
A Chinese threat actor, known to have perpetrated a series of state-sponsored espionage attacks, has been covertly staging financially motivated activities targeting the video game industry.
According to security firm FireEye, the cyber threat group — dubbed Advanced Persistent Threat 41 (APT41) — is unique in that “it leverages non-public malware typically reserved for espionage campaigns in what appears to be activity for personal gain.”
While the group appears to have been active at least since 2012, the public disclosure suggests that its twin motivations became apparent from 2014 onward.
Called Barium or Winnti by other companies, APT41 has been previously linked to various supply chain compromises targeting Asus, NetSarang, and CCleaner utility in recent years.
Balancing espionage and financially motivated attacks
APT41 is said to have launched several intelligence gathering campaigns ahead of crucial political events and strategic business decisions, with focus on verticals like pharma, healthcare, retail, education, and virtual currencies.
The group has gone after companies located in at least 14 countries, including France, India, Singapore, South Korea, the UK, and the US, reflecting the global nature of the attacks.
In addition, it’s also consistently targeted the video game industry — development studios and publishers — directly and via supply chain compromises, even as the group moved away from stealing intellectual property in 2015 following a historic Sino-US agreement that put an end to cyber-enabled theft for commerical gain.
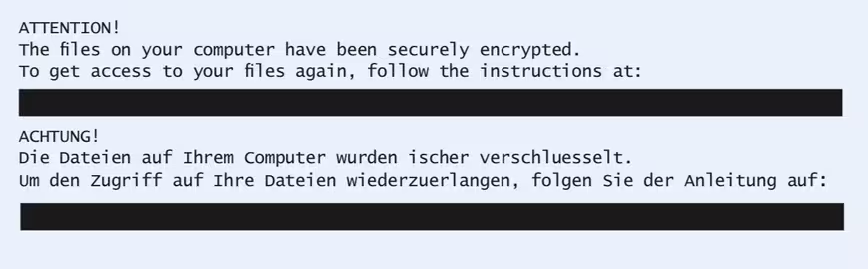
Per FireEye, the threat actor attempted to steal data from a healthcare company while also simultaneously deploying ransomware at a game development studio.
The campaigns work by injecting malware into legitimate video game software from third-parties, which are subsequently distributed to victim organizations.
Furthermore, APT41 has leveraged a variety of tactics — spear-phishing, bootkits, capturing server credentials, and using compromised digital certificates from game studios to sign malware — in order to gain access to development environments and distribute malicious code.
Interestingly, while the modus operandi infected thousands of systems, the hackers ultimately take advantage of the intrusion to target specific individuals, the researchers noted.
Once inside the environment, it exploits custom-made tools to gain elevated access to systems and generate tens of millions of dollars in the game’s virtual currency, which is then most likely sold in underground markets. Failing the objective, the group is also said to have deployed ransomware to collect money from the victim.
A do-it-all hacking group
What’s more, APT41 has proven to be something of a resourceful adversary, gaining capabilities to steal call record information from telecom companies, and identify dissidents in China.
The findings come close on the heels of similar disclosures by F-Secure and IBM, which have warned of increased malware attacks on financial institutions, infrastructure, and state-run facilities.
“APT41’s links to both underground marketplaces and state-sponsored activity may indicate the group enjoys protections that enables it to conduct its own for-profit activities, or authorities are willing to overlook them,” the researchers said. “These operations underscore a blurred line between state power and crime that lies at the heart of threat ecosystems and is exemplified by APT41.”
Get the TNW newsletter
Get the most important tech news in your inbox each week.




