
“Clear and present danger” — so suggests the authors of the recent National Infrastructure Advisory Council (NIAC) report to the White House, a task required by the administration’s May 2017 executive order (EO).
For those unfamiliar, the EO mandated government agencies to strengthen the cybersecurity of federal networks and critical infrastructure, and requested proof of compliance through a rigorous reporting process with tight deadlines.
The report ominously suggests the United States is in a “pre-9/11 moment,” a comment made by Mike Wallace, member of the NIAC, when discussing the potential of a catastrophic cyber attack against the U.S., the dire implications of which would result in a cyber equivalent to the impact of the 9/11 attack.
The authors take the federal cyber apparatus to task for not applying the necessary emphasis and diligence in securing the government’s networks and data at this late stage, and it’s hard to argue that critique. The NIAC’s report is one of the more comprehensive analyses of the state of the nation relative to cyber security preparedness, and its conclusions and recommendations are numerous and significant.
To apply the suggestions will require a mix of government, enterprise executive, and congressional actions. In the current milieu of politics, many of the important points from the report get lost, but the demand for immediate action doesn’t change. From the 45-page report, there are three things you should take away from it.
No agency is a model of cybersecurity proficiency
The report helpfully details top cybersecurity improvement recommendations for government agencies like the Department of Energy, National Security Council, Department of Defense, Department of Justice, and the FBI to name just a few. It’s clear no single agency is a picture-perfect role model of what federal cybersecurity maturity should resemble. The number one offender? The Office of Personnel Management (OPM).
While not named frequently in the report, given it doesn’t deal directly in critical infrastructure or assets, the OPM has suffered two breaches, one of which led by China, where my SSN, address and personal info were accessed along with five million other Americans. The federal government kindly gave us 10 years of credit monitoring, but the damage is done, and OPM’s reputation as a severely vulnerable federal agency dealing with highly sensitive personnel records is cemented.
What remediation looks like
According to the report, the federal government needs to facilitate a private sector-led pilot of machine-to-machine information sharing technology to test and monitor public and private data streams. The translation? The federal government and private industry need to start playing nicely, as the report suggests commercial enterprises will be the first line of defense against forthcoming catastrophic attacks.
The infrastructures of power and water distribution, both supported by private industry, are at risk, and ripple effects of a breach in those grids impacts the U.S. economy and its population’s safety. But, with hesitancy to share information given the government’s harsh regulatory mission (remember Apple vs. FBI?), private industry needs to know the government is willing to collaborate in a way that supports an enterprise’s standards before partnerships can be made.
The NIAC report recommends two options to help public and private sectors work together, one in the form of a tax incentive for using NIST Cybersecurity Framework (CSF)-based cyber risk controls, and the other in the form of lessened regulations for cooperative companies. Both are olive branches the government would do well to extend to enterprises in the coming months to begin this likely 20-year journey toward sufficient national cyber defense.
Consequences if improvements aren’t implemented
For commercial enterprises, the financial impact of cyber breaches has escalated dramatically over time. Two years ago, we witnessed the Target breach and the financial impact was extensive. The most recent cyber destruction incident, the NotPetya ransomware attack, created financial damages many times greater than the Target attack, which was previously thought to be the “mother of all breaches.”
The damages to Merck, FedEx, Maersk and others is reportedly well beyond $1 billion. Potential damage to the U.S. economy and the safety of our country’s population lies in the commercial market, the financial markets, and the power distribution systems: the nation’s first line of defense.
On the other side of the aisle, the negative impact a catastrophic cyber attack would have on the government would be ruinous. First and foremost, it’s important to recognize the government’s effectiveness is largely based on its citizens’ respect and support. When the government fails to protect critical data and infrastructure, that support is weakened and the government’s ability to operate with the trust of its constituents slowly fades.
There is a great deal of effort from the federal government to protect the infrastructure and critical public services from cyber threats, magnified most recently by Hurricane Harvey’s destructive impact in Texas, and the potential for Hurricane Irma to do the same in Florida.

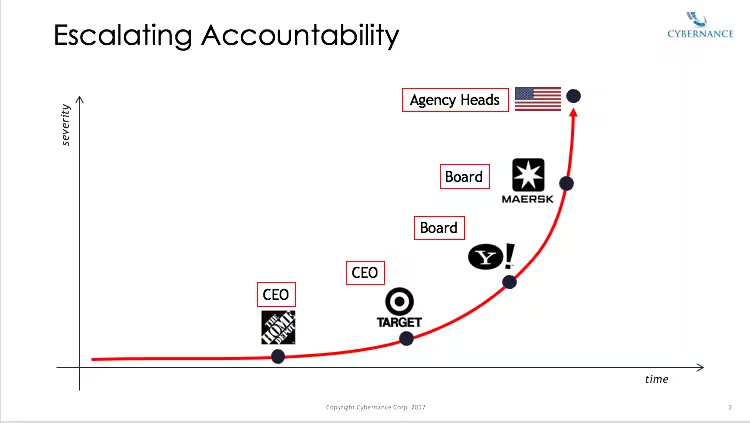
Historically, enterprise management and boards of directors have sought solace from business and personal risk based on Delaware’s “reasonable business judgement” law. It proposes that actions executed by a reasonable person of sound mind, and based on the facts they have access to at a given point in time, are justified, therefore protecting business leaders from personal liability.
Cyber risks are now so strongly emphasized, with reports like NIAC imploring the public and private sector alike to make massive improvements and cyber experts desperately seeking support in what they call a “pre-9/11” moment, that no executive or board member can deny the awareness of risk.
With the cybersecurity EO, government agency heads will now be held financially and operationally responsible for any cyber breaches. These long-time-coming consequences are serious, making it high-time enterprises and the government work together to elevate our nation’s cyber defense.
Get the TNW newsletter
Get the most important tech news in your inbox each week.




