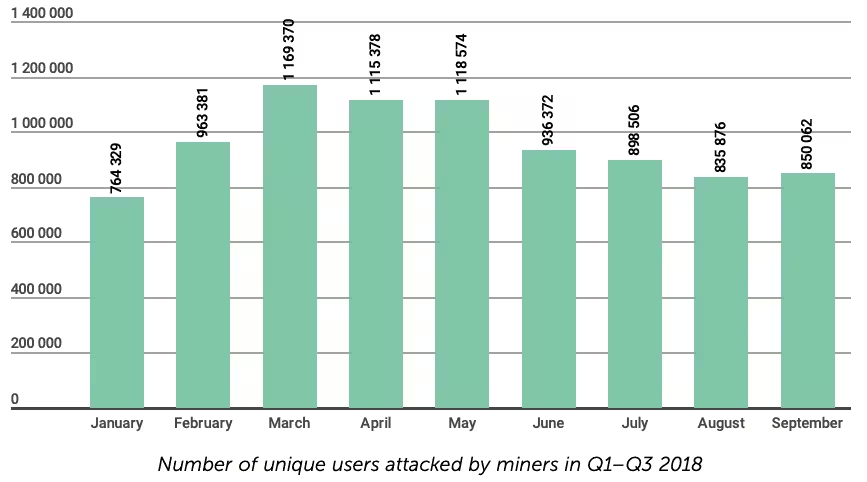
September sees cryptojacking uptick
While the number of unique users attacked by miners has certainly fallen from the market-fever earlier this year, September actually saw an increase for the first time in months.
Kasperksy notes the reprogramming of botnets has even led to a decline in DDoS attacks recorded in Q3 this year, as hackers deem cryptojacking to be more lucrative, and less competitive.
“This was induced not only by the high popularity of cryptocurrencies, but also the high competition in the “DDoS market,” analysts wrote. “[This] made the attacks less expensive for clients, but not for the botnetters themselves, who still have to cope with more than a few less-than-legal ‘organizational issues.'”
One example provided was the Yoyo botnet. The firm saw Yoyo is now launching way less DDoS attacks than before (despite the increase in activity early this year), with no data to suggest its owners (or authorities) had dismantled it.
Cryptojacking (and Monero) suits cybercriminals
Kaspersky elaborates on the allure cryptojacking holds for cybercriminals: they generally get away with it.
Researchers explain it can be practically impossible for the owner of an infected machine to realize they’re actively mining cryptocurrency. This greatly reduces the chances of the attackers coming into contact with cyberpolice.
They also maintain that Monero is still the most prevalent cryptocurrency among illegally mined coins, which can be generated from within desktop browsers using the standard computer processors of common laptops.
“This is due to its anonymous algorithm, relatively high market value, and ease of sale, since it is accepted by most major cryptocurrency exchanges,” reiterated Kaspersky. “For botnets mining this coin illegally, it is important that CPU resources can be utilized.”
A few months back, estimates suggested $250,000 worth of Monero was being mined every month through internet browsers, thanks to the supposedly neutral cryptocurrency mining script CoinHive.
Not long after, McAfee Labs revealed hackers had released 2.5 million different versions of the script in just three months.
You can’t legislate cryptojackers away
Kaspersky analysts unfortunately concluded that legislative control over cryptocurrencies “has little impact on the spread of hidden [cryptocurrency] mining.”
In fact, cryptojackers are even finding success in Algeria and Vietnam, where governments severely restrict or prohibit access to cryptocurrency under domestic law.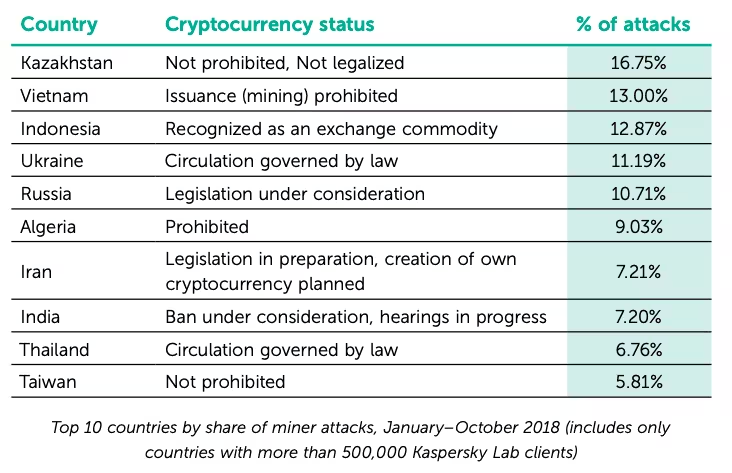
“Vietnam is [very high] in the rankings of […] countries by number of miner attacks, and Algeria is sixth,” the researchers highlight. “Meanwhile, Iran, which is presently drafting legislation to govern cryptocurrency and developing plans to issue its own ‘coins,’ is in seventh place.”
On the flipside, US internet users are the least affected by cryptojacking so far in 2018, suffering just 1.33 percent of the total number of attacks, followed by the Swiss (1.56 percent) and the British (1.66 percent).
The firm did find one realistic narrative in the trend: the more freely unlicensed software is distributed in a country, the more malicious cryptocurrency miners are found.
This reportedly lines up with other Kaspersky statistics, which showed malicious cryptocurrency miners commonly found their way into machines through pirated and unlicensed software.
Get the TNW newsletter
Get the most important tech news in your inbox each week.